Ask five people what a system administrator does, and you’ll get five different answers. That’s not because the role is poorly understood; it’s because the role genuinely varies that much depending on the environment, the organisation, and the year someone last updated their job description.
At its most fundamental level, a system administrator keeps the IT infrastructure running. Servers stay up, users get access to what they need, systems stay patched and secure, and when something breaks, someone fixes it fast. That core hasn’t changed.
What has changed is everything around it. Infrastructure now stretches across cloud platforms, virtual machines, containerised workloads, and hybrid environments. Security is no longer a shared contribution; it’s an infrastructure-level responsibility. Scripting and automation have moved from bonus skills to baseline expectations.
This guide maps out every skill category the role requires in 2026, from foundational technical knowledge to the cloud, security, and automation competencies modern IT environments now demand.
TL;DR
- System administrator skills now span on-premises, hybrid, and cloud-native environments, and the role requires competency across all three in most modern organisations.
- Core technical domains include OS administration, networking, server management, cloud platforms, security, scripting, and monitoring.
- Soft skills—particularly documentation, communication, and structured problem-solving—directly affect how effectively technical work translates into operational outcomes.
- Skill requirements differ significantly by environment type; SMB roles reward breadth, while enterprise roles reward depth in specific domains.
- The highest-demand skills in 2026 are concentrated in cloud administration, IAM, security hardening, Infrastructure as Code, AI-assisted operations, and automation.
What Is the Role of a System Administrator?
A system administrator is responsible for building, maintaining, and securing the technology infrastructure an organisation runs. That includes servers, operating systems, networks, user accounts, storage systems, and the software that ties all of it together. When any part of that infrastructure fails, the system administrator diagnoses it, fixes it, and puts measures in place to prevent recurrence.
The role sits at the operational centre of IT. System administrators aren’t designing enterprise architecture or writing application code, but they keep the environment stable enough for everyone else to do their jobs. Developers need reliable infrastructure to deploy to. Finance needs secure system access. Leadership needs uptime. The system administrator is accountable for all of it.
Day-to-day responsibilities typically include:
System installation and configuration: Setting up servers, operating systems, and software to meet performance, security, and compliance requirements.
User and access management: Creating accounts, assigning permissions, and deprovisioning credentials when employees leave.
Monitoring and patch management: Tracking system health and keeping operating systems and software current.
Backup and recovery: Maintaining backup systems and testing restoration procedures regularly.
Security enforcement: Managing firewalls, endpoint controls, access policies, and audit logging.
Troubleshooting: Diagnosing and resolving hardware, software, and network issues.
In a small organisation, one system administrator handles all of the above. In a large enterprise, the work is divided across specialised roles: network administrators, security engineers, cloud platform teams, and identity management specialists. The system administrator title is often the foundation from which those specialisations grow.
Why System Administrator Skills Matter in Modern IT Environments
The environments system administrators manage today are significantly more complex than they were five years ago. A skill set built entirely around on-premises infrastructure creates real gaps when the organisation runs workloads across AWS, Azure, and a legacy data centre simultaneously.
Three pressures are driving this:
Infrastructure has stopped living in one place. Hybrid environments are now the default. System administrators need fluency across on-premises systems and cloud platforms simultaneously, understanding where data lives, how systems communicate across boundaries, and where access controls apply.
Security ownership has shifted to the infrastructure layer. Unpatched systems, misconfigured servers, and overprivileged accounts are among the most exploited entry points in breach incidents. System administrators have direct control over all three. Security is part of the job, not adjacent to it.
The volume of work has outgrown manual processes. Modern IT environments generate provisioning requests, patch cycles, and monitoring events at a scale that manual administration handles poorly. System administrators who can automate repetitive workflows absorb that volume without proportionally increasing headcount or error rates.
Gaps in cloud knowledge slow migrations. Gaps in security leave vulnerabilities open. Gaps in automation create bottlenecks that affect every team that depends on the IT infrastructure to function.
