As businesses evaluate their security infrastructure in 2026, one fundamental question sits at the front door: Should we continue relying on traditional locks, or is it time to move to modern access control?
For decades, lock-and-key systems have been the standard. They are familiar, affordable, upfront, and mechanically reliable.
But today’s organizations operate in a far more dynamic environment, with hybrid teams, higher employee turnover, multi-site operations, and growing compliance expectations.
In that context, simply locking a door is no longer enough... It’s “Who has access, when, and how do we know?”
Modern access control systems promise greater visibility, flexibility, and scalability. Yet upgrading security is not just about adopting new technology; it’s about understanding what each approach truly offers.
This article provides a clear, practical comparison of traditional locks and access control systems, helping you determine which solution aligns with your operational needs today and in the years ahead.
What Are Traditional Locks?
Traditional locks are mechanical locking systems that use a physical key to secure and unlock a door. Common examples include deadbolts, padlocks, knob locks, and mortise locks. Inside the lock, a series of pins align when the correct key is inserted, allowing the cylinder to turn and the bolt to retract. It’s a design that has worked reliably for centuries.
For many businesses, traditional locks feel familiar and dependable. They are straightforward, easy to understand, and don’t require connectivity or technical setup.
Why Do Businesses Still Use Them?
Traditional locks offer a few clear advantages:
- No need for electricity, batteries, or internet
- Simple installation and replacement
- Lower upfront cost
- Easy to operate without training
For small offices or low-traffic areas, that simplicity can be appealing.
Where They Start to Fall Short?
However, the limitations become noticeable as organizations grow:
- Keys can be lost, stolen, or duplicated
- No visibility into who entered or when
- No remote access or control
- Rekeying is required when staff leave
Traditional locks secure the door itself, but they don’t provide insight, flexibility, or control beyond that point.
What Are Access Control Systems?
Access control systems are modern security solutions that manage who can enter specific areas of a building and when. Instead of physical keys, they rely on credentials such as access cards, mobile passes, PIN codes, or biometrics (like fingerprints) to verify identity.
When a credential is presented to a reader at a door, the system checks permissions through a central control panel or cloud dashboard. If authorized, the electronic lock opens. If not, access is denied, and the attempt can be recorded.
Core Components Typically Include:
- Access readers installed at doors or gates
- Credentials (cards, mobile apps, PINs, biometrics)
- A control panel or cloud dashboard storing user permissions
- Electronic locks connected to the system
Why Organizations Choose Access Control
Access control systems offer practical advantages, especially as teams grow:
- Instant access revocation when employees leave
- Time-based or role-based permissions
- Real-time monitoring of entry activity
- Centralized management across multiple doors or locations
- Detailed audit logs for compliance and investigations
What to Consider
While powerful, access control systems do require:
- Initial setup and configuration
- Power and network connectivity (depending on system type)
- Higher upfront investment compared to basic locks
Access control doesn’t just secure a door; it manages access as an ongoing process. For organizations that need visibility, flexibility, and scalability, it transforms security from static to actively managed.
Access Control vs Traditional Locks
Choosing between traditional locks and modern access control isn’t just about cost, it’s about visibility, flexibility, and long-term security. The table below compares both approaches side by side, highlighting practical differences in control, scalability, monitoring, and overall risk management to help you make a confident decision.
Advantages of Traditional Locks vs Access Control Explained
When businesses compare traditional locks and access control systems, the discussion often starts with cost, but it shouldn’t end there. The real comparison is about control, visibility, flexibility, and how security supports daily operations. Both options offer clear advantages. The key is understanding where each one performs best.
Advantages of Traditional Locks
Traditional locks are mechanical systems that use a physical key to operate a deadbolt, lever, or latch. Their biggest advantage is simplicity.
Straightforward and Familiar: Everyone understands how a key works. There’s no onboarding, no apps, and no training required. For small teams or low-traffic spaces, that simplicity keeps things easy and predictable.
No Power or Connectivity Required: Traditional locks don’t rely on electricity, Wi-Fi, batteries, or software. They function during outages and aren’t affected by system errors or cyber risks. In environments where reliability is critical and technology infrastructure is limited, this independence can be reassuring.
Lower Initial Investment: Mechanical locks are significantly less expensive to purchase and install compared to electronic access systems. For businesses operating on tight budgets, this makes them an attractive starting point.
Widely Available Support: Locksmith services are accessible almost everywhere. Keys can be duplicated quickly, and hardware can be replaced without specialized technicians.
Where They Work Best: Traditional locks are often sufficient for:
- Small offices with minimal employee turnover
- Storage rooms or low-risk areas
- Businesses with simple access needs
However, their advantages are strongest in stable environments where access rarely changes.
