Managing security across multiple entry points creates overwhelming complexity. Traditional access control systems operate in silos, forcing security directors and IT managers to monitor disparate, non-communicating platforms.
This fragmentation leaves gaps in coverage, making it nearly impossible to maintain comprehensive oversight of who enters your facility and when. Industry reports show the “human element” is a factor in 68% of breaches, a risk amplified by siloed systems.
These security blind spots expose your organization to unauthorized access, compliance violations, and reputational damage.
Every disconnected system is a vulnerability for malicious actors to exploit. This is confirmed by an IBM finding that 40% of breaches involved data stored across multiple environments, which are the kinds of visibility gaps created by disconnected security systems.
However, integrated building access control systems solve this by unifying all security components onto one centralized platform. This provides complete visibility and control over your entire security infrastructure. Below, we explain what integrated access control is, how it works, and why it is the practical choice for modern facilities.
What is an Integrated Access Control System?
An integrated access control system is an advanced security solution that unifies access control with other security technologies, such as VMS, intrusion alarms, video surveillance, and fire detection.
Instead of managing each system separately, you can monitor and control everything from one central platform. This integration simplifies operations and strengthens overall security by providing real-time visibility into who is entering or leaving, while linking incidents directly with other security solutions.
For organizations, it means enhanced protection of people, assets, and facilities, improved response to threats, and an efficient approach to managing building security.
Benefits of Integrated Security Systems
An integrated system brings all your security platforms under one roof, making management easy and efficient. Beyond stronger security, integrated security solutions save time and reduce costs. Here are the principal benefits.
- Centralizing Management
Integrated building access control systems consolidate management onto a single platform, eliminating the need to juggle multiple interfaces for video, intrusion detection, and door controls.
Administrators can manage user credentials, access levels, and security policies across all connected systems from one central dashboard. This centralized approach reduces operational complexity and administrative overhead.
Consequently, security personnel can perform their duties more efficiently and ensure a faster response to routine tasks and potential incidents.
- Offering Customization and Flexibility
A centralized platform gives you a solid foundation for customization, flexibility, and growth. It lets you set precise access rules based on role, time, location, or threat level. This way, permissions match your exact needs.
As operational needs change, such as reconfiguring access for a new building wing or creating temporary credentials for contractors, you can quickly adjust.
As your organization expands, the system scales with you. This makes it easy to add new doors, readers, or security technologies without overhauling your entire setup.
- Enhancing Security
This interoperability facilitates a more proactive security posture by enabling systems to work in synergy. For instance, consider an unauthorized attempt to enter a secured server room after hours. The access control system instantly denies the credential and triggers an alarm.
Simultaneously, it prompts the integrated video surveillance system to record and pull up live footage. This provides security staff with immediate visual verification and eliminates the need to cross-reference siloed data, thereby delivering contextual information at a glance.
Security personnel can then make informed decisions, dispatching the appropriate response based on confirmed visual evidence.
- Simplifying Data Collection and Reporting
When systems are combined, data collection becomes seamless and efficient: door activity, video triggers, and alarm alerts all feed into one centralized log. This removes the need for manual cross-checking and reduces errors.
From there, built-in reporting tools can quickly analyze the data, identify patterns, support compliance audits, and generate detailed activity reports in just a few clicks. The result is clearer insights that make security planning easier and more strategic.
- Complying with Regulations
Adhering to industry-specific regulations, such as HIPAA or SOC 2, is essential for any business. Integrated building access control systems simplify compliance by creating an auditable trail of all security activities.
You can generate reports showing who accessed sensitive areas, when they did, and the corresponding video evidence.
Automated features also help enforce policies, such as mandatory door locks during specific hours or dual authentication for high-risk zones. Thus, they reduce compliance risk and streamline the audit process.
Key Components of an Integrated Access Control System
From access credentials to cloud-based management, each component works together to secure access points. These elements ensure only the right people gain entry when and where they should.
Access Credentials (Cards, Biometrics, Mobile Apps)
Advanced integrated access control systems rely on various credentials to verify identity. They serve as the unique digital keys to your building and can range from keycards and fobs to fingerprints, PIN codes, and smartphones.
Each credential stores a unique identifier assigned to a specific individual. For heightened security, these unified security platforms often support multi-factor authentication, which requires presenting two different credential types to gain entry.
This crucial layer ensures that a compromised single credential alone will not open the door. Stolen or compromised credentials remain a common initial attack vector, accounting for 16% of incidents in industry analysis. Therefore, tying credentials to stronger, centralized controls is critical.
