Six months after deploying a PIN-based access control system across a 400-person office, your security team starts noticing patterns. The same credential at the front door at 11 pm, three days in a row, for an employee who works mornings. A PIN shared between teammates because "it's just easier." A contractor whose access ended last quarter is still walking through restricted doors.
Nobody did anything malicious. The system worked exactly as designed. That's the problem.
The access control credential types you choose shape every interaction your employees, contractors, and security team have with your physical security infrastructure every day. How easy it is to abuse access, how much IT overhead you absorb, how useful your audit logs actually are, all of it flows from this one decision.
This guide covers how PIN, card, and mobile credentials compare across security, usability, and cost, and gives you a practical framework for choosing the right one, or the right combination, for your environment.
TL;DR
- PIN is simple and low-cost, but creates attribution gaps that matter in regulated or high-security environments
- Legacy 125 kHz cards are the most exploitable vulnerability in most existing access control systems
- Mobile credentials offer the lowest operational overhead at scale: provisioning, revocation, and management all happen remotely
- No single credential type works for every door: high-security zones warrant MFA regardless of what the rest of the facility runs
- Start with security requirements, layer in compliance and operational needs, and let budget be the last filter
What Are We Actually Comparing?
Before getting into trade-offs, it helps to be precise about what each credential actually is, because the category names get used loosely, and the technical differences matter when evaluating security and operational fit.
PIN (Personal Identification Number)
A PIN is a numeric code entered on a keypad to authenticate a user. It doesn't require a physical object; the user carries the credential in their memory.
PINs are typically 4 to 8 digits, though longer codes exist in higher-security deployments. They're the oldest form of electronic access credential still in widespread use.
Card (Key Card / Smart Card / Fob)
A card or fob is a physical token that communicates with a reader via radio frequency. Two technologies dominate this space:
125 kHz proximity cards (HID Prox, EM4100): the legacy standard, still installed in millions of buildings. Low-frequency, no encryption, readable from a distance with off-the-shelf equipment.
13.56 MHz smart cards (HID iCLASS, MIFARE DESFire): the modern standard. Higher frequency, encrypted communication, significantly harder to clone.
The distinction between these two matters more than most buyers realize at purchase time. "Card-based access control" can mean either one, and the security gap between them is substantial.
Mobile Credentials
Mobile credentials turn a smartphone into an access card. The phone communicates with the reader via Bluetooth Low Energy (BLE) or Near Field Communication (NFC), and the credential itself lives in a secure digital wallet on the device. Users authenticate at the door by tapping, waving, or, in some systems, simply walking up with their phone in their pocket.
Modern mobile credential platforms also support hands-free entry and can be provisioned or revoked remotely in seconds, with no physical badge to collect or keypad to reprogram.
A Note on Biometrics
Biometric credentials (fingerprint, facial recognition, iris scan) are intentionally excluded from this comparison as a standalone category. In enterprise environments, biometrics are most commonly deployed as a second factor alongside card or mobile, not as the primary credential at scale. The reasons are practical: biometric readers carry a higher per-door cost, privacy regulations around biometric data collection vary by jurisdiction and are evolving rapidly, and failure modes (wet fingers, lighting conditions, enrollment edge cases) introduce friction that most organizations reserve for their highest-security doors. Where biometrics appear in this guide, it's in the context of multi-factor authentication, which is where they add the most value.
How Secure Is Each Credential Type?
Each credential type fails differently. Understanding how each fails is what lets you design around the weaknesses.
PINs: The sharing problem you can't fully engineer away
When a PIN is used, the system records that the credential was presented. It has no way of knowing whether the right person presented it. Employees share PINs with colleagues. Contractors pass codes between team members. None of this appears in your access logs. In regulated industries or sensitive areas, that attribution gap is a direct compliance liability.
PINs also carry shoulder surfing risk: the code being observed during entry, which is a practical concern in busy lobbies, not a theoretical one.
Cards: Strong until they're not
Modern 13.56 MHz smart cards are genuinely difficult to compromise. The problem is that legacy 125 kHz proximity cards, still the majority of installed infrastructure globally, can be cloned in seconds using commercially available hardware costing less than $50. Security researchers have demonstrated this repeatedly, and the tools are readily available online with no specialized knowledge required.
