The financial impact of workplace violence in hospitals reached an estimated $18.27 billion in 2023, according to data from the U.S. Bureau of Labor Statistics and the National Safety Council, covering victim treatment, additional security staffing, and prevention programs. Healthcare workers face workplace violence at rates 16 times higher than workers in other sectors, and in 2024, 276 million patient records were exposed or stolen.
These incidents usually happen due to uncontrolled or loosely managed access: people entering restricted areas, visitors moving without supervision, or unclear access boundaries. This is exactly where hospital access control systems help, by defining who can enter specific zones, limiting movement to only what’s necessary, and tracking access in real time to reduce unauthorized presence in ICUs, emergency wards, or medication storage.
This guide is designed to help you implement hospital security access control, understand how these systems function within healthcare settings, and how they directly help reduce risks and operational losses. Along the way, you’ll also find a clear comparison of top vendors and practical guidance to choose a system that fits your facility without overcomplicating daily operations.
Why Access Control Matters More in Healthcare Than Any Other Industry?
Access control in healthcare is far more critical than in most other industries because the stakes are fundamentally higher, directly impacting human lives, trust, and financial stability. The two biggest reasons behind this are patient and staff safety and the protection of sensitive patient data (PHI).
The numbers make this clear. Healthcare data breaches cost an average of $10.22 million per incident in 2025, the highest of any industry. Hospitals lose an estimated 10–20% of key assets to theft annually. In 2023, 79.7% of healthcare data breaches resulted from hacking, with over 133 million patient records exposed that year.
On the physical safety side, 55% of healthcare workers reported facing increased violence according to the 2026 State of Physical Security Report, and healthcare workers accounted for 73% of all nonfatal workplace injuries and illnesses due to violence.
In these cases, uncontrolled access can lead to unauthorized entry into high-risk areas like ICUs or emergency wards, which increases the chances of violence, disruptions, or delays in treatment. Similarly, patient data is spread across record rooms, admin areas, and digital systems, which need strict control to prevent breaches that can lead to legal issues.
Access control systems take care of both these aspects by ensuring that only the right person can access specific areas or information, while also maintaining clear records of movement and access. This way, you can have both preventive control and accountability in your facility.
Types of Access Control Systems Used in Healthcare
In healthcare, facilities mostly use a mix of methods, and each solves a specific problem. Some access control systems are designed for smooth daily movement, while others focus on tight security in sensitive zones. Here’s how they differ and where they fit:
Card-Based / Credential Systems
Card-based systems are widely used in healthcare because they make it easier to manage access across large, constantly moving teams. Each staff member is issued a card with permissions based on their role, and when it’s tapped or swiped, the system verifies access for that specific area. This allows facilities to keep a record of entries for accountability. In healthcare specifically, these systems integrate with automated dispensing cabinets like Pyxis and Omnicell, meaning the same credential that opens a door also authenticates medication access, which simplifies workflows while strengthening audit trails.
Mobile Credential / Bluetooth Access
Mobile-based access lets users unlock doors through an app using Bluetooth or NFC, shifting control from physical cards to digital credentials. This makes it easier to update or revoke access instantly as roles change, without managing physical items, while also reducing misuse since personal devices are less likely to be shared. For healthcare settings with high staff turnover, rotating nurses, or visiting specialists, mobile credentials can be issued and time-limited remotely, which eliminates the delays involved in printing and distributing physical cards.
Biometric Systems
Biometric systems verify identity using traits like fingerprints, facial recognition, or iris scans, which makes them more secure than cards or devices. Since these traits are tied to the individual and cannot be easily lost or shared, they reduce misuse and are especially suited for high-risk areas like pharmacies, labs, or data rooms where strict control is critical. In pharmacy environments, biometric access supports compliance with DEA requirements for controlled substances, particularly for Schedule II–V medications where dual-authentication is required. That said, facilities should also consider hygiene implications, as shared-touch readers in clinical environments may require antimicrobial coatings or touchless alternatives like facial recognition or iris scanning.
Multi-Factor & Hybrid Systems
Multi-factor and hybrid systems require users to verify access through multiple methods, such as a card with a PIN or biometric plus mobile authentication, adding an extra layer of security. This approach is used in high-risk areas like operating theatres, server rooms, or controlled substance storage, where relying on a single method is not sufficient. In NICU and maternity wards, some facilities pair RFID-based mother-baby matching tags with multi-factor staff authentication to prevent infant abductions, which have historically occurred in healthcare facilities at significant rates.