Advantages of Access Control Systems
Access control systems shift security from static hardware to active management. Instead of distributing keys, administrators assign credentials — cards, mobile passes, PINs, or biometrics — through a centralized system.
Instant Access Control: One of the most practical advantages is the ability to grant or revoke access immediately. If an employee leaves or loses a credential, permissions can be removed in seconds without changing the physical lock.
Visibility and Accountability: Access control systems maintain detailed entry logs. Businesses can see:
- Who entered
- Which door was used
- The time of access
This level of visibility supports compliance, internal investigations, and overall accountability.
Role-Based and Time-Based Permissions: Not every employee needs access to every room at all times. Access control enables organizations to customize permissions by job role, department, or schedule, reducing unnecessary exposure.
Scalability: As organizations grow, managing dozens or hundreds of physical keys becomes complex. Access control systems are designed to scale across multiple doors, floors, or even locations from a single dashboard.
Improved Emergency Response: In urgent situations, doors can be locked or unlocked centrally. This coordination enhances safety in ways traditional locks cannot.
Long-Term Operational Efficiency: While access control requires a higher upfront investment, it reduces ongoing friction:
- No repeated rekeying costs
- Fewer lost key issues
- Streamlined employee onboarding and offboarding
Where Traditional Locks Still Make Sense?
In a world of cloud dashboards and mobile credentials, it’s easy to assume traditional locks are outdated. But that isn’t always true. In the right setting, mechanical locks still make practical, strategic sense.
While modern access control systems offer advanced capabilities, traditional locks still have a place, especially in environments where simplicity aligns with operational needs.
Small, Stable Teams
If your business operates from a single location with limited staff turnover, physical keys may not create daily friction. When only a few trusted employees require access, distributing and managing keys can remain straightforward and manageable. Best fit scenarios:
- Small offices with under 10–15 employees
- Family-run businesses
- Owner-operated retail stores
Low-Risk or Secondary Areas
Not all doors require monitoring, audit trails, or remote control. For internal rooms where traffic is predictable and risk exposure is minimal, traditional locks can be sufficient. Examples include:
- Storage closets
- Maintenance rooms
- Utility spaces
- Backup or rarely used entrances
In these areas, installing advanced systems may add complexity without proportional benefit.
Budget-Conscious Environments
For startups or organizations prioritizing other investments, traditional locks offer strong physical protection at a lower upfront cost. A well-installed, high-quality deadbolt can still provide meaningful resistance against forced entry. Traditional locks may be appropriate when:
- Security needs are basic
- Capital budgets are tight
- Expansion plans are limited
Limited Technology Infrastructure
In older buildings, leased spaces, construction sites, or remote facilities, installing networked systems may not be practical. Traditional locks operate independently - no wiring, no software configuration, no connectivity requirements. This makes them suitable for:
- Temporary offices
- Warehouses without structured IT networks
- Buildings where infrastructure upgrades aren’t feasible
Mechanical locks remove reliance on system uptime, firmware updates, or integration dependencies.
Preference for Operational Simplicity
Some organizations value predictability over digital complexity. A physical key does one job: it opens a door. There’s no need to manage user profiles, assign permissions, or troubleshoot system alerts. For teams that:
- Don’t require entry logs
- Don’t need remote access control
- Don’t face frequent staffing changes
Traditional locks offer a straightforward, low-maintenance solution that keeps processes uncomplicated.
When Should You Choose Access Control?
Access control isn’t just about replacing keys with cards or mobile credentials. It’s about shifting from basic door security to managed access, where entry is intentional, traceable, and aligned with your organization's operating model. While traditional locks work well in stable, low-complexity settings, access control is the smarter choice as operations become more dynamic.
When Access Changes Frequently
If your organization hires often, works with contractors, or manages shift-based teams, physical keys quickly become difficult to control. Access control allows you to:
- Grant and revoke access instantly
- Assign time-based permissions
- Avoid rekeying doors when someone leaves
In fast-moving environments, flexibility becomes essential.
When Visibility Matters
If you’ve ever asked, “Who opened that door?” and had no clear answer, that’s a signal. Access control provides:
- Entry logs and audit trails
- Real-time monitoring
- Accountability for sensitive areas
This visibility supports compliance, investigations, and internal oversight.
When You Need Layered Security
Modern organizations often require multiple layers of verification. Multi-factor authentication (MFA), PIN + card combinations, or biometric validation can strengthen security where risk is higher. Access control is especially valuable in:
- Healthcare environments handling patient data
- Financial institutions managing sensitive information
- Corporate offices protecting intellectual property
It ensures people access only what their role requires, nothing more.