Core Technical System Administrator Skills
Technical depth is what separates a system administrator who keeps infrastructure stable from one who can design, secure, and scale it.
Operating Systems Administration
Most enterprise environments run Windows Server and Linux. On Windows, that means Active Directory, Group Policy, DNS, DHCP, and PowerShell. On Linux, it means command-line proficiency, package management across RHEL, Ubuntu, and AlmaLinux or Rocky Linux, and service management via systemd. OS administration also includes patch cycles, performance troubleshooting, and hardening against baselines like CIS Benchmarks.
Networking Fundamentals
System administrators need enough networking knowledge to diagnose problems without escalating every connectivity issue. The foundation covers TCP/IP, subnetting, DNS, DHCP, and routing basics, extending to firewall rules, VPN configuration, VLAN segmentation, and diagnostic tools like Wireshark and traceroute.
Server and Infrastructure Management
Physical infrastructure work includes hardware provisioning, BIOS and firmware management, RAID configuration, and out-of-band management via Dell iDRAC or HP iLO. Virtualisation is central to most environments; system administrators should be comfortable provisioning VMs, managing resource allocation, configuring high availability, and performing live migrations on VMware vSphere or Hyper-V.
Cloud Administration Skills
Cloud administration is a baseline expectation. System administrators need practical experience with at least one major platform—AWS, Azure, or Google Cloud—covering IAM configuration, compute and storage provisioning, cloud networking, and cost monitoring. Infrastructure as Code tools like Terraform and CloudFormation are increasingly expected alongside core platform skills.
Security and Access Control
User permissions, firewall rules, patch schedules, and service configurations directly affect how exposed an organisation is to compromise. Access control means enforcing least-privilege consistently through regular access reviews, RBAC structures, MFA enforcement, and privileged access management. System administrators are also responsible for patch management, configuration audits, endpoint protection, and audit logging.
Scripting and Automation
PowerShell and Bash cover the majority of automation needs across Windows and Linux, respectively. Python adds versatility for complex workflows and API interactions in cloud environments. Ansible extends automation across multiple systems without requiring agents. Tasks that previously took hours run in minutes with consistent results.