Based on the discussion, here’s a quick comparison of the above-mentioned categories of healthcare facility access control systems:
Key Features to Look for in Healthcare Access Control
While choosing a healthcare access control for your healthcare facility, it’s important to prioritize certain key features as they can significantly influence your operational as well as long-term growth. Here are some features to look out for:
HIPAA Physical Safeguard Compliance
Under HIPAA regulations, healthcare facilities are required to restrict and manage physical access to areas where ePHI exists, such as servers, records, and connected devices. Access control systems support this by enforcing role-based permissions and maintaining logs of every entry. HIPAA requires audit log retention for a minimum of 6 years, which means the system needs to reliably store and retrieve access records over extended periods. This ensures that access is not only limited to authorized individuals but also traceable over time, so every action can be reviewed, verified, and accounted for when needed.
Zone-Based Access Levels
Zone-based access works by dividing the facility into different areas, such as public, clinical, restricted, and critical, and assigning permissions based on both role and risk level. This solves the problem of over-access, where individuals technically have permission but don’t need to be in certain areas. This reduces exposure to sensitive zones, protects assets and data, and makes it easier to trace activity when needed.
Emergency Lockdown & Override Capabilities
This feature allows administrators to lock down specific zones or the entire facility instantly, often from a central dashboard. A centralized system enables immediate response, while override logic prevents disruption to essential services. So instead of choosing between security and functionality, the system adjusts access dynamically so that the movement is controlled.
Visitor Management & Temporary Credentials
Visitor management looks after access for visitors, contractors, and temporary staff by assigning verified, time-bound, and area-specific credentials. It typically includes registration, identity validation, and automatic expiration of access. This solves the lack of control over non-staff movement. So, by formalizing entry, the system ensures that even temporary access is limited, monitored, and recorded.
Integration with Video Surveillance
When access control is integrated with video surveillance, every entry event can be linked to footage. This becomes critical during incidents. Without integration, teams often need to switch between systems, trying to match logs with video manually, which slows down response and leaves room for error.
Integration with Nurse Call and Duress Systems
Given that workplace violence is one of the most pressing safety concerns in healthcare, access control should also connect with nurse call and duress response systems. When a nurse activates a panic button, the access control system can trigger automatic lockdowns in the immediate zone while alerting security staff in real time. This integration ensures that the system does not just manage entry, but actively supports staff safety when an incident is unfolding.
Cloud vs. On-Prem Architecture
When evaluating access control, the choice between cloud and on-prem affects how the system is managed, maintained, and scaled over time, including control, IT workload, and multi-site operations. Cloud systems work better for distributed teams and multiple locations by reducing operational overhead, while on-prem systems are more suitable when full control over data, infrastructure, and security policies is required.
Scalability Across Multiple Facilities
As your facilities expand across multiple buildings, cities, or regions, access control needs to scale without ever becoming fragmented. This is critical because it ensures that you can easily manage multiple sites under a centralized structure, where access policies, user roles, and permissions remain consistent. Without this, each facility often ends up operating independently, which creates gaps, inconsistencies, and more administrative overhead.