When You Manage Multiple Sites or Departments
As organizations expand, managing keys across multiple floors, departments, or buildings becomes operationally complex. Access control centralizes oversight, enabling administrators to manage permissions across all locations from a single dashboard. This is especially valuable when:
- Offices operate in different cities
- Warehouses and corporate sites need coordinated security
- Departments require different access levels
Instead of tracking dozens of key copies, access becomes structured, organized, and scalable.
When Compliance and Documentation Are Essential
In regulated industries, proving who had access and when is often just as important as preventing unauthorized entry. Access control systems provide automated audit trails that support compliance with standards such as GDPR, HIPAA, and PCI DSS. Beyond audits, this documentation helps:
- Strengthen internal policies
- Reduce insider risk
- Demonstrate due diligence during investigations
When security must be measurable, not just assumed, access control becomes a strategic asset rather than a convenience.
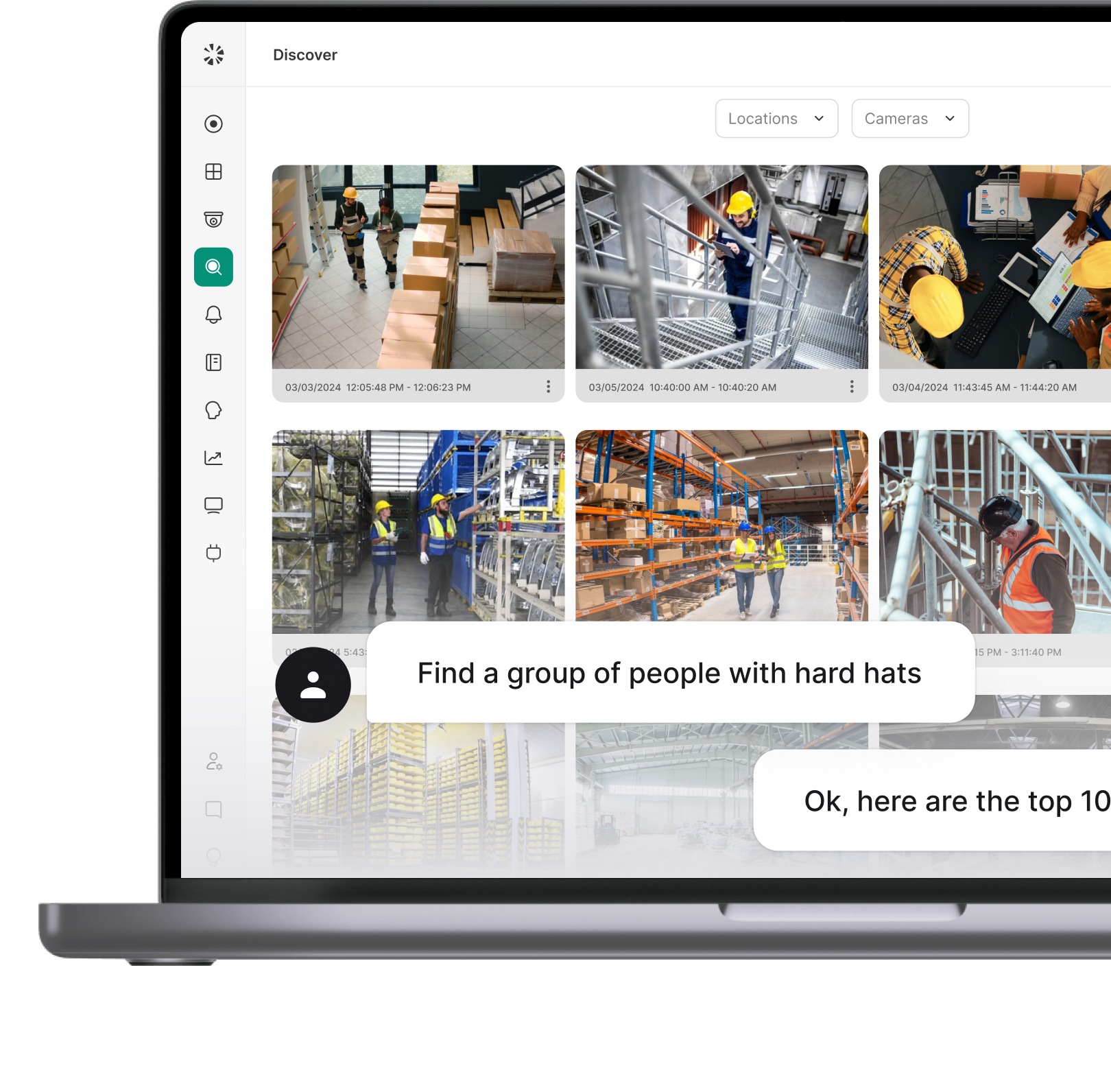
How Coram Takes Access Control Further?