Multiple authenticators strengthen your comprehensive building security system by tying access to verified identity alone.
Access Control Software
Acting as the central nervous system, the access control software is the dashboard that powers every unified security platform. From this single interface, administrators comprehensively manage the entire operation by:
- Configuring user permissions
- Enrolling credentials
- Establishing precise rules (who can enter which areas and when)
This management hub is hosted on-premises or in the cloud, and connects to all door hardware and readers across your facility. It provides real-time visibility, displaying live events as they occur for immediate monitoring and response.
Furthermore, every access attempt is meticulously logged, creating an audit trail for compliance reporting and security reviews.
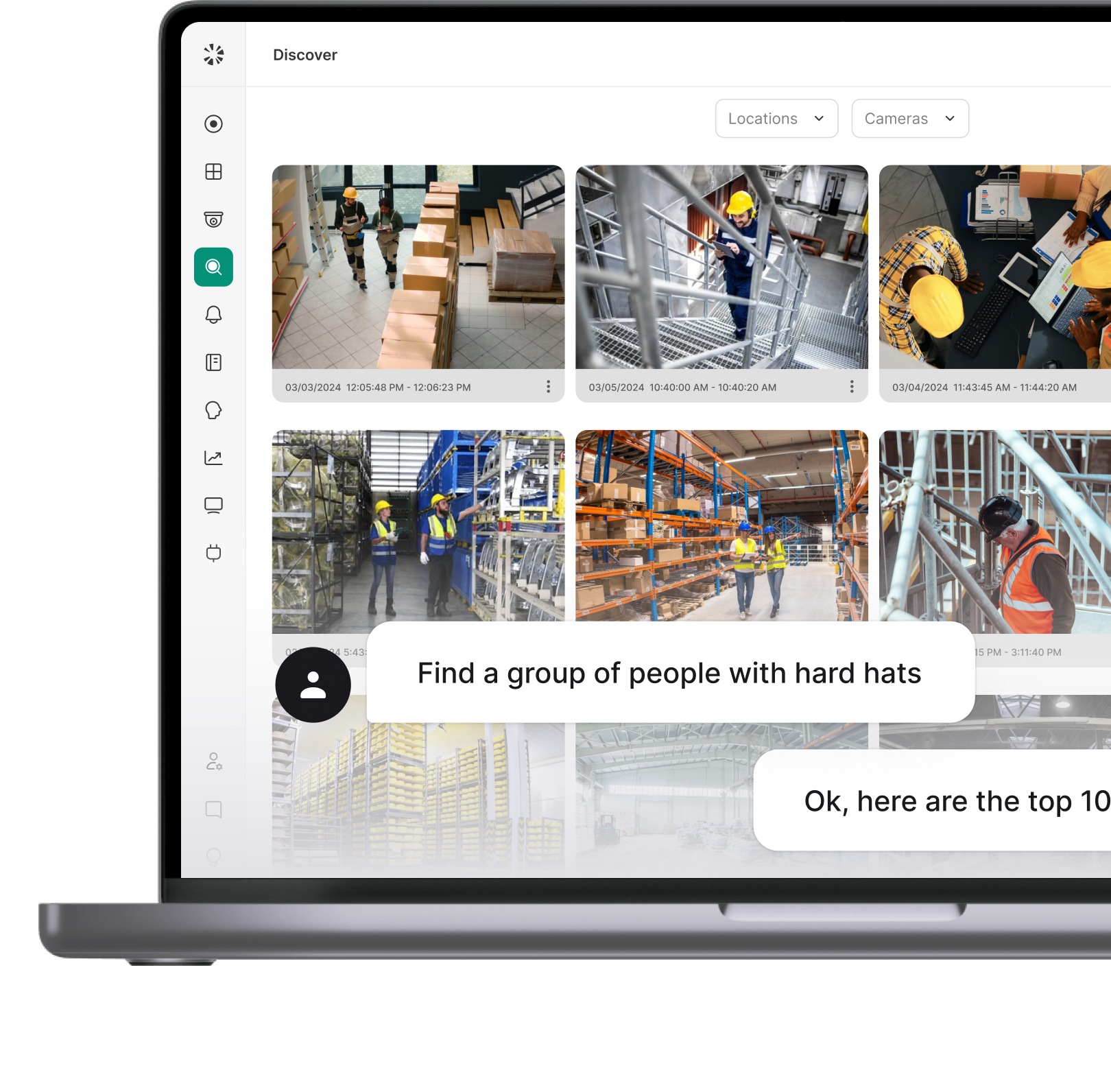
Video Surveillance Integration
Video surveillance integration is the crux of integrated access control systems, linking camera feeds with door events to provide instant context for security incidents. When cameras are tied to access points, security officers can review synchronized video clips for every card swipe, failed credential, or forced-entry alarm.
