When it comes to video surveillance, traditional systems record what happened. However, they fail to detect who it was. As a result, when a restricted area is accessed or a flagged individual enters the premises, security teams often rely on manual footage review after the incident.
In high-traffic environments such as corporate offices, hospitals, campuses, or multi-location enterprises, this delay creates a real operational gap. This becomes critical because knowing exactly who is on-site, and in real time, is a growing security priority for organizations.
This is exactly where face recognition video surveillance becomes relevant. By automatically detecting and matching faces against approved or watchlisted databases, it enables faster identification and more informed response decisions.
In this blog, we'll explain how face recognition video surveillance works and where it is most commonly used, so you can evaluate whether it fits your security and privacy framework.
What is Face Recognition Video Surveillance?
Face recognition video surveillance is a biometric security technology that identifies or verifies a person using their facial features. It works like an automated face scanner. The system detects a face within a frame, maps distinct facial features, and converts them into a digital template. That template is then compared against pre-enrolled profiles to confirm or deny identity.
Facial recognition technology falls under the broader category of biometric security technologies, which also includes fingerprint recognition, voice recognition, and iris or retina scanning. However, what differentiates it is that it can work passively through existing camera infrastructure, often without requiring any physical contact or active participation.
Interestingly, while the technology has long been associated with security and law enforcement use cases, it is increasingly being preferred by enterprises, campuses, and even commercial facilities looking to strengthen identity verification within their video surveillance systems.
How Face Recognition Video Surveillance Works
Face recognition video surveillance operates through a structured biometric processing pipeline. Each stage performs a defined technical function that moves the system from raw video input to identity verification and response. Here's what the process looks like:
Step 1: Image/Video Capture
The process starts with continuous video input from connected IP cameras. As individuals move through monitored areas, the cameras capture live streams or recorded footage. At this stage, the system is simply collecting visual data. However, image resolution, lighting conditions, and camera placement directly influence recognition accuracy later in the process.
Step 2: Face Detection
Once video frames are captured, the system applies computer vision algorithms to determine whether a human face is present. The software first isolates facial regions from the surrounding environment. If multiple individuals appear in a single frame, each face is detected separately. In this way, detection acts as a validation filter before identification begins.
Step 3: Feature Extraction and Faceprint Creation
After confirming the presence of a face, the system analyzes specific facial landmarks. These include measurable spatial relationships such as the distance between the eyes, the contour of the jawline, the position of the nose, and overall facial geometry. The system then converts these measurements into a mathematical template known as a faceprint.
Step 4: Database Matching
The generated faceprint is then compared against stored templates within a facial recognition database. Each comparison produces a similarity score that represents how closely the captured face matches a stored profile. Organizations configure a predefined confidence threshold to determine what qualifies as a valid match:
- If the similarity score is below the threshold, no identification is confirmed.
- If the score meets or exceeds the threshold, the system confirms a match.
Basically, this step transforms biometric data into an identity decision.
Step 5: Alert/Action
Finally, when a confirmed match occurs, the system triggers a predefined response based on configured rules. Some common responses include:
- Real-time alerts to security teams
- Event logging for compliance and audit tracking
- Notifications to administrators
- Integration with access control systems to grant or deny entry
The full sequence (capture, detection, encoding, matching, and response) occurs within seconds. This structured workflow enables face recognition video surveillance to function as an identity-verification layer within a broader security infrastructure.
Real-Time vs. Post-Event (Forensic) Analysis
Face recognition video surveillance can work in two primary modes: real-time identification and post-event (forensic) analysis. However, your choice between them depends on your organization's risk profile and operational priorities.
1. Real-Time Recognition
In real-time mode, faces are analyzed as individuals appear on camera. The system immediately generates a faceprint, compares it against the database, and triggers alerts if a match meets the defined confidence threshold. All in all, the real-time mode focuses on prevention and immediate action.
2. Post-Event (Forensic) Analysis
In forensic mode, facial recognition is applied to recorded footage after an incident has occurred. Hence, security teams can search historical video using a face image or profile and retrieve all instances where that person appeared. Eventually, this mode focuses on investigation and traceability.
Where is Face Recognition Video Surveillance Used?
Face recognition video surveillance is usually deployed in environments where identity verification must happen quickly, consistently, and at scale. Here are some of the most common face recognition use cases where this technology is actively used:
1. Airports and Aviation Infrastructure
Airports operate under strict security mandates while simultaneously managing high passenger volumes. As a result, identity verification must be both accurate and efficient. To achieve this, facial recognition is used to:
- Streamline passenger identity checks at checkpoints
- Monitor restricted staff-only areas
- Detect individuals on security watchlists
- Reduce manual document verification
Since aviation environments involve layered security protocols, biometric video surveillance often supports broader identity management systems rather than functioning in isolation.
