If you are evaluating facial recognition for retail security, you have probably noticed every vendor claims to offer AI-powered loss prevention. The feature pages look the same. The demos show the same workflows. And after three sales calls, it is still unclear which system actually stops theft versus which one generates alerts no one acts on.
The technology has also moved. In 2026, facial recognition in retail is not experimental. Major grocery chains, big-box retailers, and specialty stores are running it in production. The question is no longer whether the technology works. It is whether your deployment will integrate with your existing security infrastructure, meet privacy requirements in your jurisdiction, and deliver ROI your finance team can measure.
This guide breaks down how facial recognition security systems work in retail environments, which features separate real platforms from glorified databases, and how to evaluate solutions based on your loss prevention priorities rather than vendor marketing.
TL;DR
- Facial recognition in retail identifies known shoplifters, organized retail crime (ORC) members, and persons of interest before they reach the sales floor
- The technology exists in two forms: bolted-on solutions that layer recognition onto existing cameras, and camera-native platforms where AI is built into the architecture
- Foundation capabilities include real-time alerts, watchlist management, and integration with existing security cameras. Advanced systems add behavioral analytics, POS integration, and cross-location identification
- Privacy compliance is non-negotiable. BIPA, state biometric laws, and GDPR create legal obligations that vary by jurisdiction and require consent workflows, data retention policies, and audit trails
- ROI comes from shrinkage reduction, not alert volume. The systems that deliver results connect recognition events to actual theft prevention outcomes
What is Facial Recognition Security in Retail?
Facial recognition security in retail uses AI-powered cameras to identify individuals as they enter a store, then match their face against a database of known persons of interest. When the system finds a match, it sends a real-time alert to loss prevention staff.
The database typically includes three categories:
- Known shoplifters: Individuals previously caught stealing at your location or shared across a retail network
- ORC suspects: Members of organized retail crime rings identified by law enforcement or retail associations
- Banned individuals: Former employees, people with restraining orders, or anyone the store has formally trespassed
This is fundamentally different from traditional security cameras. A standard CCTV system records footage for after-the-fact investigation. By the time loss prevention reviews the tape, the merchandise is gone. Facial recognition shifts the intervention point from investigation to prevention.
The operational difference is significant. Instead of catching theft on video, staff receive an alert while the person of interest is still in the lobby. That changes the calculus entirely: a store associate can provide customer service attention that discourages theft, or loss prevention can monitor the individual in real time.
How Retail Facial Recognition Systems Work
The technology operates in four stages: capture, extraction, matching, and alerting.
Stage 1: Face Capture
Cameras positioned at store entrances capture video of every person who walks in. The system isolates individual faces from the video stream, even in crowds, poor lighting, or partial occlusion scenarios.
Camera placement matters more than most vendors admit. A camera mounted too high captures the top of heads. A camera with insufficient resolution cannot extract the facial detail needed for accurate matching. The best systems specify exact mounting heights, angles, and minimum resolution requirements during site planning.
Stage 2: Feature Extraction
The AI analyzes each captured face and converts it into a mathematical representation called a faceprint or embedding. This is not a photograph. It is a set of numerical values that describe the unique geometry of the face: the distance between eyes, the shape of the jawline, the proportions of facial features.
The faceprint is what gets stored and compared. This distinction matters for privacy compliance. Systems that store actual photographs create different legal obligations than systems that store only mathematical representations.
Stage 3: Database Matching
The extracted faceprint is compared against the watchlist database in real time. Modern systems complete this comparison in under two seconds, even with databases containing thousands of enrolled faces.
Matching accuracy depends on two metrics:
- True positive rate: How often the system correctly identifies someone on the watchlist
- False positive rate: How often the system incorrectly flags someone not on the watchlist
High-quality systems achieve true positive rates above 99% with false positive rates below 0.1%. Low-quality systems generate so many false alerts that staff stop responding to them. The alert fatigue problem has killed more facial recognition deployments than any technical limitation.