This speeds up verification and investigation in real time and results in reduced false alarms. Integrated building access control systems also support automated rules, such as auto-focusing cameras on an activated door, so operators don’t sift through hours of footage.
Combined video and access logs simplify audits and compliance by producing consolidated trails of who entered, when, and what was recorded. Scalable systems let you add cameras and storage without disrupting operations.
Alarm Systems and Sensors
Alarm systems and sensors form the immediate detection layer in integrated access control systems. Door contacts, motion sensors, glass-break detectors, and environmental sensors (smoke, flood) feed real-time signals into the central platform, allowing rules to correlate alarms with access events.
Integrated alarms can automatically lock or release doors and send location-aware alerts to security staff and first responders. This reduces response times and eliminates guesswork from incident handling.
Centralized alarm management streamlines incident workflows, supports compliance reporting, and reduces false positives through cross-system validation.
Cloud-based Management
Cloud-based management modernizes how firms integrate access control by centralizing configuration, monitoring, and updates in the cloud from any location. This approach eliminates the need for costly on-premise servers and allows security directors to:
- Manage door permissions
- Review access events
- Update credentials remotely via a secure web browser
The platform scales to accommodate new sites or users, making it ideal for managing multi-location operations within a single, unified security platform.
Automatic software updates guarantee your comprehensive building security system is always running with the latest features and security patches. This component fortifies security and facilitates compliance auditing through centralized data management.
How Coram Integrated Access Control Works?
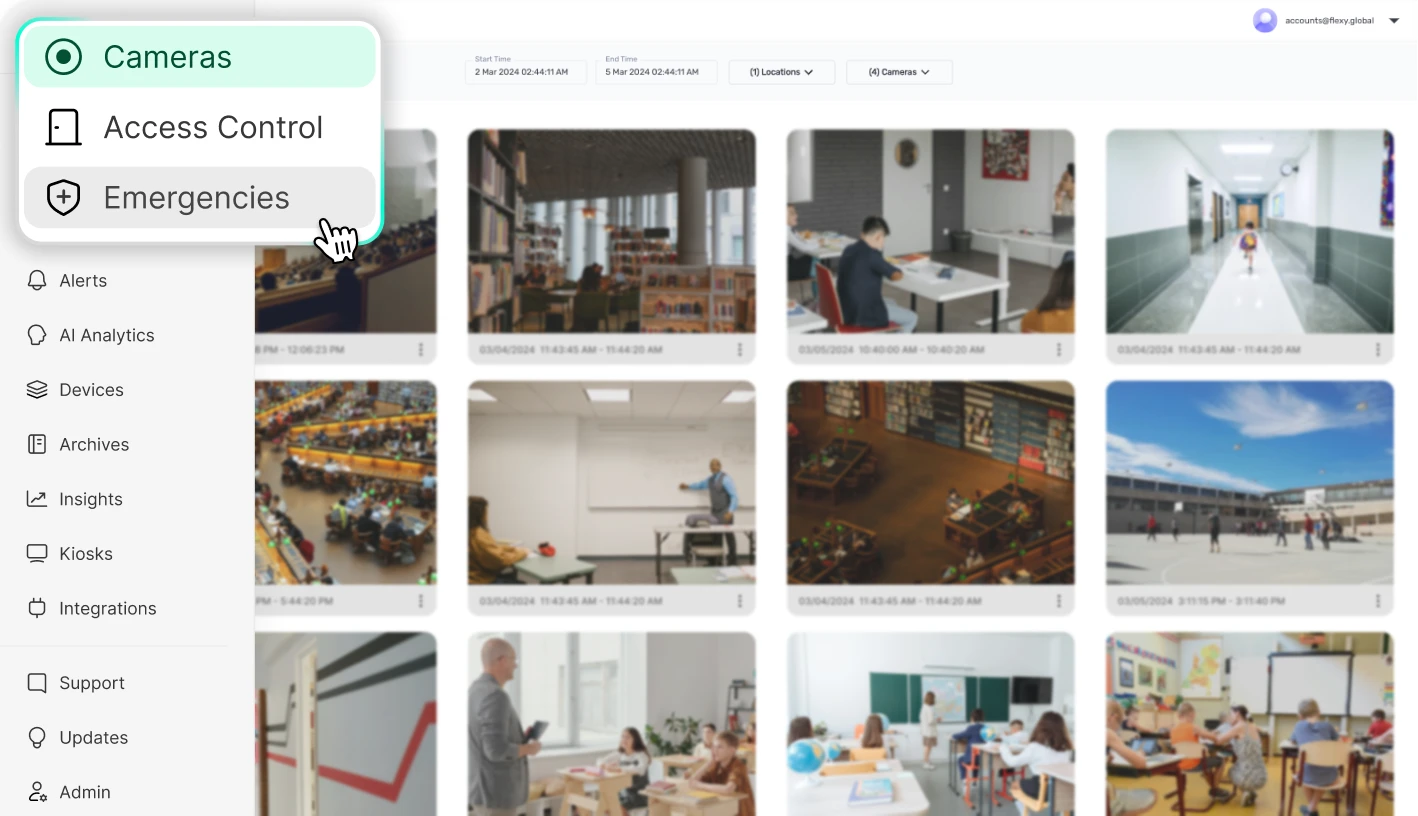
Coram’s integrated access control system is designed to simplify how businesses secure their facilities while giving administrators full visibility and control. At its core is a centralized access control board that connects to every door in your building.