2. Government and Public Institutions
Government facilities face higher security risks while also handling a constant flow of visitors, staff, and officials. In such environments, facial recognition maintains controlled access and monitors potential threats by tracking flagged individuals at entry points, managing internal watchlists, quickly searching video archives during investigations, and securing sensitive areas.
3. Industrial and Manufacturing Facilities
Industrial enterprises face a different type of risk. Here, the focus is more on preventing unauthorized access, ensuring workforce authentication, and protecting critical infrastructure. For this reason, facial recognition is commonly integrated at entry gates or secure zones to verify employee identity.
4. Financial Institutions
Financial institutions operate within highly regulated environments where identity verification directly impacts fraud prevention and compliance. Accordingly, facial recognition is used to verify customers during high-value transactions, monitor access to restricted operational areas, or identify individuals previously flagged for risk-related concerns.
Benefits of Face Recognition in a Security System
Once facial recognition is enabled, the system can associate footage with specific individuals and apply rules around that identity. That shift has the following benefits for how security is managed day to day:
1. Immediate Identification of Flagged Individuals
In many facilities, the primary risk comes from previously flagged individuals attempting to return. By using facial recognition, the system automatically checks incoming faces against a predefined database and triggers instant alerts if a match is found. As a result, security teams can respond in real time instead of identifying the person later through manual footage review.
2. Reduced Dependence on Physical Credentials
Although access cards and badges are widely used, they can still be shared. A person can hand their badge to someone else, intentionally or not, and the system has no way to verify who is actually entering. Facial recognition solves this problem by tying access to the individual rather than to a device. Even if cards remain part of the workflow, biometric verification adds an additional control point.
3. Faster Investigations
When an incident occurs, one of the first questions is: where else has this person appeared?
Manually answering this can require hours of video review across multiple cameras. With facial recognition, security teams can search by profile and retrieve all matching appearances within seconds. This reduces investigation time and improves documentation quality, especially in regulated environments.
4. Better Visibility Across Large or Multi-Location Sites
As facilities grow, maintaining visibility across every entrance and hallway becomes difficult. Staffing does not always scale with infrastructure, but facial recognition solves that problem by automatically grouping appearances of the same individual across different cameras and locations. This way, security teams can focus on alerts and exceptions.
Regulatory and Legal Landscape for Face Recognition
While the legal landscape for facial recognition continues to change, there is already a substantial compliance framework in place. For instance, in the U.S., there are no nationwide facial recognition regulations. Instead, compliance obligations are shaped by a combination of federal privacy rules and state-specific biometric regulations.
One of the most influential laws is the Illinois Biometric Information Privacy Act (BIPA). Although it is a state law, its impact extends nationally because it applies to companies that collect biometric data from Illinois residents. BIPA requires:
- Explicit written consent before collecting biometric identifiers
- Clear disclosure of purpose and retention timelines
- Strict data storage and destruction policies
Non-compliance has led to significant class-action litigation, which makes BIPA a major risk consideration for enterprises operating across states.
The Future of Face Recognition in Security
Based on a recent research study, it has been found that the next phase of evolution will focus less on improving benchmark scores and more on strengthening systems against deliberate interference. Here are some points to consider with respect to that:
1. Robustness Will Matter More Than Raw Accuracy
Modern face recognition models perform well in clean environments. But with carefully designed perturbations, the accuracy can drop. That's why performance alone is not enough. Going forward, systems will need to be evaluated not just on how accurately they recognize faces, but also how reliably they perform when someone is actively trying to deceive them.
2. Multi-Layer Identity Verification Will Become More Common
As vulnerabilities in single-channel biometric systems become clearer, relying exclusively on facial recognition may be insufficient in higher-risk environments. Therefore, we may see greater use of layered authentication models. For this, facial recognition may be more actively combined with badge validation, behavioral analytics, or other biometric factors.
3. Evaluation Standards Will Evolve
Another major shift will happen in how systems are evaluated. In addition to accuracy in normal conditions, security teams may also start assessing:
- Reliable performance even when lighting, camera angles, or surroundings change
- Ability to handle attempts to trick or manipulate the system
- Steady accuracy across different faces, expressions, and appearances
In other words, future deployment decisions will likely include resilience testing as a core requirement.
Final Takeaway
Face recognition video surveillance is quickly becoming a core part of modern security strategies across various industries. It is already being integrated into complex national systems that link biometric data across agencies, which only shows how identification-based security is progressing with more unified identity frameworks.
Moving forward, the technology’s future will be shaped not only by technical improvements in accuracy and resilience, but also by how organizations manage privacy expectations, govern biometric data responsibly, and align security needs with the changing legal and ethical standards.
FAQ
Face detection identifies whether a human face is present in the footage. On the other hand, face recognition analyzes these identified facial features and matches them against a database to determine identity. All in all, detection finds a face and recognition verifies who it is.