Stage 4: Real-Time Alerting
When a match occurs, the system sends an alert to designated personnel. The alert typically includes the matched photograph, the watchlist category, the confidence score, and the camera location.
Alert delivery channels vary by platform: mobile app notifications, SMS, email, integration with existing security operations software, or direct feeds to security operations centers. The channel matters less than the response workflow. A system that sends alerts no one sees is operationally equivalent to having no system at all.
Core Features of Retail Facial Recognition Platforms
Not every feature matters equally for every retailer. This section organizes capabilities into three tiers: Foundation features every system should have, Advanced features that separate platforms from point solutions, and AI-Powered features that define the 2026 state of the art.
Foundation Features
Real-Time Alerts: The system notifies staff the moment a watchlist match occurs. Alerts should include the matched image, confidence score, and camera location. If alerts arrive five minutes after the person entered, the system is not real-time.
Watchlist Management: Staff can add, edit, and remove individuals from the watchlist without IT involvement. The interface should support bulk uploads for retail networks sharing ORC intelligence. Permissions should control who can add versus who can only view.
Integration with Existing Cameras: Most retailers have existing security camera infrastructure. A facial recognition system that requires ripping out and replacing all cameras is a non-starter for most deployments. Look for systems that work with your current camera brands and models.
Audit Trail: Every recognition event, every watchlist change, and every alert response should be logged with timestamps and user attribution. This is not optional. Compliance investigations, legal proceedings, and internal reviews all require a complete audit trail.
Confidence Thresholds: The system should allow configurable confidence thresholds for triggering alerts. Setting the threshold too low generates false positives. Setting it too high misses real matches. The right threshold depends on your operational tolerance for each.
Advanced Features
Cross-Location Identification: An individual added to the watchlist at one store is automatically flagged at all stores in the network. For multi-location retailers, this is the difference between isolated incidents and coordinated loss prevention.
POS Integration: The system connects facial recognition events to point-of-sale transactions. When a known shoplifter is in the store, loss prevention can see which register they approach and monitor the transaction in real time. Post-incident, investigators can pull the exact transaction associated with a recognition event.
Video Management Integration: Recognition events link directly to recorded footage. Clicking on an alert pulls up the video of that person entering the store. Investigation time drops from hours to minutes.
Access Control Integration: For retailers with restricted areas (stockrooms, pharmacies, cash offices), facial recognition can trigger or deny access. A flagged individual approaching a controlled door generates an alert before they attempt entry.
Mobile Application: Loss prevention managers receive alerts on their phones, not just desktop monitors. This matters for retailers where LP staff roam the floor rather than sitting in a security office.
AI-Powered Features
Behavioral Analytics: Beyond identifying who someone is, the system analyzes what they are doing. Loitering in high-theft areas, repeated visits without purchases, movement patterns consistent with scouting behavior. These signals create alerts for people not yet on any watchlist.
Demographic Filtering: Some systems can filter alerts by estimated age, gender, or other attributes. This is controversial and banned in some jurisdictions. Retailers considering this capability need to evaluate legal compliance in every location where they operate.
Anomaly Detection: The AI flags unusual patterns that rule-based systems miss. A person who checks out at multiple registers in sequence. Someone who enters and exits repeatedly without making purchases. Behavior that deviates from normal shopping patterns.