Each door is equipped with a card reader, and when an employee or visitor badges in (or uses their mobile phone via Bluetooth), the system immediately communicates with the access control board.
Coram’s software performs real-time credential checks to determine whether the user is authorized to access that specific door. Once verified, the control board instructs the door to unlock.
Whether entry is granted or denied, the attempt is logged in the cloud, creating a reliable record of who accessed what and when.
Key Features
Here are other features that complement how Coram’s integrated access control works.
- Cloud-based Management and Customization
Because the system is cloud-based, businesses save on the cost and complexity of maintaining local servers. This cloud connection also makes Coram highly customizable. Administrators can define access rights down to the individual level, deciding which employees or visitors can enter certain areas, at what times, and under what conditions.
Access can be granted or revoked instantly, and custom schedules can be set to automatically lock or unlock specific doors during business hours, after-hours, or for special events.
- Integration with Video Surveillance System
Coram does not stop at access control; it integrates with video surveillance to strengthen security further.
If someone tailgates through a door or attempts unauthorized access, the system pairs door activity with camera footage, providing instant alerts and audit trails.
- Scalability and Offline Access
Scalability is another key advantage. Whether managing one office or multiple facilities across regions, Coram adapts effortlessly to organizational growth.
In cases of power or network outages, the system retains local access permissions and offers backup power. This ensures operations continue without disruption.
Conclusion
Integrated access control systems transform fragmented security operations into unified, efficient platforms that deliver comprehensive protection across your entire facility.
By consolidating video surveillance, alarm systems, and access management into one centralized dashboard, these solutions eliminate security blind spots while streamlining administrative overhead.
The benefits extend beyond enhanced security to include simplified compliance reporting and real-time visibility that enables quick incident response. With consolidated logs and automated rules, teams reduce false alarms, meet compliance requirements, and make data-driven security decisions.
Coram’s cloud-based integrated access control system delivers that by centralizing operations, eliminating silos, and securing assets. Book a free personalized demo with a Coram expert today.
FAQ
Integrated access control differs from traditional systems in that it combines several security functions, such as video surveillance, VMS, and alarm systems, into a unified platform. However, traditional access management systems operate as separate, siloed solutions.
Yes, integrated access control can work with your existing cameras and alarms; however, this depends on compatibility with your framework and hardware.
With integration, you can automate responses to incidents, centralize management, and connect credentials to video and alarm systems. All these improve general security by offering a more holistic and efficient system.
Cloud-based integration can be more secure than on-premise, as providers invest in advanced, multi-layered security measures and dedicated security teams that most businesses cannot match.
On the other hand, on-premise integration gives businesses full physical and digital control, which may be preferred for sensitive data or strict compliance standards. The most secure option ultimately depends on an organization’s specific needs, available resources, and expertise.
The cost of an integrated system ranges widely, with no fixed average price. It depends on factors such as:
- Custom development needs
- The use of cloud or legacy systems
- Vendor pricing models
- The availability of skilled personnel
- Whether integration is point-to-point or platform-based
- The number and complexity of systems
Healthcare, pharmaceuticals, and law enforcement use integrated access control to meet regulations, protect sensitive data, secure high-value assets, and prevent hazardous events.
Manufacturing and logistics rely on hands-free systems to improve efficiency for workers handling equipment. Banking and finance use it to reduce fraud, while education and government implement it to strengthen security and maintain compliance.




%20(8).webp)