5 Best Access Control Systems for Hospitals
When it comes to choosing the best access control system for a healthcare facility, you can easily come across multiple platforms. Most of these offer more or less the same capabilities, yet some platforms stand out due to their approach to healthcare safety. Here are 5 hospital access control systems you can consider:
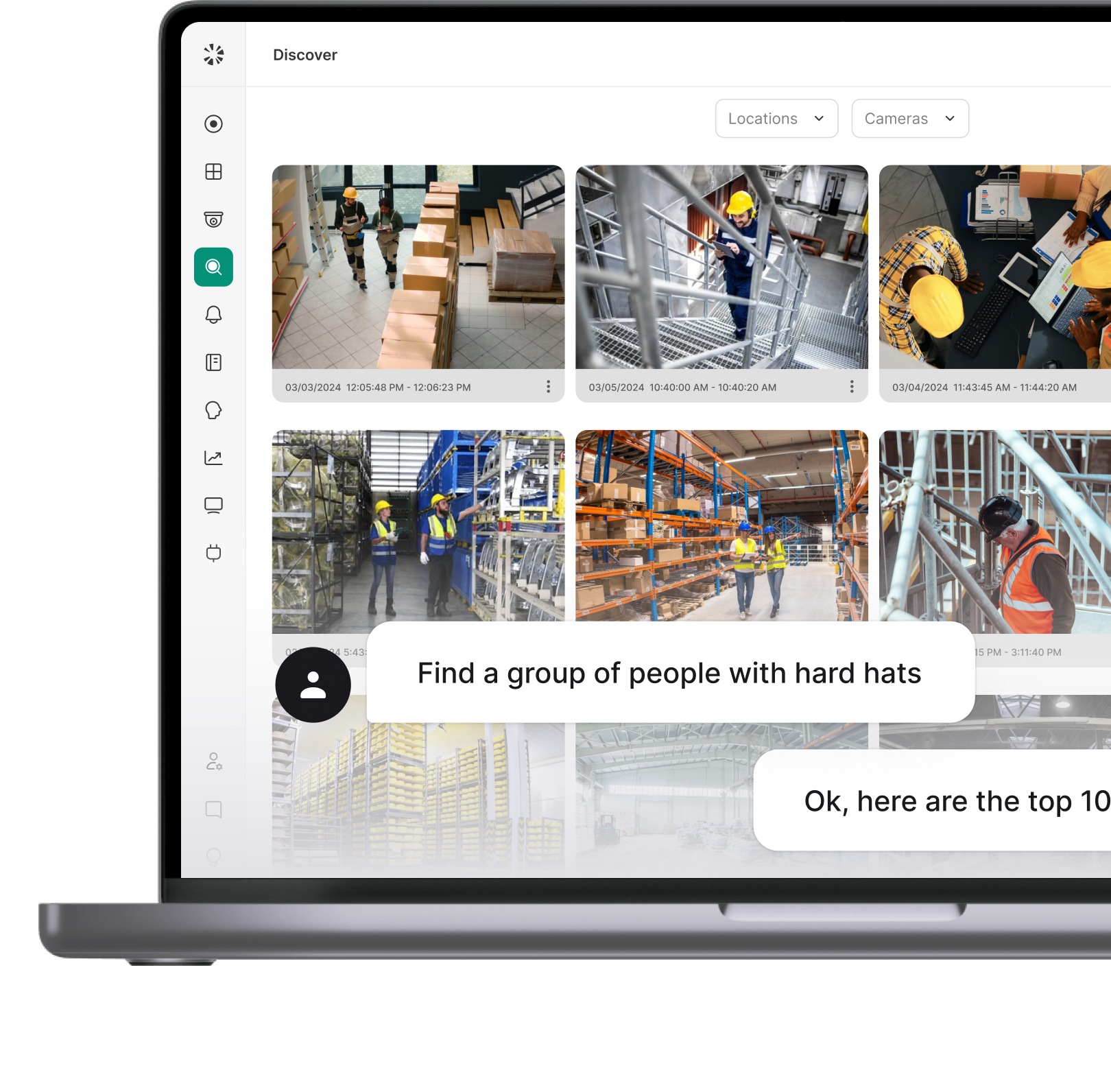
Coram
Coram’s access control system is designed to adapt as your facility requirements evolve, rather than requiring separate setups for different scales of operation. It supports a wide range of access points, including doors, gates, elevators, and specialty areas, while remaining hardware-agnostic, which is why it can work with existing locks and readers. This makes it suitable for environments where infrastructure is already in place.
The system also places strong emphasis on visibility by linking every access event, such as entry, denied access, forced door, or propped door, with corresponding video footage. This connection works with both existing camera setups and Coram’s own cameras. To ensure everything runs smoothly even without the internet, it also comes with an offline mode that ensures access control continues to function during network disruptions.
Best for: Healthcare facilities that need native video-linked access control across single or multi-site environments, especially where existing hardware needs to be retained rather than replaced.