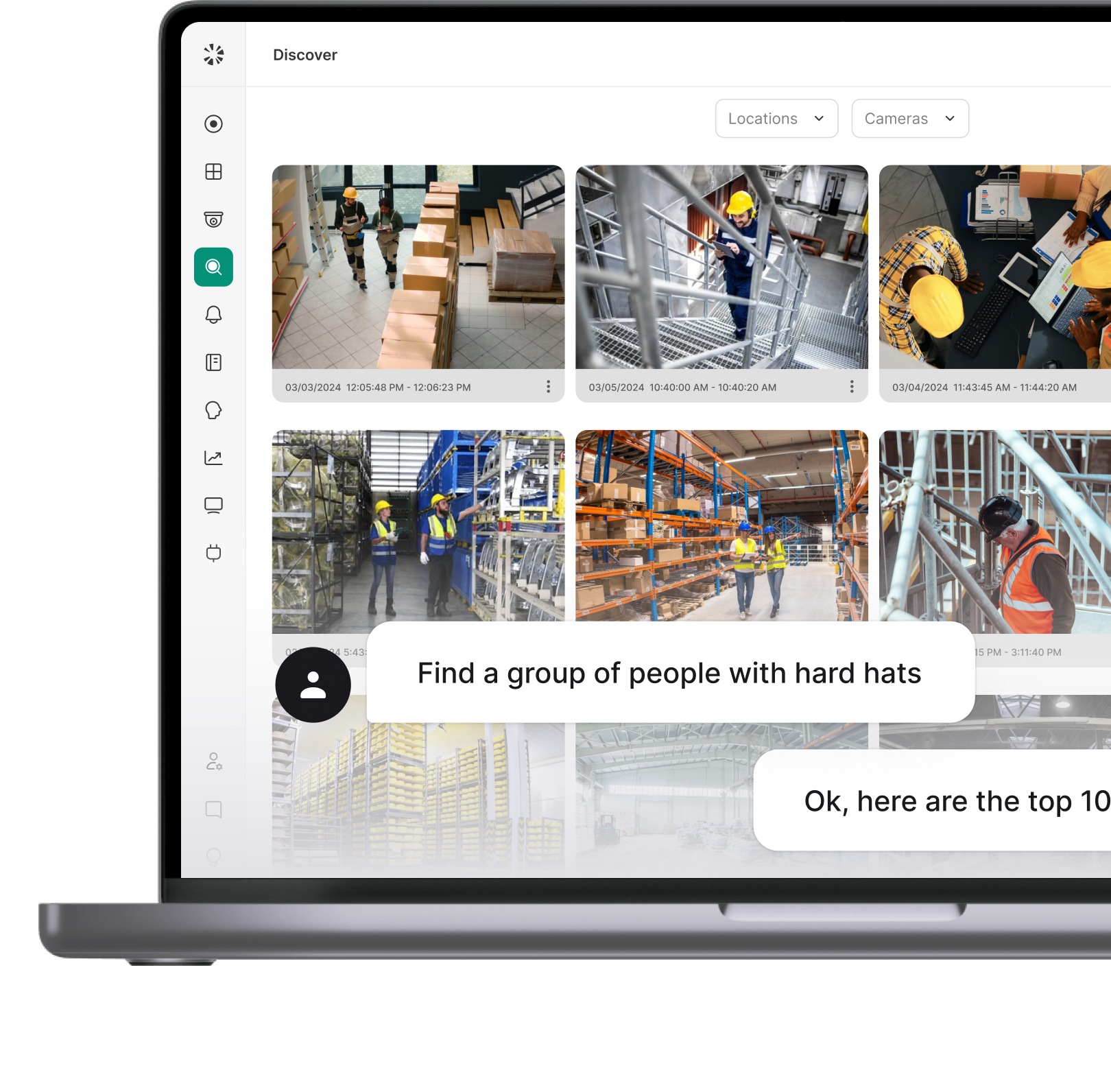
Natural Language Search: Security teams query the system conversationally. Instead of filtering through menus, an investigator types "show me everyone who entered through the east entrance yesterday between 2pm and 4pm" and gets results immediately.
Federated Learning: The system improves recognition accuracy over time without sending raw facial data to a central server. Privacy-preserving AI that gets better without compromising data residency requirements.
Feature Comparison by Retail Environment
Different retail environments have different security priorities. A grocery store chain optimizing for ORC prevention has different requirements than a luxury retailer focused on VIP recognition. The table below maps features to retail verticals.
