The way early years settings think about security is starting to change. What was once a matter of locked doors and paper sign-in books has evolved into something more structured, more accountable, and increasingly digital. The EYFS statutory framework now expects providers to demonstrate not just that children are safe, but that systems are in place to prove it.
This shift is why nurseries, preschools, and reception classes are evaluating security infrastructure differently than they did a few years ago. Understanding exactly what the EYFS requires, and how modern security systems support those requirements, can help you make informed decisions about your setting's approach.
This guide covers the security measures, procedures, and compliance requirements that early years providers need to meet EYFS safeguarding and welfare standards in 2026.
What Are the EYFS Safeguarding and Welfare Requirements?
The EYFS statutory framework is issued under Section 39 of the Childcare Act 2006. Section 3 of the framework covers safeguarding and welfare requirements, setting out what early years providers must do to keep children safe.
At its core, the framework states that providers must take all necessary steps to keep children safe and well. This includes ensuring the suitability of adults who have contact with children, promoting good health, managing behaviour, maintaining premises and equipment safely, and establishing policies and procedures for safeguarding.
For security specifically, the requirements focus on three areas: controlling who enters the premises, knowing who is on site at all times, and having procedures to respond to emergencies.
The Legal Foundation
The Childcare Act 2006 is the primary legislation governing childcare and early years provision in England. It gives legal force to the EYFS framework and establishes the welfare requirements that all registered providers must meet. Under the Act, Ofsted has the authority to inspect settings against these requirements and take enforcement action when providers fail to comply.
This matters because Ofsted inspectors assess whether settings have effective systems to keep children safe. A setting that cannot demonstrate who is on the premises at any given time, or that lacks clear procedures for managing visitors, will receive a negative judgement in the safeguarding and welfare section of their inspection.
2025 EYFS Safeguarding Reforms: What Changed
The Department for Education updated the EYFS framework in September 2025 following a consultation that received over 1,470 responses. The changes strengthen safeguarding requirements and align the framework with current best practice.
Here is a breakdown of the key changes:
The consultation showed that many early years providers already had excellent practices in place. The updates essentially codify what leading settings were already doing, which means the transition should be straightforward for well-run organisations.
Legal Requirements vs Recommended Practice
Understanding the legal landscape helps providers distinguish between what they must do and what represents best practice.
The distinction matters because while CCTV and electronic access control are not legally mandated, a setting without these measures needs to demonstrate how it meets the underlying statutory requirements through other means. In practice, digital systems make compliance easier to maintain and demonstrate.
Insurance policies for early years settings also typically require certain security measures. Failure to maintain these measures could void coverage or result in higher premiums. Check your policy documentation to confirm specific requirements around locks, lighting, fire detection, and secure storage.
Essential Security Systems for EYFS Compliance
Meeting EYFS security requirements involves appropriate physical security infrastructure. The challenge for early years settings is balancing genuine security with a welcoming environment for children and families. An intimidating security setup defeats the purpose of creating a nurturing space.
Access Control Systems
Access control determines who can enter the premises and when. For early years settings, this means preventing unauthorised entry while allowing quick exit in emergencies.
The core function is straightforward: external doors should have locks that create an audit trail showing who entered and when. Options range from magnetic locks released by electronic fob to keypad entry systems with changeable codes to video intercom systems allowing visual verification before entry.
The layout of the reception area matters just as much as the technology. Visitors should not be able to proceed beyond reception without being acknowledged by staff. This typically involves a reception desk positioned to oversee the main entrance and a secondary door or gate between reception and the main setting.
What makes access control work in early years settings is discretion. Using hardware that does not look institutional, training reception staff to be friendly while following procedures, and designing entry sequences that feel routine rather than interrogative all contribute to a secure but welcoming environment.
CCTV and Video Surveillance
CCTV is not a legal requirement for early years settings in the UK. However, it is widely used because it supports safeguarding in ways that are difficult to replicate otherwise. Cameras deter inappropriate behaviour, provide evidence for incident investigation, and verify visitor identity at entry points.
Cameras should not be positioned to directly observe children during care routines such as nappy changing or toileting. This is both a privacy requirement and a practical safeguarding measure.
Because CCTV footage contains personal data, it must be handled in compliance with UK GDPR. This means having a lawful basis for processing (typically legitimate interests for security), displaying clear signage, defining retention periods (typically 30 days), restricting access to authorised staff, and having procedures for subject access requests.