Strengths
- Ease of use, with an intuitive interface that minimizes training overhead
- Native event-to-video linking for every access event, which is a differentiator among platforms in this category
- Fast and relatively simple setup process
- Responsive customer support
- Scalable across single-site and multi-site environments without major complexity
Limitations
- Reported camera-related issues, including freezing and slow calibration, which can delay incident review in time-sensitive situations
- Mobile app performance lags during video playback, which limits the usefulness of remote monitoring
- Occasional delays in streaming and searching for footage, particularly in larger deployments
Genetec Security Center
Genetec offers Synergis, an enterprise-grade access control system designed to manage large and distributed environments from a single platform. It enables you to centrally manage cardholders, remote door control, and schedule access across multiple locations. The system is part of the broader Security Center platform, where access control works alongside video surveillance and other security functions in a unified interface.
The platform works on an open architecture and supports a wide range of third-party devices such as readers, controllers, and locks from manufacturers like Axis, HID, and STid, allowing facilities to integrate existing hardware instead of replacing it. This flexibility is supported by regular updates, ensuring compatibility with newer technologies over time and maintaining stable operations while meeting enterprise-level security requirements.
Best for: Large hospital systems and multi-campus health networks that need a unified enterprise platform managing access control, video, ALPR, and intercom under one interface.
Strengths
- Strong unified platform combining access control with other security systems
- Extensive integrations with third-party devices and systems
- Flexible architecture that works with existing hardware
- Reliable customer support, especially in critical situations
Limitations
- Significant learning curve, especially as the system scales in size and complexity, which can burden smaller IT teams
- The breadth of features can add operational overhead for mid-size or single-site facilities that don’t need the full enterprise suite
- Initial deployment and configuration require dedicated time and expertise, often involving certified integrators
Avigilon (Motorola Solutions)
Avigilon Alta offers a flexible access control setup that supports both cloud-based and on-premise deployments, allowing facilities to choose how they want to manage and scale their system. The platform supports a variety of entry points, including doors, gates, elevators, and parking areas, making it adaptable to different facility layouts.
In terms of access methods, it supports traditional credentials like key cards and fobs, along with mobile-based access, intercom systems, and touchless options such as wave-to-unlock and QR codes. It also integrates closely with video security, which helps connect access events with visual context. This combination of credential flexibility and integration is aimed at creating a more seamless entry experience while maintaining visibility across the facility.
Best for: Facilities that prioritize touchless entry and credential flexibility, especially those with high foot traffic at multiple entry points like ERs, lobbies, and parking structures.
Strengths
- Straightforward implementation and installation process
- Strong mobile capabilities, including touchless access options suited for clinical environments
- Reliable performance with smooth integration across systems
- Responsive customer support
Limitations
- Performance issues during firmware updates can temporarily disrupt access operations
- May require hardware upgrades over time, adding unplanned costs to the total deployment
- Priced at a premium compared to alternatives, which can be a factor for cost-sensitive facilities
Brivo
Brivo is primarily a cloud-based access control system designed to provide centralized visibility and control across facilities, whether it’s a single location or a growing multi-site setup. The platform allows users to manage access, monitor activity, and respond to incidents from any device, which becomes especially relevant in environments where teams are not always on-site.
The system supports integration with existing hardware, which allows you to adopt it without fully replacing your current infrastructure. This open integration approach, along with its cloud architecture, makes it easier to scale as needs evolve, which positions Brivo’s access control as a way to improve overall operational visibility and efficiency.
Best for: Mid-size hospitals and clinic networks that want straightforward cloud-based management with remote access, particularly those with rotating staff or contractors needing quick credential issuance.
Strengths
- Strong cloud-based access with remote management from any device
- Good visibility into access activity and system-wide events
- Data-driven insights through activity tracking and analytics
Limitations
- Heavy reliance on internet connectivity due to the cloud-first approach, which can be a risk in facilities where network outages occur
- Advanced analytics and features may require higher-tier plans, increasing the ongoing cost
- Video integration exists but is not deeply unified, meaning teams may still need to cross-reference systems during incidents
ACRE Security
Acre Access Control is built as a cloud-native system that’s designed from the ground up to operate in cloud environments rather than being adapted to it later. This allows it to support centralized management across multiple sites, with access available through web browsers, desktops, and mobile devices.
It also supports flexible workflows through customizable dashboards, so your teams can structure the interface based on how your facility operates. At the same time, the platform supports advanced logic and integrations, which makes it suitable for environments where access rules are more complex and need to adapt to different scenarios.
Best for: Multi-site healthcare organizations that need true cloud-native architecture with complex access logic and customizable operational workflows.