A few patterns stand out. Cross-location identification is critical for grocery and big-box retailers because ORC rings target multiple stores. VIP recognition matters most for luxury retail where personalized service drives revenue. Behavioral analytics is universally important but becomes critical in environments where preventing theft before it happens matters more than catching it afterward.
Privacy and Legal Compliance
Facial recognition in retail operates under a patchwork of federal, state, and local regulations. Getting this wrong creates legal liability that can dwarf any loss prevention savings.
Illinois BIPA
The Illinois Biometric Information Privacy Act requires explicit written consent before collecting biometric data, including faceprints. Retailers operating in Illinois must obtain consent from every individual scanned, which creates operational complexity for traditional retail environments. Violations carry statutory damages of $1,000 to $5,000 per incident.
Several major retailers have faced class action lawsuits under BIPA. The compliance approach typically involves signage at entrances, employee training on the consent process, and systems that can exclude individuals who do not consent.
State Biometric Laws
Texas, Washington, and other states have enacted biometric privacy laws with varying requirements. Some require consent. Some require only notice. Some apply only to commercial use. The obligations differ enough that a compliance strategy for one state may be insufficient for another.
Multi-state retailers need a system that can implement different consent and notice workflows by location. A single national policy will either be over-restrictive in permissive states or non-compliant in strict states.
GDPR
For retailers operating in Europe, GDPR classifies biometric data as a special category requiring explicit consent and a lawful basis for processing. Data retention limits apply. Subject access requests must be honored. Cross-border data transfer rules may restrict where faceprint data can be stored and processed.
Building a Compliant Deployment
Compliance is not a feature checkbox. It is an operational program. The elements include:
- Clear signage at all entrances where facial recognition is active
- Documented consent workflows where required by law
- Data retention policies that auto-purge records after the legally permitted period
- Access controls limiting who can view and modify watchlist data
- Audit trails documenting every data access event
- Regular privacy impact assessments as the deployment scales
Implementation Considerations
A facial recognition deployment is a security infrastructure project, not a software installation. The difference between a system that delivers results and one that becomes expensive shelfware usually comes down to implementation decisions made before the first camera goes live.
Camera Requirements
Facial recognition requires higher resolution and more specific placement than general surveillance. Minimum requirements typically include:
- 1080p resolution minimum, 4K recommended for larger capture zones
- Mounting height of 7 to 9 feet to capture faces rather than heads
- Adequate lighting or IR capability for low-light environments
- Frame rates of at least 15 fps to capture moving subjects
Vendors should provide a site assessment that specifies exact camera requirements before deployment begins. A vendor that skips the site assessment is setting up the deployment to underperform.
Network Infrastructure
Facial recognition systems generate significant data traffic, especially when running AI inference at the edge. Network requirements include:
- Dedicated VLAN for security camera traffic
- Sufficient bandwidth for simultaneous streams from all recognition cameras
- Low latency connections to cloud services if using cloud-based matching
- Redundancy for business-critical alerting pathways
Staff Training
Technology only works if staff know how to use it. Training should cover:
- How to respond to alerts (approach protocols, escalation procedures)
- Watchlist management procedures (who can add, what documentation is required)
- Privacy compliance requirements (consent procedures, customer inquiries)
- False positive handling (how to verify matches before taking action)
Measuring ROI
The business case for facial recognition in retail is shrinkage reduction. But measuring that reduction requires connecting system activity to loss prevention outcomes.
Metrics That Matter
Recognition Rate: What percentage of watchlist individuals entering the store are successfully identified? This measures whether the system is doing its primary job.
Alert Response Rate: What percentage of alerts result in staff action? A system generating alerts no one responds to is not preventing theft.
Intervention Rate: How often does staff engagement with an alerted individual prevent a theft that would otherwise have occurred? This is the hardest metric to measure but the most important.
