Over the past 5 years, 60% of organizations have reported breaches in their physical security systems, with the average incident costing nearly $100,000 to resolve.
Too often, physical security is mistaken for a checklist exercise - locked doors, surveillance cameras, and alarm systems. While these are essential, they only address surface-level protection.
Effective security demands a deeper, proactive approach, one that evolves with operational changes, facility layouts, and shifting business dynamics. Even a seemingly minor issue, a broken stairwell light, an unlocked service gate, or an outdated evacuation plan, can turn into a serious vulnerability waiting to be exploited.
This is where a physical security risk assessment becomes indispensable. Beyond the basics, it uncovers hidden blind spots and equips organizations with strategies to mitigate risks before they escalate proactively.
In this article, learn how a structured risk assessment strengthens your defense, protects your people & assets, and keeps your organization a step ahead of potential threats.
What is a Physical Security Risk Assessment?
A physical security risk assessment is a structured process used to evaluate the safety and resilience of an organization’s physical environment. It goes beyond simply checking locks and cameras; it’s a comprehensive review of all potential risks to your facilities, people, and assets.
Also known as a physical security audit, this assessment involves a comprehensive review of security policies, procedures, and infrastructure of offices, warehouses, production plants, retail locations, and other similar facilities. A thorough evaluation may further include
- on-site inspections,
- testing business security systems under different conditions,
- and interviewing staff to uncover gaps in awareness or response.
Typical risks assessed range from burglaries and vandalism to natural disasters, workplace violence, and internal theft.
For example,
- A physical security risk assessment might uncover outdated access control systems that still rely on easily duplicated keycards, leaving facilities vulnerable to unauthorized entry.
- It could also reveal blind spots in CCTV coverage where critical areas remain unmonitored, creating opportunities for theft or misconduct.
- In some cases, the assessment may identify poorly defined or insufficient emergency response protocols, meaning employees may not know how to act during a fire, intrusion, or natural disaster, putting both people and assets at risk.
What Happens During A Physical Risk Assessment?
A physical security risk assessment usually follows a systematic approach that covers both people and infrastructure. It's a structured physical security audit where every layer of protection is tested for strengths and weaknesses.
Policy and Procedure Review
The assessment begins with examining your organization’s existing security policies, such as access control systems, visitor management, incident response plans, employee protocols, etc.
An auditor also checks if emergency exit procedures are well-documented and if staff are trained to follow them. The goal is to identify any gaps, inconsistencies, or outdated measures. An auditor will then provide tailored recommendations to strengthen these practices.
Inspection of Physical Premises
Next, the auditors evaluate the building itself, including its construction, layout, lighting, entry points, and landscaping. Weak spots such as poorly lit areas, unsecured entrances, or obstructed sightlines are flagged, with suggestions for upgrades like reinforced barriers, improved illumination, or redesigned access routes.
Testing of Security Systems
Technology is only effective when it functions reliably. Auditors now test technologies such as electronic locks, surveillance cameras, alarm systems, and monitoring software to confirm they are operational and up to standard.
If outdated software or faulty cameras are found, the assessment provides practical steps to upgrade them before they become liabilities.
Employee Awareness and Training
Human behavior is just as important as physical barriers. Employee interviews are conducted to understand their adherence to security protocols and their preparedness for emergencies.
In this step, the auditors from physical security risk assessment companies often uncover human-factor risks, such as a lack of awareness about phishing attempts, tailgating threats, or response procedures during a breach or natural disaster. Training recommendations are provided to build stronger preparedness.
How to Conduct Physical Security Risk Assessments
1. Develop A Plan and Define Its Scope
Begin your physical security risk assessment by defining its scope. Decide which sites, assets, and facilities will be included. Whether the goal is compliance, asset protection, or strengthening overall security, setting objectives helps measure the effectiveness of the assessment. It also provides efficient use of resources and forms the foundation for an effective physical security audit.
2. Identify Threats and Vulnerabilities
Once the scope is set, the next step is to identify the specific threats and vulnerabilities that each facility faces. This process begins with a thorough audit of the location, examining both internal and external risk factors. For example,
- Consider the number of entrances and exits - are they properly secured to prevent unauthorized access while still allowing safe evacuation during emergencies?
- Staffing is another key element; understaffed facilities may become more prone to operational risks and oversight gaps.
- Geography also plays a role in risk assessment. Facilities located in high-crime areas, regions prone to terrorism, or zones vulnerable to natural disasters such as floods, tornadoes, or wildfires face heightened security challenges.