If your organization is still running HID Prox or equivalent, your key card access control is weaker than your IT team's password policy.
Even with modern smart cards, a stolen badge grants access until someone reports it missing. In large organizations, that window can be hours or days.
Mobile: The strongest single-factor credential available today
Mobile credentials are cryptographically bound to a specific device. They can't be shared like a PIN or cloned like a proximity card.
The attack surface shifts from physical to digital; a compromised device or weak passcode creates exposure, but these are manageable with standard MDM policies most enterprise IT teams already enforce.
The practical concern for mobile deployments is coverage: BLE and NFC readers require compatible infrastructure, and not every facility has it.
What It's Actually Like to Use Each Every Day
Security specs matter. But the credentials your employees interact with dozens of times a day had better work well in practice because friction at the door compounds fast across a large workforce.
A five-second delay per entry across 500 employees is thousands of lost minutes daily.
Complaints pile up, workarounds get invented, and security gets bypassed in the name of convenience. Here's how each credential actually performs when real people use it, every day, across a real facility.
PIN: Simple until it isn't
The upside is obvious: nothing to carry, nothing to lose, nothing to forget at home. For low-traffic, low-security environments, PINs are frictionless.
The daily reality in larger deployments looks different:
- Entry slows down during peak hours when multiple people queue at a keypad
- Users forget codes after holidays, long weekends, or role changes
- Shared spaces with high turnover require frequent code rotation which means retraining
- Keypads wear visibly over time, physically revealing the most-used digits
For most enterprise environments, PIN-only entry creates a daily UX tax that compounds silently in the background.
Card: The familiar standard with a hidden cost
Cards are fast, tactile, and universally understood. Tap or wave, door opens. Most employees don't think twice about it, which is exactly why cards became the default credential for enterprise access control.
The friction shows up elsewhere:
- Forgotten badges at home mean help desk calls, temporary credentials, and someone's morning derailed
- Lost cards require physical replacement, sometimes days later, if the supply isn't managed well
- Visitors and contractors need physical badges issued and collected manually
- Employees carrying cards for multiple systems accumulate a wallet full of credentials with no unified management
Cards work well. The operational overhead of managing them at scale is where the cost hides.
Mobile: The highest ceiling, the steepest onramp
Once mobile credentials are set up and working, the daily experience is genuinely better than any alternative. Tap your phone, and the door opens. No badge to forget. Provisioning a new employee takes seconds. Revoking access for a contractor happens from a laptop, instantly, without anyone needing to physically collect anything.
The gaps worth knowing upfront:
- Onboarding requires app install, device enrollment, and user training: plan for a transition period with mixed populations
- A phone at 0% is a locked door: cards and PINs don't have battery dependency
- Older devices and personal device policies create gaps that need a fallback
- Hands-free entry via proximity can be a liability in high-security areas where you want deliberate authentication at every entry
What Each Credential Costs to Manage
The hardware cost of a keypad, a card reader, or a mobile-compatible reader tells you almost nothing about what that credential type will actually cost over three to five years.
The real cost lives in the operational layer: badge replacements, admin hours, help desk tickets, and the compliance exposure that comes from credential programs that aren't actively managed.
PIN: Low Upfront, Deceptively Expensive to Maintain
Keypads sit at the lower end of the reader price range, roughly $80 to $300 per unit, with no per-user credential cost. On a capital budget, PIN systems look very attractive.
The ongoing cost is harder to see:
- Every PIN reset or rotation consumes administrator time at scale
- Security best practice requires periodic rotation, but most organizations skip it because the lift is too high
- High-turnover environments mean constant re-issuance and retraining cycles
- Audit exposure grows quietly when PIN sharing goes undetected
Pro Tip: Calculate how many PIN resets your team processes per month. That number multiplied by admin time is your real credential cost.
Card: Predictable Unit Economics, Unpredictable Replacement Volume
Physical credentials run $5 to $50 each. Readers range from $80 to $1,200. The replacement cycle is perpetual and scales directly with headcount.