Shrinkage Delta: Comparing shrinkage rates before and after deployment, controlling for other variables. This is the bottom-line metric that finance teams care about.
False Positive Rate: How often does the system generate alerts for individuals not on the watchlist? High false positive rates destroy staff trust in the system.
Building the Business Case
A realistic business case includes:
- Current shrinkage rate and dollar value
- Expected reduction based on comparable deployments (vendors should provide case studies)
- Total cost of ownership including hardware, software, implementation, and ongoing operations
- Payback period based on conservative shrinkage reduction estimates
- Qualitative benefits: staff safety, customer experience, reduced investigation time
Five Questions That Expose What Vendors Will Not Volunteer
Vendor demos follow vendor scripts. These questions put the evaluation back on your terms.
1. "Show me the false positive rate from a production deployment, not a lab test." Lab accuracy and real-world accuracy are different. A vendor who can only cite lab numbers is not ready for production deployment. Ask for metrics from a comparable retail environment.
2. "What happens when your system flags someone and they turn out not to be on the watchlist?" This tests the false positive handling workflow. There should be a clear process for staff to mark false positives, and those errors should feed back into system improvement.
3. "Walk me through your compliance posture for Illinois BIPA and California CCPA." If the vendor cannot articulate a clear compliance approach for the strictest jurisdictions, they are leaving legal risk on your plate.
4. "Show me the integration with my existing VMS and access control system." Replace the generic system names with your actual vendors before the demo. A live integration demonstration is categorically different from a slide about API capabilities.
5. "What is your roadmap for addressing the bias concerns documented in NIST testing?" Facial recognition accuracy varies by demographic. Vendors should have a clear answer for how they address this, whether through training data diversity, bias testing, or other technical approaches.
Deploy Smarter, Prevent More
Facial recognition in retail is no longer experimental technology. It is production infrastructure running in stores across the country. The question for loss prevention teams is not whether to evaluate it, but how to evaluate it against the specific requirements of their environment.
The framework in this guide exists to structure that evaluation:
- Foundation features are table stakes. A system that fails on real-time alerting or watchlist management is not worth evaluating further.
- Advanced features determine whether the system integrates into your existing security infrastructure or operates as an isolated tool.
- AI-powered features define the ceiling of what the system can do without manual intervention.
- Privacy compliance is not optional. Get it wrong and the legal exposure dwarfs any loss prevention savings.
Coram brings video security, facial recognition, and AI-powered analytics into a single platform. The integrations that other systems treat as professional services projects are built into the architecture from day one. For loss prevention teams ready to move beyond legacy CCTV, that architectural difference shows up immediately in deployment speed, operational efficiency, and measurable shrinkage reduction.
FAQ
Yes. Major grocery chains, big-box retailers, convenience stores, and pharmacies have deployed facial recognition for loss prevention. Most do not publicize the deployments, but ACLU investigations and news reports have documented systems at numerous national retailers.
Cameras at store entrances capture faces of everyone who enters. The system compares each face against a watchlist of known shoplifters and ORC members. When a match occurs, loss prevention staff receive an alert with the individual's photo, watchlist category, and location. Staff can then monitor the individual or provide heightened customer service to deter theft.
Legality varies by jurisdiction. In most US states, retailers can use facial recognition with appropriate notice to customers. Illinois requires explicit written consent under BIPA. Several other states have enacted or are considering biometric privacy laws with varying requirements. Retailers must evaluate compliance in each jurisdiction where they operate.
Facial detection identifies that a face is present in an image. Facial recognition identifies whose face it is by matching against a database. Detection is a prerequisite for recognition, but detection alone does not identify individuals.
Top-tier systems achieve true positive rates above 99% and false positive rates below 0.1% under optimal conditions. Real-world accuracy depends on camera quality, lighting, mounting angle, and the size of the watchlist database. Accuracy also varies by demographic, which has raised concerns about bias. NIST publishes benchmark testing that compares vendor performance.




.webp)