Strengths
- Strong multi-site management with centralized control
- Customizable dashboards aligned with operational workflows
- Supports advanced logic and integrations for complex environments
- Automatic updates that reduce maintenance overhead
Limitations
- The interface can be unintuitive, with some features not immediately easy to locate, which slows down adoption for frontline security staff
- Navigation may take time to get used to for new users, increasing the training burden
- Video integration is supported but not deeply native, which may require additional configuration to link access events with footage
Comparison Table
Most access control platforms today check the same basic boxes, but they still offer different capabilities on some fronts. For a better understanding, here’s a quick comparison so you can see where each system actually stands:
The right choice depends on how well the platform aligns with your environment. The key is to evaluate how the system will perform over time, how it integrates with your existing setup, how easily it can scale, and how effectively it supports your security and operational workflows.
HIPAA Compliance and Access Control: What You Need to Know
Access control in healthcare is directly tied to HIPAA’s Security Rule, which requires organizations to protect electronic protected health information (ePHI) through a mix of administrative, technical, and physical safeguards. Here’s what you need to take note of:
HIPAA Physical Safeguard Requirements (§164.310)
§164.310 is the part of the HIPAA Security Rule that covers the physical side of protecting patient data where that data is stored or accessed. It consists of four standards that target a different layer of physical risk:
- Facility access controls (§164.310(a)): Define and document who can access specific areas based on role, and how that access is verified.
- Workstation use (§164.310(b)): Set rules for how systems handling ePHI are used, including placement, screen locks, and user access.
- Workstation security (§164.310(c)): Secure devices so only authorized users can access them, with measures like automatic logoff.
- Device and media controls (§164.310(d)): Track hardware throughout its lifecycle, ensuring proper handling, disposal, and data removal.
Note: Some specs under §164.310 are labeled “required,” and others are “addressable.” Here, addressable does not mean optional. If in your facility, a particular spec doesn’t fit the environment, you need to document that decision and the steps taken. Otherwise, skipping it without that documentation is a compliance gap, even if nothing has gone wrong yet.
How Access Control Systems Support HIPAA Compliance
When it comes to HIPAA compliance, role-based access control in healthcare becomes critical because it ensures that every person in the facility only has access to the areas they actually need. At the same time, every access event (whether granted or denied) is recorded with a timestamp and tied to a specific credential, which allows you to trace movement when an incident needs to be investigated.
With the 2025 HIPAA updates, this level of control is becoming significantly stricter. The proposed modification to the HIPAA Security Rule, released on December 27, 2024, represents the most sweeping update to the rule since 2013. Key changes include mandatory multi-factor authentication (MFA) across all systems that access ePHI, required encryption of ePHI both at rest and in transit, annual penetration testing and vulnerability scanning with defined remediation timelines, maintenance of an annually updated technology asset inventory and network map, and the ability to restore critical systems within 72 hours following a disruption.
Beyond MFA and encryption, there is a clear shift toward managing physical and digital access together, because when these systems operate separately, gaps start to appear. The proposed rule reinforces this by requiring that access controls, whether physical or logical, be tied to a unified identity framework so that permissions are consistently enforced across the entire system. Organizations will have a 240-day compliance window once the final rule is published, which means preparation should begin now.
Joint Commission Requirements
TJC (The Joint Commission) accreditation covers the full physical environment of a healthcare facility, which goes even further than HIPAA in scope. With the 2026 Accreditation 360 overhaul, TJC is restructuring its standards framework. The Environment of Care and Life Safety chapters are being merged into one Physical Environment chapter, consolidating requirements and changing how compliance is measured. This restructuring means that access control, emergency management, and physical environment safety are now evaluated under a single, more integrated framework.
A few areas get specific attention under the updated standards:
- Workplace violence is now a National Performance Goal, linking access control in high-risk areas like emergency departments to accreditation metrics.
- Pharmacy and medication storage require detailed access logs for diversion investigations.
- Maternity and NICU units must follow strict infant protection standards with controlled entry and monitored exits.
- Systems must support emergencies with lockdowns, overrides, and reliable operation during outages.
So now, if your access control system is logging data, that data should reflect a consistent, coherent security posture. With the 2026 changes, surveyors will be looking at physical environment controls as a whole, not in isolated silos. Your access logs, lockdown procedures, and visitor management protocols all need to tell the same story.