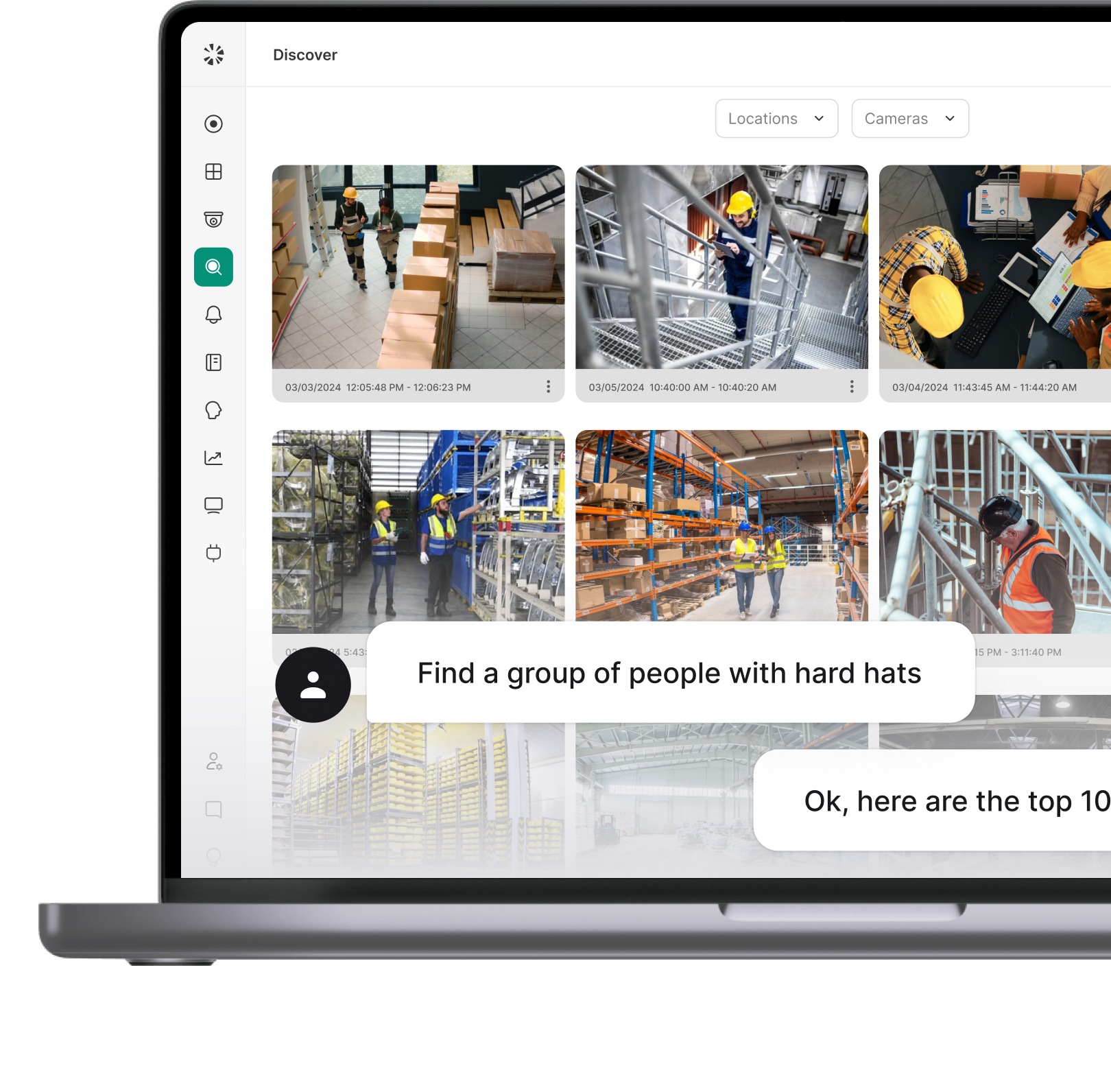
Yes, modern systems like Coram can analyze live video feeds and compare faces against stored profiles within seconds. Coram's AI uses proprietary foundation models running on Coram Point for edge-based detection, with data then sent to the cloud for further processing to reduce false positives. It can also trigger alerts immediately after a match meets a defined confidence threshold.
Under controlled conditions, leading models can achieve up to 99% accuracy. However, real-world performance varies based on lighting, camera angle, image quality, and occlusion. That's why accuracy also depends on database quality and system configuration.
Although there is no universal requirement as such, higher-resolution cameras with Full HD (1920x1080, or 2 megapixels) or higher usually work well. Proper camera placement, lighting, and achieving a sufficient pixels-per-foot ratio are equally important. For example, Coram recommends a minimum of 50 pixels per foot (PPF) for accurate face recognition.
Yes, it is legal in many parts of the U.S., but its use is regulated by federal, state, and local laws. While some states require explicit consent before collecting biometric data, certain cities restrict government deployment. Compliance depends on location and use case.
It depends on the system scale, number of cameras, database size, and integration requirements. The underlying expenses typically include software licensing, hardware infrastructure, and ongoing maintenance.