Introduction
Access control regulates a user's entry to a property, or designated areas within it, and typically involves various technologies such as keycards, biometric scanners, PIN codes, or other authentication methods. These systems can integrate with video surveillance to streamline and fortify security measures. In this blog, we will discuss why access control systems are being implemented in video security systems and the benefits they provide the security managers.
Why is this a Priority?
Security breaches at buildings or facilities are prominent, even when there is an access control system to restrict user access. This can include unauthorized users using someone else’s access credentials, doors being left open, or tailgating behind people to enter the building.
.webp)
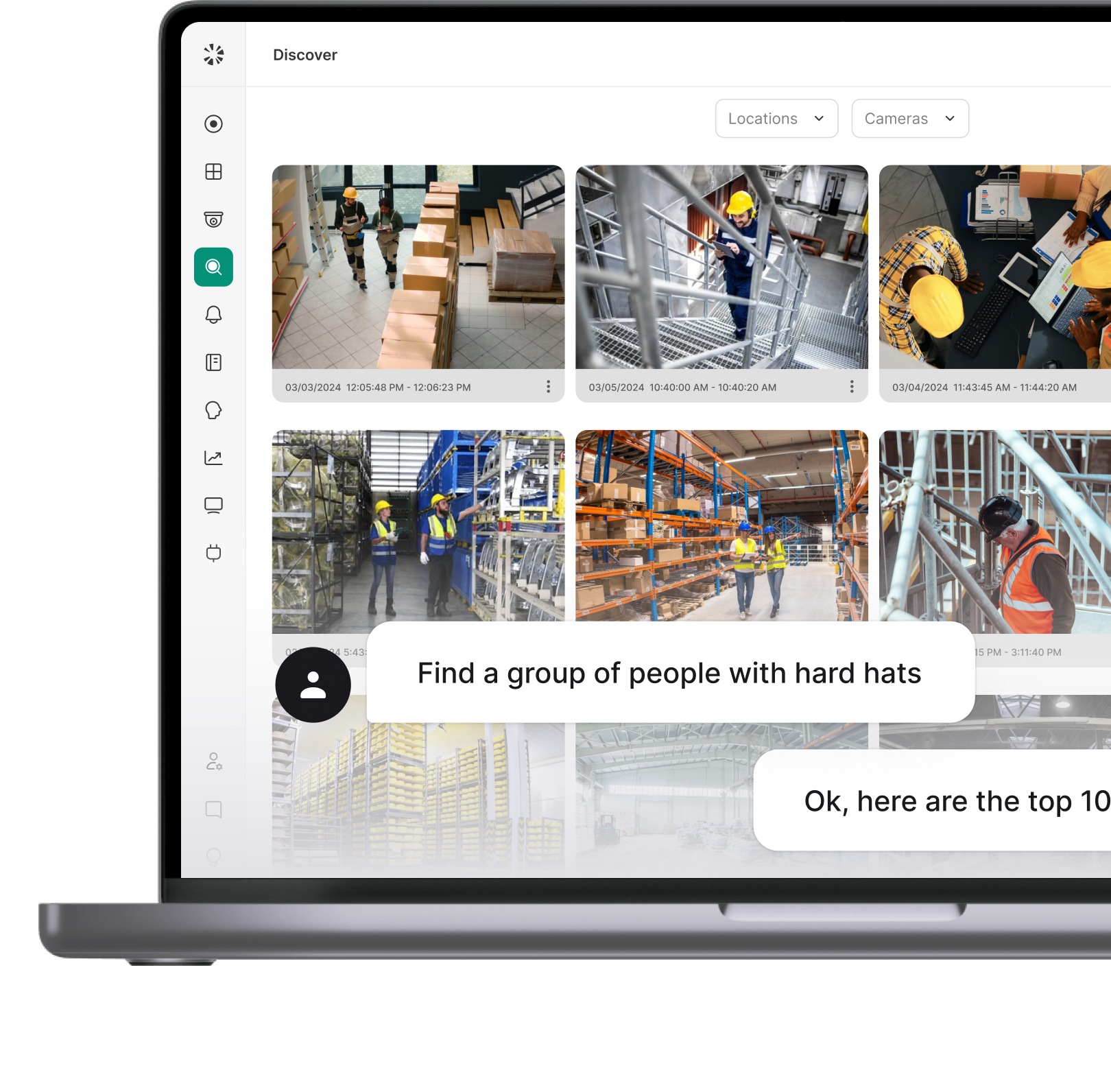
Video surveillance systems provide the visual security needed to see these unauthorized users when they access the building. Security managers typically observe the breach on their video security system, then use their access control system to action any security measures. However, for quicker response and ease of use, access controls can be added within the video security system to investigate and act all in one place.
Access Control Today
Businesses that leverage both access control and a video surveillance system often face two options. They either end with two systems that don’t talk to each other (i.e. different vendors for video surveillance and access control) or they end up buying both from the same provider. The latter ends up locking the business into a single vendor, which could restrict their ability to get the best video surveillance system.
Modern video surveillance companies have begun to adapt with leading access control systems, such that physical security management is all on one platform. This eliminates the options of single vendor physical security systems or systems that do not integrate naturally. This enables you to pick whichever video surveillance and access control system you’d like.
Main Benefits of the Integration Include:
- Entry Verification: Specific cameras can be synced to access controls to monitor the video footage when an event occurs. This includes manually inspecting the person on the video surveillance system who had multiple failed access attempts.
- Automatic Verification: If you have an existing access control or specific requirements to verify identity at entry points, then systems like Coram AI make it easy to manage this on one platform. For example, you can combine facial recognition technology from the video surveillance system with access control and verify that the two systems agree.
- Alerts and Logs: Customizable alerts can be set based on user entries and failed attempts. Access logs capture details such as entry location, time, video clip, and identified user/ID for a security manager to review.
.webp)
Who Benefits from an Access Control + Video Surveillance Integration?
- Large corporate offices with heavy foot traffic and multiple controlled entry points
- Sites where security incidents regularly occur
- Multi-tenant buildings
- Companies with a limited IT staff
Coram AI Integration with Access Controls
Coram AI aims to be an open platform for all physical security needs for businesses. This means we aim to support all existing IP cameras and market-leading access control systems. Using our AI capabilities we enable businesses to save time and gain insights from their cameras. Adding access control to Coram AI’s easily managed system, further improves security processes and simplifies the overall management and operational efficiency.
Coram AI works with any access control system with a publicly available API, such as Brivo and Openpath. It takes only a few seconds to add your access control to the Coram AI dashboard, and from there, logs can be accessed and customized alerts made to further secure the facility. So if a breach is observed, doors can be locked down swiftly by security managers without having to move to another system.




.webp)