- It’s equally important to review access management policies, confirming that former employees or contractors no longer retain access privileges. Additionally, basic safety measures, like hazard signage and emergency plans, should be reviewed for adequacy.
Threats can be identified through site visits, structured interviews with management and staff, and on-site inspections. By compiling this information into a centralized document or spreadsheet, organizations gain a clear picture of vulnerabilities, allowing them to prioritize resources and strengthen security measures effectively.
3. Assess Impact and Likelihood
The next step is to evaluate both their potential impact and the likelihood of occurrence. This helps determine where to prioritize resources for the greatest improvement in your security posture.
Like, a facility located in a high-crime area may face a greater probability of theft. At the same time, one in a flood-prone zone may have a lower likelihood of crime but higher exposure to natural disasters.
Traditionally, organizations have relied on qualitative methods, such as rating risks on a scale from low to high or using color-coded severity charts. While these approaches offer a broad view, they can sometimes oversimplify complex risks. A more effective method is risk quantification, which ties each potential threat to measurable consequences, particularly financial costs. This allows organizations to evaluate not only the likelihood of an event but also the scale of operational disruption, safety concerns, and monetary loss it may cause.
By combining likelihood with impact, decision-makers gain a clearer understanding of which risks demand immediate attention and which can be managed with minimal resources.
4. Review The Current State Of Your Physical Security
Identifying risks is only half the job; knowing whether your existing defenses can actually withstand them is what truly matters. This step is about taking a clear, unbiased look at your current physical security setup to see if it’s strong enough or if it’s leaving dangerous blind spots.
Key areas to evaluate include:
- Access control - Do former employees still have keys, codes, or badges that were never revoked? Are access levels properly aligned with employee roles?
- Facility protection - In high-risk or conflict zones, are fences, barriers, and on-site security professionals in place to control entry points?
- Emergency readiness - Are environmental threats like floods or severe weather being monitored, and do you have evacuation or continuity plans in place?
A structured physical security audit at this stage helps confirm that existing measures are not just in place but effective. Any gaps discovered here form the foundation for stronger, smarter risk mitigation.
5. Implement or Update Mitigation Measures
Once the weak points in your physical security are clear, the next step is to close them with the proper mitigation measures. Identifying gaps is only valuable if you act on them. This is where strategy turns into execution, not just to fix vulnerabilities, but to create layered defenses that adapt to evolving risks.
Some practical approaches include:
- Modernized Access Protocols - Transition from outdated keys or shared codes to biometrics or individual PIN systems.
- Enhanced Staffing - Deploy trained security personnel where surveillance alone isn’t enough.
- Advanced Safety Systems - Upgrade fire suppression, intrusion detection, or environmental monitoring technologies.
- Resilient Continuity Plans - Build and test recovery strategies to withstand unexpected disruptions.
6. Survey Personnel
Technology alone can’t secure an organization; people remain the strongest (or weakest) link. Surveying personnel help spot issues that technology misses (doors left propped open, access badges shared, or confusion during emergency drills), as well as training and day-to-day practices that a physical security audit may not reveal.
By engaging employees through interviews, surveys, or focus groups, you can assess:
- How well do staff understand access and emergency protocols
- Gaps in security training or compliance
- Attitudes toward reporting suspicious activity
- Real-world challenges they face in following security measures
This human-level insight complements technical assessments, ensuring that security strategies are practical, understood, and consistently applied.
7. Review Physical Security Systems
Even the most advanced security plan can fail if the physical systems behind it aren’t reliable, up-to-date, and well-coordinated. This stage is about taking a closer look at the “hard” side of security, everything from locks and alarms to cameras and control rooms. The goal is not just to confirm their presence but to evaluate how effectively they work together in real-world conditions.
Key areas to assess include:
Access Control Systems - Biometric scanners, card-based entry, or even traditional keys are managed properly, and can they log or restrict unauthorized access?
Personnel - Supervisors, SOC (Security Operations Center) staff, and guards - are they positioned and trained to respond quickly?
Surveillance Systems - Cameras, monitors, and storage devices - are they high-quality, covering critical areas without blind spots, and is footage retrievable when needed?
Alarms & Response Systems - Do alarms instantly alert the right teams and law enforcement? Are they tested regularly?
Other critical questions to ask:
- Are sensitive zones monitored 24/7, or are there coverage gaps?
- Do alarms trigger if access controls are bypassed and notify the right people?
- Are there camera blind spots that could enable unauthorized access?
- Can the SOC integrate all systems into a single, fast response?