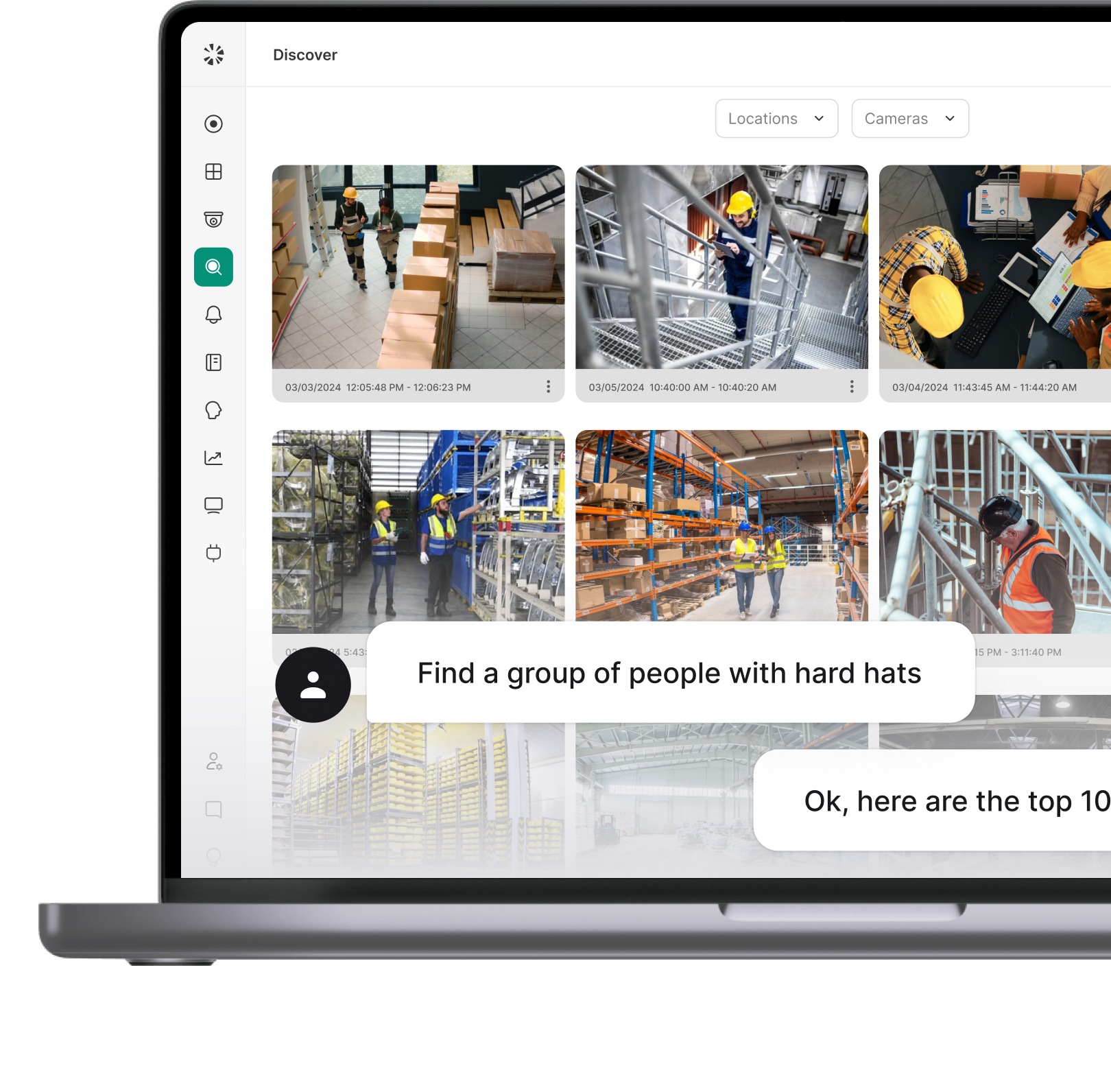
AI-Assisted Administration
AI copilots and large language models are reshaping day-to-day administration workflows. In 2026, system administrators increasingly use AI-assisted tools for script generation, log analysis, anomaly detection, and incident triage. Familiarity with AI-driven monitoring platforms and the ability to evaluate AI-generated outputs critically—rather than accepting them blindly—is becoming a practical differentiator.
Monitoring and Troubleshooting
Effective troubleshooting means isolating the actual cause, not applying fixes until something works. System administrators should be comfortable with monitoring tools like Nagios, Zabbix, Prometheus, or Datadog, and log management platforms like the ELK Stack or Splunk. Alert tuning matters as much as tool selection; a monitoring setup that generates constant noise gets ignored.
Essential Soft Skills for System Administrators
Technical skills get a system administrator hired. Soft skills determine how effective they are once they’re in the role.
Problem-Solving
Effective troubleshooting follows a structured process: define the problem precisely, identify what changed recently, form a hypothesis, test it, and document the outcome. Administrators who skip documentation end up solving the same problems repeatedly. Root cause analysis takes this further, tracing the problem to its origin rather than closing a ticket when symptoms disappear.
Communication with Technical and Non-Technical Teams
System administrators need two communication modes that switch fluidly. With technical peers, precision matters; articulating what was observed, tested, and ruled out makes cross-team troubleshooting faster. With non-technical stakeholders, the requirement flips. A finance director dealing with an outage needs to know what is affected, what is being done, and when to expect resolution—not the technical cause.
Documentation and Process Discipline
When the only person who knows how a system is configured is the one who built it, every resignation becomes a potential incident. Useful documentation covers system configurations, runbooks for routine tasks, incident records, and infrastructure diagrams that reflect the current environment. Documentation written once and never updated is only marginally better than none.