That's before visitor badges and contractor credentials. Organizations still on legacy 125 kHz face a full reader and credential replacement to move to encrypted smart cards, a project that routinely runs into six figures for mid-to-large facilities.
Pro Tip: Ask your installer whether existing Wiegand wiring can be reused. It can reduce total replacement costs by up to 35%.
Mobile: Higher Setup Cost, Lower Steady-State Overhead
Cloud-based mobile access control software runs $3.50 to $15 per door per month. The upfront investment is real. The steady-state economics look different:
- No physical badge inventory to manage
- Provisioning takes seconds from the dashboard
- Revocation is instant: access is gone before the employee leaves the building
- New hire credentials ready before day one
Where Mobile Breaks Even and Pulls Ahead
To make the comparison concrete, here's what a 500-person organization looks like over three years across each credential type:
The numbers shift significantly with scale. At 2,000 users, card replacement and admin costs roughly quadruple while mobile subscription costs stay flat per door. By year three, the gap widens further: cards get more expensive as you scale, and mobile gets cheaper.
Pro Tip: When evaluating mobile credential platforms, confirm whether mobile enrollment is included in the base subscription or billed separately. Some vendors price it as an add-on, which significantly changes the three-year cost calculation.
When One Credential Isn't Enough
Most credential decisions get framed as either/or. PIN or card. Card or mobile. The reality in enterprise environments is messier, and often, a single credential type leaves a gap that only a second layer can close.
Scenario 1: The healthcare facility fails its audit
A PIN-based medication storage room feels secure until an audit reveals three nurses sharing the same code. HIPAA requires individual attribution for every access event. A shared PIN makes that impossible. Card or mobile credentials tied to individual users restore the audit trail instantly.
Scenario 2: The data center with a tailgating problem
A card-only system logs every valid credential presented. It has no way of knowing whether one badge tap lets in two people. Card + PIN ensures the person holding the badge is the person who knows the code. Unauthorized attributed entry becomes significantly harder without adding meaningful friction for legitimate users.
Scenario 3: The high-security room where any single factor falls short
Mobile credentials authenticate the phone. Biometrics authenticate the person. For the small number of doors where unauthorized access carries severe consequences, pharmaceutical storage, executive floors, server rooms, mobile + biometric is the only combination that closes the gap.
The pattern across all three is the same. Before combining credentials, define the specific failure you're closing. MFA adds security and friction in equal measure. The right combination is the one that addresses the actual risk at that door, not the most secure option available on paper.
Which Credential Is Right for Your Organization?
The right credential depends on your users, what you're protecting, your facility structure, and your operational overhead capacity. There's no single answer.
Start with security requirements, and budget later
The credential type sets the ceiling on what your access control system can enforce. Define the minimum requirement for each zone first. Common areas have different requirements than server rooms or regulated storage.
If your workforce is stable and low-complexity, start simple
Single-site organizations with low turnover and no regulatory requirements don't need a mobile credential program. Encrypted smart cards cover the requirement without enrollment overhead.
If scale or multi-site management is the problem, mobile is the answer
Mobile credential economics become compelling once headcount crosses a few hundred users or access needs are being managed across multiple locations. Provisioning takes seconds. No badge inventory, no replacement cycle.
If compliance is driving the decision, individual attribution is non-negotiable
HIPAA, SOX, and FedRAMP require access events attributable to specific individuals. PIN-only access isn't viable regardless of cost. A card or mobile tied to individual profiles is the baseline. MFA is the standard for high-risk zones.
If your infrastructure is legacy, close the cloning gap first
Moving from 125 kHz to encrypted 13.56 MHz smart cards closes the most exploitable gap without replacing the entire infrastructure.
Three questions before you decide
How fast does your user base change? High turnover means constant card replacement costs. Mobile eliminates that cycle; if the answer is "frequently," the economics make the case.
What does your compliance framework require? If individual attribution is mandated, HIPAA, SOX, FedRAMP, PIN-only isn't viable. That requirement narrows the decision before anything else.
What happens when the credential fails? Cards get lost. Phones die. PINs get shared. Know your most likely failure mode before you deploy.