A connected, well-audited system is an interconnected defense network that ensures your organization is ready to detect, deter, and respond to threats without delay.
8. Document and Report Findings
Reports turn observations into actionable strategies, helping leadership prioritize risks, allocate resources, and make informed security decisions. Effective documentation also reinforces accountability, supports compliance, and sets a clear roadmap for continuous improvement.
Well-structured reports not only capture the urgency of identified risks but also justify mitigation measures and present them in a format tailored to different stakeholders (executives, managers, and security teams).
Best practices for documentation:
Use standardized templates - Promote consistency and ensure no critical detail is overlooked.
Incorporate visuals - Severity charts, graphs, and diagrams simplify complex risk data.
Blend qualitative and quantitative data - Combine expert insights with measurable metrics, such as estimated financial impact.
Tailor for the audience - Executives need strategic takeaways, while security teams require technical details.
Maintain comprehensive records - Document findings, recommendations, and follow-ups for compliance and future assessments.
Keep it updated - Treat reports as living documents that evolve with new threats and organizational changes.
Done well, reporting not only drives immediate action but also strengthens long-term security posture by building an evolving record of risk management.
9. Establish a Review Cycle
Physical security is not a one-time effort; it requires continuous attention. Once an assessment is completed, the next critical step is to establish a structured review cycle. Threats evolve, organizational priorities shift, and new security technologies emerge, making regular reassessments essential.
Encourage security staff, stakeholders, and management to revisit findings and validate whether current measures remain effective. This can be achieved through scheduled after-action reviews, follow-up evaluations, or by updating the assessment report entirely.
Establishing a clear timeline, such as biannual or annual reviews, helps maintain consistency and accountability. This proactive approach prevents outdated practices, assures compliance, and keeps security strategies aligned with organizational objectives, ultimately strengthening resilience against emerging challenges.
10. Engage Your Security Expert to Oversee the Security Projects
Implementing security improvements goes beyond identifying risks; it requires expert guidance. Bringing in your security consultant or in-house specialist to lead these projects helps turn recommendations into practical, effective solutions. Their technical knowledge allows them to prioritize initiatives, choose the right technologies, and align upgrades with organizational goals.
With expert oversight, errors are reduced, compliance with industry standards is maintained, and progress is steady from assessment to execution. Consistent involvement of the security expert keeps projects on track, within budget, and delivers measurable results that strengthen overall protection.
Why Is Risk Management Necessary In Physical Security?
The reason why physical security risk assessment is necessary is simple - security breaches can lead to significant financial losses and reputational damage. Even minor incidents, like unauthorized access or facility theft, can disrupt operations, damage client trust, and increase insurance premiums. Compared to these consequences, the cost of a physical security risk assessment is minimal, and the long-term benefits far outweigh the upfront investment.
- Identify Security Gaps
Many organizations are unaware of hidden vulnerabilities within the operations. A comprehensive physical security assessment uncovers gaps in access controls, surveillance coverage, emergency protocols, and employee practices. By pinpointing these risks, companies can focus resources on the most critical areas, avoiding wasted investments.
- Optimize Security Investments
Risk assessments while preventing breaches are also about smarter spending. For instance, small investments, such as upgrading door locks or installing additional cameras, can prevent far costlier incidents later. Acting early maximizes cost-effectiveness while improving safety across facilities.
- Strengthen Protections Against Breaches
A proper physical security risk assessment provides actionable recommendations. Reports guide companies to strengthen defenses, address urgent risks, and ignore negligible ones, creating a clear path to safer operations. From updating access controls to strengthening surveillance, the goal is to close gaps that attackers could exploit.
- Support Strategic Planning
Assessments create a roadmap for future security initiatives. By prioritizing needs, companies can set realistic budgets, allocate staff, and address talent shortages more strategically. This structured approach builds resilience without overshooting financial limits.
- Increase Employee Awareness
Employees are a key factor in facility safety. Risk assessments identify areas where training is needed, helping staff understand threats and adopt safer practices. Over time, a culture of security awareness is built, reducing the likelihood of breaches.
Benefits of Regular Physical Security Risk Assessments
Conducting a thorough physical security audit helps identify vulnerabilities, allowing organizations to implement targeted controls. Beyond prevention, regular physical security risk assessments strengthen overall security, improve operational resilience, and deliver additional benefits such as:
Enhance Business Resilience and Risk Management
All organizations face unexpected challenges, from severe weather and accidents to intentional threats. A comprehensive physical security assessment identifies vulnerabilities across these scenarios and recommends targeted mitigation measures.