How to Choose the Right System for Your Healthcare Facility
To make sure you choose the right access control system for your healthcare facility, it’s important to keep a few pointers in mind. Here are a few considerations to take note of:
Assess Your Facility Type
The structure and purpose of your facility quietly determine how access control needs to behave, before any technology is selected. A single-site clinic with under 50 doors and a small team can typically manage with a straightforward cloud-based system and standard credentials. A multi-campus hospital system, on the other hand, needs federation support, centralized policy management, and the ability to handle thousands of credentials across different locations with different risk profiles. So, always first assess your facility type and then see which vendor fits those requirements.
Audit Your Existing Infrastructure
Before selecting a system, understand what’s already in place in terms of network capacity, door hardware, badge systems, surveillance, and IT infrastructure. In many cases, you might realize that you don’t need to replace everything, but to build on or integrate with existing systems where possible. Check whether your current readers support modern protocols, whether your network can handle additional connected devices, and whether your camera system can integrate with a new access control platform. This audit often reveals that a hardware-agnostic platform saves significant cost compared to a full rip-and-replace approach.
Define Your Security Zones
Defining zones brings clarity to access by separating areas based on risk: what’s public, what needs restriction, and what requires tight control due to sensitive assets like patient data, medication, or critical systems. Map your facility floor by floor: public lobbies and waiting areas, clinical zones like patient rooms and nurse stations, restricted areas like pharmacies and labs, and critical zones like server rooms, narcotics vaults, and NICUs. Each zone should have a defined access policy, and your system should be able to enforce those policies consistently without manual intervention.
Evaluate Total Cost of Ownership
While initial pricing matters, the hidden costs often show up over time in the form of maintenance, updates, system management, and how much your IT team has to stay involved. It also depends on how the system is set up, as with on-premise, you’re responsible for keeping everything running smoothly. Cloud systems take that load off your team, but you’re paying on an ongoing basis and relying on the vendor. When evaluating cost, factor in per-door hardware costs, annual software licensing, integration expenses, training time, and ongoing support fees. For reference, industry data suggests that small hospitals can achieve payback within 1 year with strong long-term ROI, while larger facilities with more complex deployments typically see payback within 1–2 years.
Prioritize Integrations
Access control is only one part of a larger security setup, and when these systems operate separately, information gets scattered, which makes it difficult to see the full picture during an incident or even track what actually happened. Integration brings these systems together so access events can be linked to video, permissions can be managed from one place, and updates like onboarding or offboarding happen across all systems at once. Specifically, evaluate whether the platform integrates with your video surveillance, nurse call and duress systems, visitor management tools, HR and identity management platforms, and building management systems. The more unified the ecosystem, the fewer gaps exist during an incident.
Final Takeaway
Access control plays a more critical role in healthcare than in most other sectors because it directly connects to patient safety, data protection, and uninterrupted operations. That’s exactly where access control becomes preventive by limiting unnecessary movement, restricting high-risk areas, and ensuring that access is always aligned with role and need.
So, when evaluating systems, focus on how they perform in real conditions, how easily they can be managed across locations, and how well they integrate with the rest of your setup. That’s how you can make a smart decision and choose a hospital access control system that delivers consistent control and the flexibility to adapt as the facility evolves.
FAQ
It’s the process of controlling who can access systems, data, or physical areas in a healthcare facility to protect sensitive patient information.
The main types are Discretionary (DAC), Mandatory (MAC), Role-Based (RBAC), and Attribute-Based (ABAC), which define how access permissions are assigned and enforced.
Yes, HIPAA requires access controls to make sure only authorized individuals can access ePHI as part of its security safeguards.
The best system depends on your facility’s size, infrastructure, and priorities. For environments where native video-access linkage and scalability across multiple sites are priorities, Coram is a strong choice because it connects every access event with corresponding footage in a single platform.
Larger enterprise networks with complex integrations may lean toward Genetec, while facilities prioritizing touchless entry may find Avigilon Alta more suitable. The key is matching the platform to your operational reality rather than selecting based on feature lists alone.
Costs vary widely based on size and setup, typically ranging from a few thousand for small setups to enterprise-level investments for large hospitals.
Yes, most modern hospital access control systems integrate with video surveillance to link access events with footage for better visibility and incident response.