Staff and parents should be informed about CCTV use. The key message is that cameras are positioned to support security, not to monitor individual behaviour or observe children's play.
Visitor Management Systems
A visitor management system tracks everyone who enters and exits the premises. This is fundamental to knowing who is on site at any time, which is a statutory requirement.
Paper sign-in books remain common but have significant limitations. Handwriting can be illegible, visitors may forget to sign out, information is difficult to retrieve quickly, and books can be lost or damaged. There are also no automatic alerts or screening checks.
Digital visitor management systems address these issues. They create readable records with consistent data capture, prompt for sign-out automatically, enable instant searchability, integrate with screening databases where needed, and can print badges with visitor photos.
For early years settings, the most valuable features are real-time visitor logs showing everyone currently on site, photo capture at check-in, badge printing with visitor photo and purpose, host notification when visitors arrive, and reporting capabilities for compliance audits.
Managing Visitors in Early Years Settings
Every person entering the premises who is not a registered child or employed staff member should be logged. This includes parents and guardians, contractors and maintenance workers, delivery personnel, Ofsted inspectors, students on placement, volunteers, and professionals visiting children such as speech therapists or health visitors.
Visitor Management Policy
A visitor management policy should establish clear procedures for before, during, and after visits. Expected visitors should be notified in advance to reception. Contractors should provide company details and purpose of visit. DBS requirements for regular visitors should be documented.
On arrival, all visitors report to reception for identity verification, sign in with name, organisation, purpose, and arrival time, receive a visitor badge, and get briefed on emergency procedures. The host is notified that their visitor has arrived.
During the visit, visitors remain with their host or in designated areas, wear badges visibly at all times, and do not use personal mobile phones in child areas. Staff are trained to challenge anyone not wearing appropriate identification.
On departure, visitors return their badge and sign out with departure time. Badges are destroyed or deactivated.
DBS Check Requirements
The position on DBS checks for visitors depends on the nature of their access:
Document your decisions about DBS requirements in your safeguarding policy and keep records of checks completed.
Drop-Off and Pick-Up Security
Drop-off and pick-up times present the highest security risk for most settings. Large numbers of adults arrive in a short period, doors are opened frequently, and staff attention is divided.
Maintaining an authorised collector list for each child is essential. This list should include photos of all authorised collectors, be updated whenever families request changes, be accessible to staff managing collection, and include any restrictions such as court orders.
If someone attempts to collect a child and is not on the authorised list, do not release the child. Contact the parent or primary guardian immediately, keep the child in a safe area while waiting for confirmation, and document the incident.
For families with complex custody arrangements, obtain copies of any court orders, follow them exactly regardless of requests from parents, document all information about custody arrangements, and seek legal advice if unclear about requirements.
Emergency Procedures and Risk Assessment
The EYFS framework requires providers to have procedures for responding to emergencies. Security systems should support these procedures rather than complicate them.
Statutory Emergency Requirements
Providers must have documented and practised procedures for fire evacuation, lockdown, public health incidents, severe weather, serious injury, and criminal activity including intruders or threats.
Fire evacuation requires detection and alarm systems, clear evacuation routes, assembly points, roll call procedures, and regular drills at least termly. Documentation of drills and outcomes is required.
Lockdown procedures should cover securing the building when there is a threat outside, communication methods during lockdown, roles and responsibilities, and practice drills.
Security Risk Assessments
Risk assessments identify security vulnerabilities and guide the deployment of security measures. Areas to assess include entry points (doors, gates, windows, service entrances), perimeter security (fencing, visibility from outside), reception configuration (sightlines, separation from child areas), drop-off and pick-up zones, outdoor play areas, internal circulation, and storage for hazardous materials and records.
The risk assessment process involves identifying hazards and who might be harmed, evaluating risks and existing controls, identifying additional controls needed, recording findings and actions, and reviewing regularly and after any incident.
Risk assessments should be reviewed at least annually, after any security incident, following significant changes to premises or procedures, and when external risk factors change.
Emergency Communication
Communication systems should support emergency response. Internal communication might include two-way radios for staff coordination, panic buttons or duress alarms, and PA systems for announcements. External communication includes direct lines to emergency services, parent notification systems, and contact lists for local authority and support services.