Basic access control lets you unlock doors without keys, but in many organizations, systems still operate in silos. One platform handles doors, another handles cameras, and a third manages alerts.
Coram’s approach takes it a step further by connecting these elements into a single, coordinated security environment.
Turning Door Events Into Real-Time Insight
In a typical system, you might see a log that says: Door opened at 9:12 AM. And in many systems, access control starts and ends with “access granted” or “access denied.” But that doesn’t tell you what actually happened.
Coram links every event to context. Every door activity, whether it’s a granted entry, denied attempt, forced door, or door held open, can be instantly paired with video. That means security teams can immediately verify context without switching systems or manually searching footage.
This integration transforms access control from a record-keeping tool into an operational awareness tool. You don’t just know a door opened. You see who entered, whether someone followed behind, or if something unusual occurred.
Centralized Management Across Locations
As organizations expand, complexity increases. Multiple buildings, departments, vendors, and shift schedules create layers of access needs. Coram simplifies this through a unified, cloud-based dashboard. From a single interface, administrators can:
- Assign role-based or time-based permissions
- Manage mobile credentials, keycards, or biometrics
- Instantly revoke access when staff leave
- Monitor real-time activity across all sites
- Generate compliance-ready reports
There’s no need to rekey doors or coordinate with local technicians for routine updates. Changes happen instantly and securely.
Built for Scalability and Continuity
Security systems must remain reliable. Coram’s hardware-agnostic design works with existing locks and readers, minimizing disruption during upgrades. Offline functionality ensures doors continue operating even during network outages, maintaining business continuity. This flexibility allows organizations to modernize without replacing their entire infrastructure.
Intelligence That Supports Prevention
The access data alone is useful, but connected access data is powerful. Coram doesn’t just record activity; it helps surface patterns. By integrating access events with video, alerts, and even IoT systems, it provides proactive visibility into unusual behavior — like tailgating, repeated denied entries, or after-hours access attempts.
Offline functionality ensures continuity during outages, while hardware-agnostic design allows organizations to work with existing locks and readers.
A Unified Command Center View
Instead of juggling separate systems for doors, cameras, and alerts, Coram brings them together. The result is operational clarity - one interface, one source of truth, and faster decision-making when it matters most. The result is faster decision-making, clearer oversight, and less operational friction.
In 2026, access control shouldn’t just open doors. It should provide visibility, coordination, and confidence across your entire facility.
Conclusion
Traditional locks and access control systems both serve the same purpose, protecting your doors, but they do it in very different ways.
- Traditional locks offer simplicity, affordability, and mechanical reliability. They don’t depend on power or software, and for small, stable environments, they can work perfectly well. However, they lack visibility, flexibility, and control, especially when keys are lost, copied, or difficult to manage.
- Access control systems, on the other hand, provide centralized management, real-time monitoring, and scalable permissions. They require a higher upfront investment and some technical setup, but they deliver accountability, adaptability, and long-term efficiency.
In 2026, the “winner” depends on your needs. If your environment is simple and static, traditional locks may suffice. But for growing organizations seeking control, visibility, and smarter security management, access control clearly leads the way.
FAQ
In many business environments, yes. Traditional locks secure a door, but they don’t provide visibility or control once a key is distributed. Access control systems allow administrators to track entry, revoke permissions instantly, and assign role-based access. While both can be physically secure, access control adds oversight and flexibility that mechanical locks cannot offer.
Lost keys, employee turnover, and lack of visibility are common challenges. Access control eliminates the need to rekey doors when someone leaves and allows businesses to manage permissions remotely. It also provides entry logs, improving accountability and compliance.
Like any connected technology, access control systems can be targeted. However, modern platforms use encryption, multi-factor authentication, and secure cloud infrastructure to reduce risk. Proper configuration and cybersecurity practices are critical to maintaining system integrity.
Businesses can choose from keycard systems, PIN-based keypads, mobile credentials, biometric systems (fingerprint or facial recognition), and hybrid solutions. Some systems are on-premise, while others are cloud-based for remote management.
Yes, when implemented correctly. Reputable providers use secure data encryption, redundant cloud infrastructure, and strict compliance standards. Cloud-based systems also offer remote management, automatic updates, and scalability, making them both reliable and practical for modern organizations.