How Your Access Control Platform Shapes the Credential Decision
The credential conversation doesn't happen in isolation. The platform you run determines which credential types are available, how easily you can mix them, and what happens when requirements change.
Most access control platforms are built around a single credential type. Swap the credential, and you're often looking at a reader replacement or a new vendor entirely. That lock-in is one of the most common reasons organizations stay on legacy systems longer than they should.
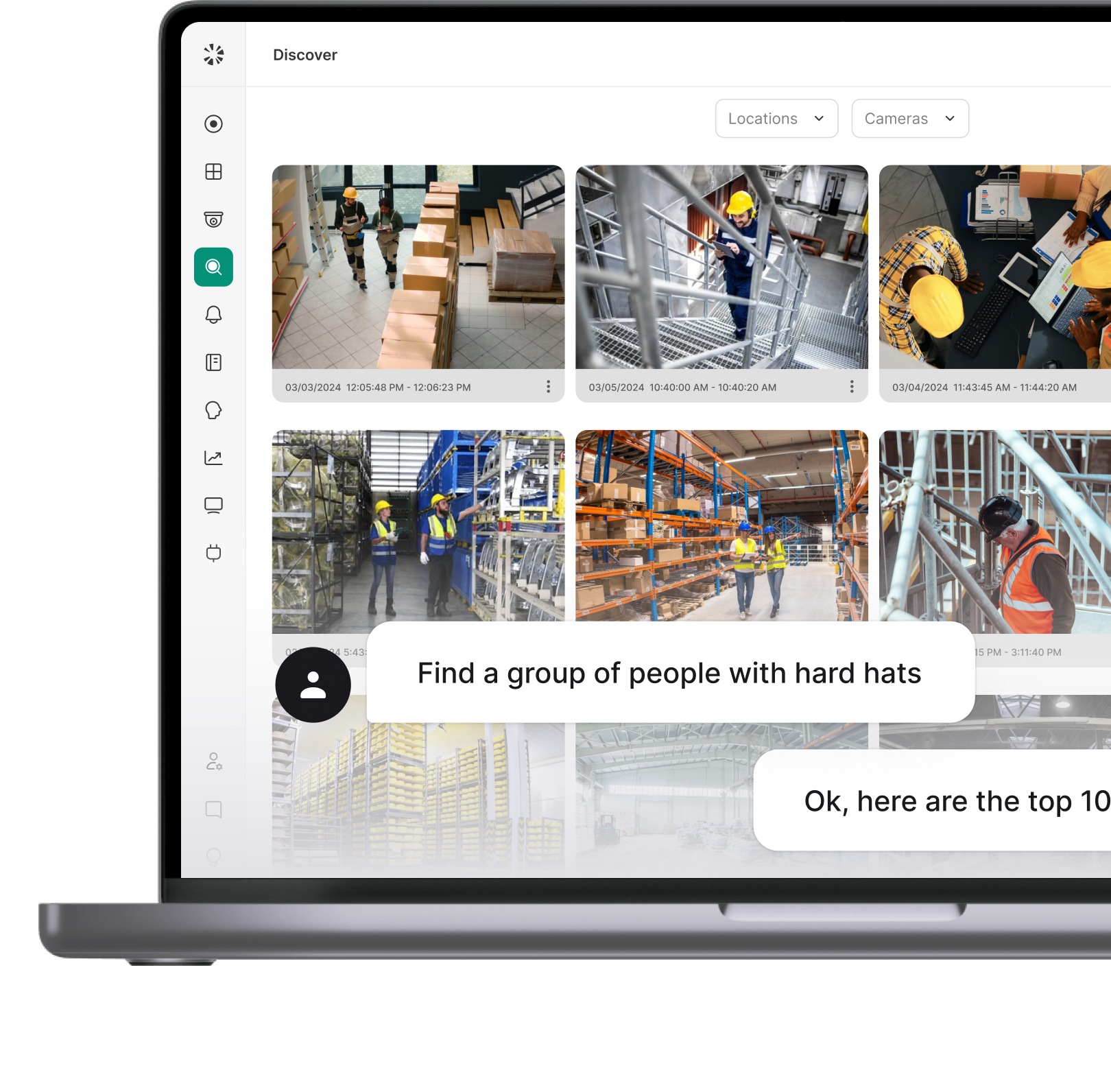
How Coram Supports All Three
Coram is credential-agnostic by design. PIN, card, and mobile credentials all run on the same platform, managed from the same dashboard, across every door and location.