Time Management and Prioritisation
Prioritisation should be grounded in business impact rather than ticket sequence. A locked-out user affects one person; an authentication service outage affects everyone. Longer-term work—upgrades, automation, and documentation—needs protected time. System administrators who never carve it out stay permanently reactive.
Adaptability and Continuous Learning
The technology stack in use today will look different in three years. Certifications from Microsoft, AWS, Red Hat, and CompTIA provide structured learning frameworks. Hands-on practice in lab environments or cloud free-tier accounts builds applied familiarity that study alone does not.
System Administrator Roles and Responsibilities
The system administrator role owns the IT infrastructure’s operational layer. While developers build applications and security teams define policy, system administrators are responsible for keeping the underlying environment stable, accessible, and secure on a daily basis.
Infrastructure Deployment and Configuration
System administrators provision servers, install and configure operating systems, deploy applications, and integrate new systems into the existing environment. The decisions made at this stage—security settings, access controls, and network placement—carry long-term consequences. Misconfigured systems at deployment are significantly harder to correct once they are running in production.
User and Access Management
This is one of the most operationally continuous responsibilities in the role. Key tasks include creating and maintaining user accounts across systems and directories, assigning permissions based on role and business need, enforcing access policies and MFA requirements, and deprovisioning credentials promptly when employees leave or change roles. In most environments, this work connects directly to Active Directory, Microsoft Entra ID, or a cloud identity provider like Okta.
Monitoring, Patching, and System Health
Security Administration
Security at the infrastructure level is a direct system administrator responsibility. That means enforcing firewall rules, managing endpoint protection, maintaining audit logs, and applying security baselines across every system under administration. Where a dedicated security team exists, system administrators implement the policy that team defines. Where one does not, they own the full scope.
Backup, Recovery, and Vendor Management
Backup and disaster recovery require configuring backup jobs, validating completion, and testing restoration procedures regularly. A backup process that has never been tested is not a reliable one.
Vendor and asset management covers software licensing, hardware inventories, and support contracts. Accurate records directly affect security audits and budget planning, and they degrade quickly without active maintenance.
How System Administrator Skills Shift Across Environment Types
System administrator skills do not apply uniformly across every organisation. The environment type determines which competencies get used daily and which gaps create the most operational risk.
On-Premises IT Environments
On-premises environments demand the deepest hardware and infrastructure knowledge, with no shared responsibility model to fall back on. Core skills include Windows Server and Linux administration, Active Directory and Group Policy, VMware vSphere or Hyper-V, physical hardware management via iDRAC or iLO, and on-site backup and recovery. Security is fully internally managed across patching, firewall configuration, and endpoint protection.
Hybrid IT Environments
Hybrid environments are the most technically demanding. System administrators must be fluent in both on-premises infrastructure and cloud platforms simultaneously. Managing identity across that boundary—synchronising Active Directory with Microsoft Entra ID, configuring conditional access policies, and maintaining SSO—becomes a core daily responsibility. Site-to-site VPNs, ExpressRoute connections, and firewall rules spanning both environments add further complexity that purely on-premises or cloud administrators do not face.
Cloud-Native IT Environments
Hardware knowledge becomes largely irrelevant here. Security, access control, and monitoring principles apply just as directly as in any other environment.
Enterprise Environments
Scale and organisational complexity define enterprise system administration. Responsibilities are divided across specialised teams, and system administrators operate within structured change management processes, formal documentation requirements, and compliance frameworks like SOC 2 or ISO 27001. The differentiating skills are depth in specific domains and the ability to collaborate effectively across teams.
SMB Environments
In SMB environments, one system administrator often owns everything: servers, networking, cloud accounts, user management, security, backups, and end-user support. Breadth matters more than depth at this scale. Solid coverage across Active Directory, Microsoft 365, basic networking, cloud fundamentals, and scripting handles the majority of what the role demands day to day.