By addressing these risks proactively, companies can strengthen their operational resilience, reduce potential disruptions, and equip their teams with the tools and protocols needed to respond effectively when incidents occur.
Foster a Positive Safety Culture
A strong safety culture begins with trust. Employees need to feel that their well-being is a priority. Conducting regular physical security assessments, addressing identified vulnerabilities, and clearly communicating updated safety procedures demonstrates your organization’s commitment to protecting its people.
This proactive approach not only reduces risks but also builds confidence among employees, encouraging them to take safety seriously and actively participate in maintaining a secure workplace.
Mitigate Cybersecurity Threats
Cybersecurity is not just about firewalls and software; physical access can lead to digital breaches. A thorough physical security assessment helps uncover vulnerabilities that could allow unauthorized entry to critical systems or sensitive data.
Key areas to evaluate include surveillance coverage, access control systems, alarm protocols, and security policies.
Identifying weaknesses in these areas lets organizations implement targeted safeguards, from restricted entry points to improved monitoring, reducing the risk of cyber threats and strengthening the connection between physical and digital security.
Stay Compliant with Industry Regulations
For many industries, physical security assessments are mandatory. Conducting regular evaluations helps organizations meet regulatory requirements and avoid costly penalties. Key frameworks and standards include:
- ISO (International Organization for Standardization) 27001 – Provides comprehensive guidelines for managing information security risks.
- HIPAA (Health Insurance Portability & Accountability Act) – Governs how organizations handle and protect sensitive health information in the U.S.
- PCI-DSS (Payment Card Industry Data Security Standards) – Sets security standards for businesses processing credit card transactions.
- OSHA (Occupational Safety & Health Administration) Hazard Identification – Offers industry-specific guidelines for assessing workplace hazards and safety risks.
By aligning your physical security practices with these standards, organizations protect sensitive data, safeguard employees, and maintain operational compliance, all while reinforcing a culture of safety and accountability.
Common Mistakes to Avoid During Physical Security Risk Assessments
To maximize the value of a physical security risk assessment, it’s essential to be aware of the mistakes organizations often make. Avoiding these pitfalls ensures your efforts are both practical and efficient.
- Don’t Delay Action - Every moment spent without proper controls increases exposure to breaches, attacks, and potential liabilities. Act promptly to implement remediation plans.
- Avoid Tunnel Vision - Physical security risk assessments are not only about electronic systems. Physical security gaps and human-related risks must also be evaluated.
- Losing Focus on Key Priorities - Clearly define the purpose of your assessment. Staying within scope prevents wasted resources and ensures manpower and budget are allocated effectively.
- Skipping the Basics - Begin with a full inventory of assets, data flows, and operational processes. Assuming you already know the risks can lead to ineffective remediation strategies.
- Relying Solely on Automated Tools - Tools are valuable, but human expertise is critical to interpret results. Involve internal security teams, external experts, and leadership to cultivate a security-conscious culture.
- Treating It as a Single Event - Risk assessments are not one-off tasks. Continuous updates are necessary as threats evolve, ensuring your organization remains protected over time.
Conclusion
A physical security risk assessment is a systematic evaluation of a facility’s security measures to identify vulnerabilities, potential threats, and areas for improvement. It helps protect people, assets, and sensitive information while reducing financial and reputational risks. Regular assessments allow organizations to address weaknesses and strengthen overall security proactively.