During an emergency, knowing who is on site is critical. Visitor management systems should provide an instant list of all visitors currently signed in, contact details, location information if available, and export to mobile devices for use at assembly points.
Staff Training and Responsibilities
Security depends on staff understanding their roles and following procedures consistently. This is not something that can be fixed with technology alone.
Every staff member has a role in security. This includes ensuring doors close securely behind them, challenging unfamiliar faces, reporting concerns about individuals or security, following procedures during drop-off and pick-up, and knowing their role in emergency procedures.
Drills
Regular drills test whether procedures work in practice. Fire evacuation drills should happen at least termly, lockdown drills at least annually, and other scenarios as appropriate.
Document all drills including timing, participation, issues identified, and actions taken. This documentation serves both as evidence for Ofsted and as a practical tool for improving procedures.
Data Protection and Privacy
Security systems collect personal data. Providers must handle this data in compliance with UK GDPR.
GDPR Compliance for Security Systems
Security systems typically rely on legitimate interests as the lawful basis for processing. This requires documenting your legitimate interests assessment, balancing your interest in security against the privacy rights of individuals.
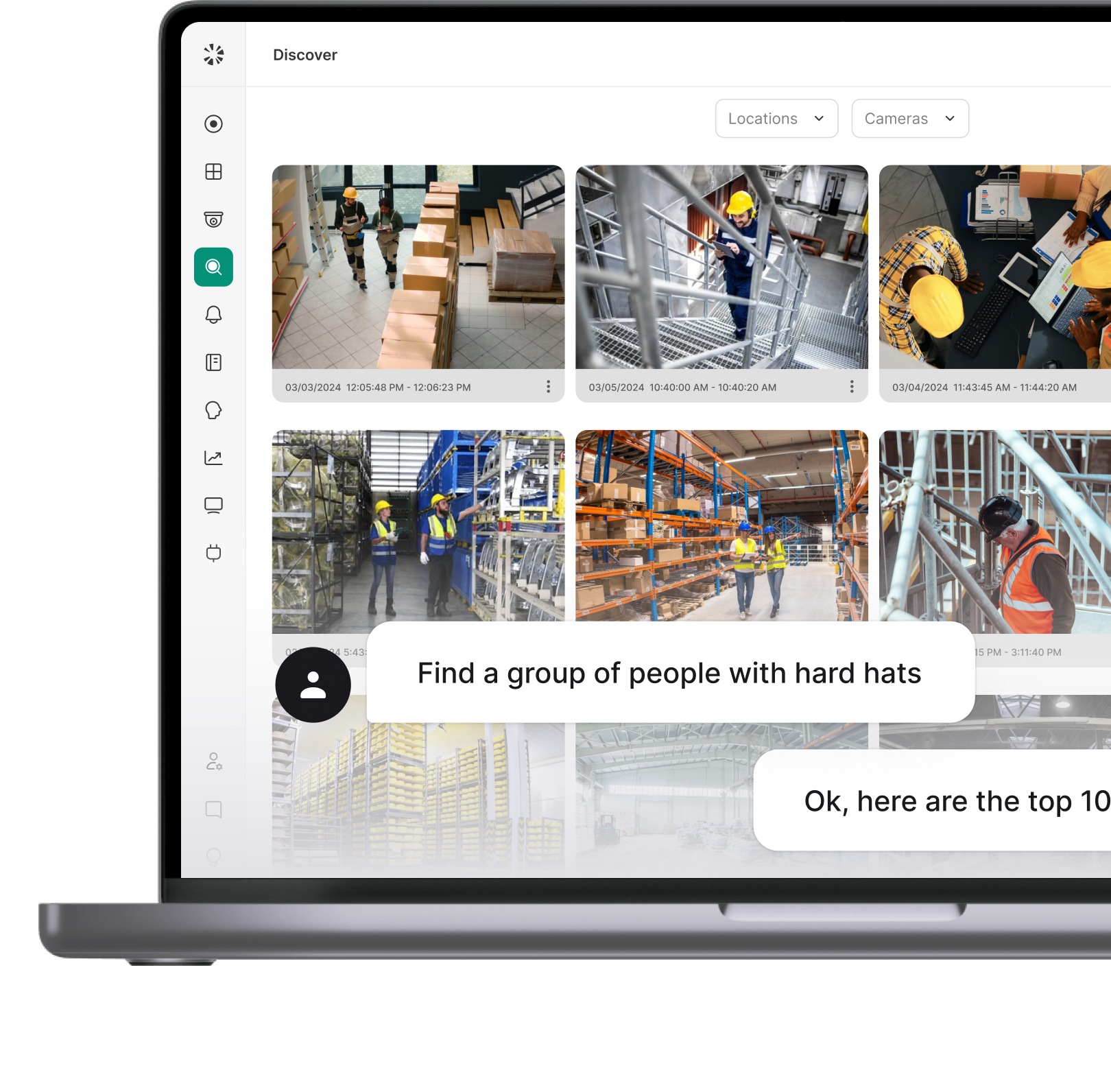
Choosing the Right Security Solutions
Selecting appropriate security systems requires matching capabilities to setting requirements. The wrong choice can mean either inadequate security or unnecessary complexity and cost.