Most In-Demand System Administrator Skills in 2026
The skills commanding the most attention from hiring managers in 2026 reflect where IT environments have moved over the past few years. Cloud, security, and automation now appear in the majority of system administrator job postings, while purely on-premises skill sets have become a secondary requirement rather than a primary one.
The highest-demand areas currently are:
- Cloud platform administration: AWS and Azure experience appear in the majority of mid-size and enterprise system administrator roles. Multi-cloud awareness is increasingly expected, even when the organisation primarily uses one platform.
- Identity and access management: With zero trust architectures gaining adoption, IAM skills covering both on-premises directory services and cloud identity providers are consistently listed as required rather than preferred.
- Security hardening and compliance: System administrators who can configure systems against CIS Benchmarks, maintain audit trails, and support compliance frameworks like SOC 2 or ISO 27001 are in higher demand as regulatory requirements tighten across industries.
- Infrastructure as Code: Terraform and Ansible experience has moved from a differentiator to a baseline expectation in cloud-heavy environments.
- Scripting and automation: PowerShell and Python remain the most requested languages, with Bash close behind for Linux-heavy environments.
- AI-assisted operations: Familiarity with AI-driven monitoring, copilot-assisted scripting, and intelligent alerting is an emerging differentiator.
- Container and Kubernetes management: Demand is growing in organisations that have moved workloads into containerised environments, though this remains more specialised than the skills above.
Purely reactive, ticket-driven system administrators without cloud or automation depth are increasingly competing for a narrower range of roles.
How to Build System Administrator Skills
The most effective approach combines structured learning with hands-on practice, since technical skills that have not been applied in a real environment do not transfer reliably under pressure.
Start with a lab environment. A home lab, cloud free-tier accounts, or a local virtualisation setup using VirtualBox or VMware Workstation gives system administrators a space to break things safely. Provisioning virtual machines, configuring Active Directory, and practising scripting in a controlled environment builds applied familiarity that no course alone provides.
Use certifications as a learning framework. CompTIA Network+ and Security+ cover foundational knowledge. Microsoft AZ-104, AWS SysOps Administrator, and Red Hat RHCSA map directly to the competencies most in demand. The structured curriculum is as valuable as the credential itself.
Learn scripting by solving real problems. Writing scripts to automate tasks already being done manually is more effective than working through tutorials in isolation. Starting with PowerShell or Bash to automate a repetitive daily task builds both skill and a practical reference library simultaneously.
Build incrementally. Prioritise OS administration, networking fundamentals, and Active Directory before moving into cloud and automation. Trying to cover everything at once produces surface-level familiarity without depth in any area.
System Administrator Skills Checklist
Use this as a self-assessment reference or a baseline for evaluating candidates. Skills are grouped by domain, not by priority, since the weight of each area depends on the environment.