Key steps to conduct a physical security risk assessment include:
- Develop a plan and define its scope
- Identify threats and vulnerabilities
- Assess impact and likelihood
- Review the current state of your physical security
- Implement or update mitigation measures
- Survey personnel
- Review physical security systems
- Document and report findings
- Establish a review cycle
- Engage your security expert to oversee the security projects
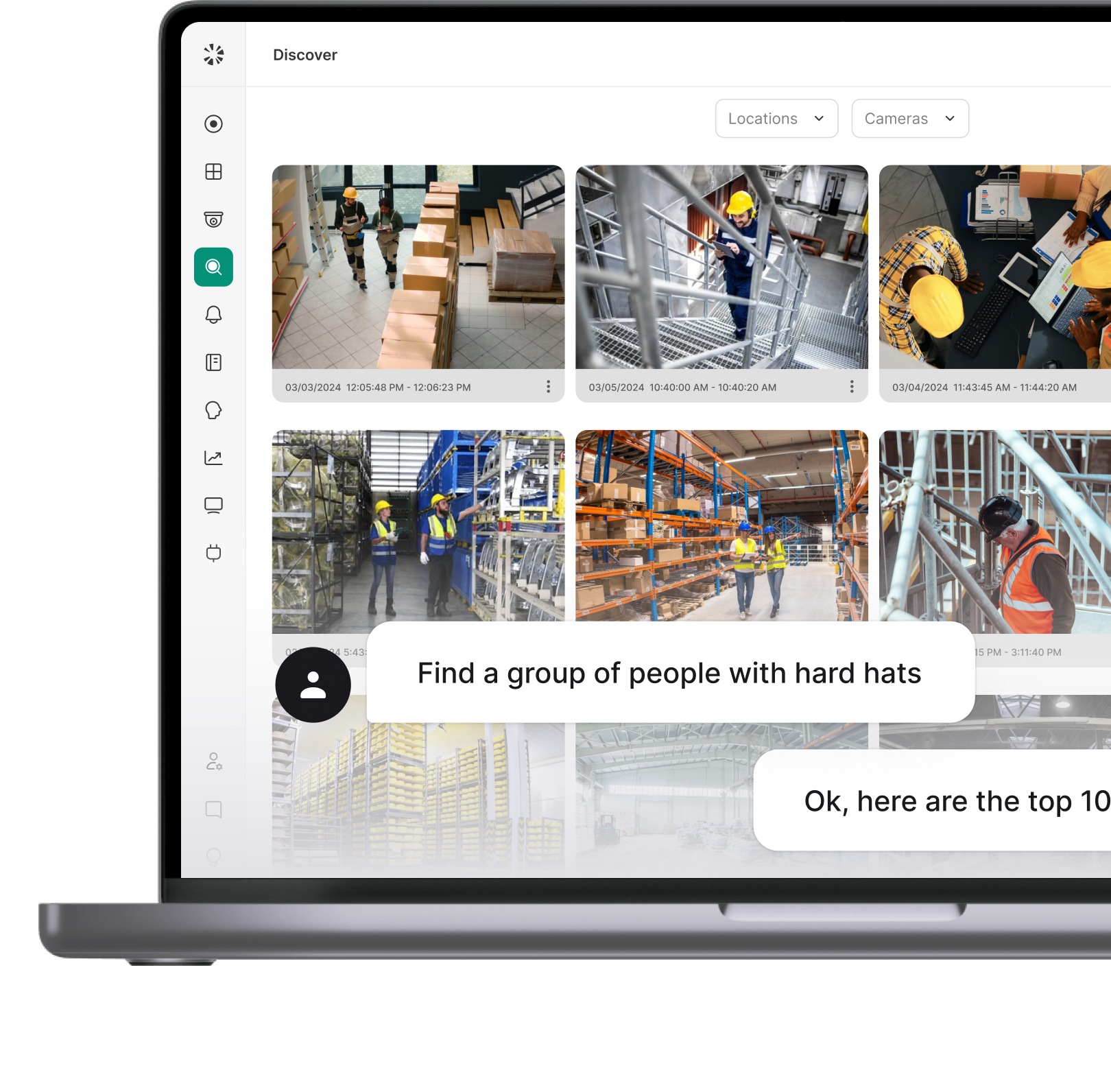
Physical security audits are most effective when paired with reliable security systems. Integrating tools from Coram, such as access control, emergency management, and surveillance cameras with facial recognition, gun detection, and safety alerts, helps organizations detect and address risks efficiently, creating a safer, more resilient workplace aligned with modern security standards.
FAQ
Physical security risk assessments should be performed regularly to identify gaps and address vulnerabilities before they are exploited. A thorough evaluation is typically recommended at least once a year. However, the frequency may vary depending on the organization’s size, industry, and location. Larger organizations, high-risk facilities, or sites with frequent operational changes may benefit from semi-annual or quarterly assessments to stay ahead of potential threats.
Both internal security teams and third-party experts can perform assessments, depending on organizational needs. Internal teams offer familiarity with operations, while external experts provide unbiased insights, specialized experience, and exposure to industry best practices. Many organizations adopt a hybrid approach, leveraging internal knowledge and third-party expertise for a comprehensive evaluation.
A physical security risk assessment identifies potential threats, vulnerabilities, and the likelihood of incidents to prioritize mitigation measures. A security audit, on the other hand, evaluates whether existing security policies, procedures, and systems comply with standards and effectively protect assets. In short, assessments identify risks, while audits verify the effectiveness of controls.




%20(9).webp)