What to Look For
When evaluating visitor management systems, prioritise real-time dashboards showing current visitors, photo capture and badge printing, pre-registration capability, host notification, automatic check-out prompts, compliance reporting, cloud-based operation with offline capability, and integration with access control.
For access control systems, look for audit trails of all access events, multiple credential types, temporary credentials for visitors, time-based access rules, emergency release capability, and integration with visitor management.
For CCTV, prioritise high resolution cameras suitable for identification, night vision for external cameras, remote viewing capability, motion-activated recording, secure storage with appropriate retention, and integration with access events.
Questions to Ask Vendors
Before selecting a vendor, ask these questions: Does the system meet the specific requirements of early years settings? What training and implementation support is provided? How is data protected and where is it stored? What is the process for subject access requests? How does the system perform during internet outages? What is the ongoing cost structure including support and updates? Can the system integrate with existing access control or CCTV? What compliance certifications does the vendor hold?
Implementation Considerations
Test new systems in one area before rolling out across the setting. Identify issues and refine procedures before full implementation. Budget time for thorough staff training because a system that staff cannot use correctly provides no security benefit. Inform parents before introducing new security measures and explain the purpose. Update relevant policies to reflect new systems and procedures.
Conclusion
Meeting EYFS security requirements involves more than having policies on paper. It requires physical security infrastructure, consistent procedures, trained staff, and proper documentation. The shift from paper-based systems to digital security tools reflects the increasing complexity of safeguarding requirements and the need for reliable, auditable records.
That said, the right approach depends on your setting's specific circumstances. Some organisations prioritise an all-in-one security ecosystem, while others prefer to enhance their existing camera and access infrastructure with modern management tools. In either case, the goal is the same: creating a secure environment where children are protected and compliance is straightforward to demonstrate.
Start by assessing your current arrangements against the checklist in this guide. Identify gaps and prioritise actions based on risk. Implement changes systematically, ensuring staff are trained and procedures are documented. Security is not a one-time project. Review arrangements regularly, learn from incidents and near misses, and update systems as requirements evolve.
FAQ
The EYFS framework requires providers to take reasonable steps to ensure children's safety, ensure no unauthorised person has unsupervised access, and have emergency procedures in place. Specific measures like CCTV or electronic access control are not legally mandated but support compliance with these requirements.
No. CCTV is not a legal requirement. However, it is widely used and can support compliance with safeguarding requirements. If you do not have CCTV, you should be able to demonstrate how you monitor premises security through other means.
Section 3 of the EYFS framework covers safeguarding and welfare. Requirements include ensuring staff suitability, promoting health and safety, managing behaviour, maintaining safe premises, and having appropriate policies and procedures. Security measures support several of these requirements.
Risk assessments should be reviewed at least annually. They should also be reviewed after any security incident, following significant changes to premises or procedures, and when external risk factors change.
Providers must know who is on the premises at any time. This requires a system for logging visitor arrivals and departures. While paper logs can meet the basic requirement, digital systems provide more reliable and accessible records.
No. Visitors who are supervised at all times and have no opportunity for unsupervised contact with children do not require DBS checks. Regular visitors who may have unsupervised access should be checked. Document your approach in your safeguarding policy.
There is no statutory requirement specifying retention periods for visitor records. A common approach is to retain records for 12 months, which supports incident investigation while limiting data retention. Define your retention period in your data protection documentation.




.webp)