Operating Systems
- Windows Server administration and Active Directory management
- Linux administration across at least one major distribution (RHEL, Ubuntu, AlmaLinux or Rocky Linux)
- Group Policy configuration and DNS/DHCP management
- OS hardening against CIS Benchmarks or equivalent security baselines
- Patch management and CVE tracking
Networking
- TCP/IP, subnetting, DNS, and DHCP fundamentals
- Firewall rule configuration and access control lists
- VPN setup and troubleshooting
- VLAN configuration and network segmentation
- Packet analysis using Wireshark or equivalent tools
Server and Infrastructure
- Physical server provisioning and hardware management
- VMware vSphere or Microsoft Hyper-V administration
- High availability and failover clustering configuration
- Storage management across SAN, NAS, or local storage
- Backup configuration and documented recovery testing
Cloud Administration
- Compute and storage provisioning on AWS, Azure, or Google Cloud
- IAM roles, policies, and service account configuration
- Cloud networking, including VPCs, security groups, and load balancers
- Infrastructure as Code using Terraform or CloudFormation
- Cost monitoring and resource optimisation
Security and Access Control
- Least-privilege access enforcement and regular access reviews
- Role-based access control (RBAC) configuration
- MFA enforcement across systems and privileged accounts
- Audit log maintenance and monitoring
- Familiarity with NIST, CIS Controls, or ISO 27001 frameworks
Scripting and Automation
- PowerShell scripting for Windows and Microsoft cloud environments
- Bash scripting for Linux administration tasks
- Python for API interactions and complex workflow automation
- Configuration management using Ansible, Puppet, or Chef
Monitoring and Troubleshooting
- Infrastructure monitoring using Nagios, Zabbix, Prometheus, or Datadog
- Log management and analysis via ELK Stack or Splunk
- Structured troubleshooting methodology with documented outcomes
- Alert threshold configuration and notification routing
Soft Skills
- Structured problem-solving and root cause analysis
- Clear communication with both technical and non-technical stakeholders
- Consistent documentation of configurations, procedures, and incidents
- Prioritisation based on business impact
- Continuous learning through certifications and hands-on practice
System Administrator Skills for Resume and Career Growth
A system administrator’s resume needs to show scope and impact. “Managed Active Directory” tells a hiring manager very little. “Managed Active Directory for 1,200 users across three sites, including automated provisioning and quarterly access reviews” communicates scale, method, and discipline. Attach numbers wherever possible: user counts, system counts, uptime percentages, or time saved through automation.
Use exact terminology from job postings. Applicant tracking systems filter resumes before a human reviews them. “Microsoft Entra ID” rather than “cloud identity,” “Terraform” rather than “infrastructure automation,” improves the chances of passing that filter.
Group technical skills by category—Operating Systems, Cloud Platforms, Scripting, Security—rather than listing them flat. It makes a resume easier to scan and signals structured thinking.
For career growth, the path typically branches based on where depth has developed:
Choose a direction first, then identify certifications that map to it. Collecting credentials without a clear trajectory is a slow path to anywhere.
What Good System Administration Actually Looks Like
The skill set this guide covers is broad by design, because the role demands it. System administrators who invest in depth across technical domains—cloud, security, automation, and infrastructure—while building the soft skills that make that technical work operationally useful, are the ones who stay relevant as environments evolve and move into more specialised or senior roles.
The checklist in this guide is a practical starting point for identifying gaps. The career path table points toward where closing those gaps can lead. The work in between is incremental—one certification, one lab environment, one automated workflow at a time.
Modern IT environments do not stay static, and neither does the system administrator role. The professionals who treat skill development as continuous rather than episodic are the ones who consistently have options, whether that means a broader scope in their current role, a move into cloud engineering or security, or a path toward IT leadership.
FAQ
Operating system administration, networking fundamentals, security and access control, and scripting are the foundation. Cloud administration and Infrastructure as Code have become equally critical in most modern environments.
A system administrator is responsible for deploying, configuring, maintaining, and securing the IT infrastructure that an organization runs. That includes servers, operating systems, networks, user accounts, and the software that connects them.
Core responsibilities include user and access management, patch management, system monitoring, backup and recovery, security administration, and troubleshooting infrastructure issues. The exact scope varies by organization size and environment type.
Yes, particularly skills that extend beyond on-premises infrastructure. Cloud administration, automation, IAM, and security hardening are consistently listed as required competencies in current job postings across mid-size and enterprise organizations.
Compute and storage provisioning on AWS, Azure, or Google Cloud, IAM configuration, cloud networking, cost management, and Infrastructure as Code tools like Terraform. Scripting in Python or PowerShell is also expected in most cloud-focused roles.
System administrators manage servers, operating systems, user accounts, and software infrastructure. Network administrators focus specifically on routers, switches, firewalls, and network connectivity. In smaller organizations, one person often covers both. In larger environments, the roles are separate with clear boundaries.