One platform, any credential combination. Coram's DR-U1 reader supports 125 kHz and 13.56 MHz cards, mobile credentials via BLE and NFC, and PIN entry. Organizations can run different credential types across different zones without managing separate systems. A server room on card + PIN and a common area on mobile sit under the same access policy framework, with unified reporting across both.
Provisioning and revocation in seconds. New hires get credentials before day one. Terminated employees lose access before they leave the building. Contractor passes expire automatically at the end of an engagement. Everything happens from the Coram dashboard, remotely, without physical badge handling or admin desk involvement.
Every credential event is tied to video. Every access attempt, granted, denied, forced, or propped, is automatically paired with video from existing on-site cameras or Coram's own hardware. A credential event with visual context becomes evidence. Without it, it's just a log entry.
The platform supports the transition as requirements evolve. Organizations that haven't finalized their credential strategy don't need to before deploying Coram. Start with cards. Add mobile when the workforce is ready. Apply MFA to high-risk zones as requirements grow. The platform supports that progression without a rip-and-replace cycle at each stage.
If you're evaluating credential types alongside an access control platform, book a demo to see how Coram works across your doors and locations.
The Bottom Line on Access Control Credentials
No credential wins across every environment. PIN works at a small scale with stable users. Cards are reliable but carry a replacement burden that compounds with headcount. Mobile offers the best operational economics at scale but requires infrastructure investment and a managed transition.
If you're setting up a new system today, build for mobile. If you're upgrading, close the legacy card vulnerability first. If you're in a regulated environment, individual attribution requirements make the decision before the budget does.
Coram supports all three on a single platform. Book a demo to see how it works across your doors and locations.
FAQ
Smart cards remain the most widely deployed credential type in enterprise environments. Most large organizations standardized on card-based access control over the past two decades, and that installed base is still the majority.
Mobile credentials are gaining ground, particularly in organizations upgrading legacy infrastructure or deploying new systems, but cards still dominate in active use today.
Yes, and most mid-to-large enterprises do. Modern platforms support multiple credential types across different doors, zones, or user groups from a single interface.
A common setup runs mobile for the general workforce, card plus PIN for restricted areas, and a temporary PIN for contractors. The readers and platform need to support the credential types you want to run: hardware-agnostic platforms handle this without requiring separate systems for each.
No. Mobile credentials offer better operational efficiency at scale. Cards are reliable but carry replacement overhead and physical theft risk. PINs are simple to deploy but create attribution gaps that matter in regulated environments.
The right choice depends on your security requirements, compliance obligations, workforce profile, and infrastructure.
Mobile credentials handle multi-site management better than cards or PINs. Provisioning and revocation happen remotely, there's no physical badge inventory to manage across locations, and access policy changes apply instantly across every site from one dashboard.
Organizations with legacy infrastructure or mixed workforces often run mobile for the core workforce with card or PIN as a fallback while transitioning.
The cleanest path is phased migration. Start by identifying which doors and zones carry the highest security risk and upgrade those readers to 13.56 MHz or multi-technology readers first. Many modern readers (including Coram's DR-U1) support both 125 kHz and 13.56 MHz simultaneously, so employees can continue using existing badges during the transition while new credentials are rolled out zone by zone. Pair the reader upgrade with a credential swap schedule tied to natural replacement points: new hires get smart cards or mobile from day one, existing employees swap at badge renewal. Most organizations complete a full migration in three to six months without a single day of disrupted access.
Both are wireless protocols used to communicate between a phone and a door reader, but they work differently. NFC requires the phone to be within a few centimeters of the reader, similar to tapping a contactless payment.
BLE has a longer range (up to several meters), which enables hands-free entry where the door unlocks as you approach with your phone in your pocket. Most modern mobile credential platforms support both, and the choice between them often comes down to the security posture of the specific door: NFC for areas where deliberate intent to enter matters, BLE for high-traffic entries where speed is the priority.