The front desk has become a critical security control point. Organizations today deal with a more complex, higher-volume visitor mix than ever before: contractors, vendors, clients, delivery personnel, job candidates, and guests all moving through the same facility, often with different access needs and different risk profiles.
The risks are real. Unauthorized access, tailgating, and compliance gaps are increasingly common in facilities still relying on paper logbooks and informal check-in processes:
- Contractors and vendors with varying access needs
- Clients and job candidates expecting a professional experience
- Delivery personnel cycling in and out multiple times a day
- Guests who need escorting but rarely get it
Manual logs can't produce a reliable audit trail. They can't tell you who's still on-site during an emergency. And they make compliance audits painful.
Paper sign-in sheets had their time. That time is over.
This guide breaks down the visitor management strategies that work in 2026, from pre-registration and credentialing to zone-based access, real-time monitoring, and emergency accountability, so you can identify the gaps in your current approach and fix them.
TL;DR
- A visitor management system controls, tracks, and documents who enters your facility, where they go, and when they leave
- Pre-registration, identity verification, and access control integration are the foundation of an effective strategy
- Paper logs and standalone apps create visibility gaps that only surface when something goes wrong
- Real-time monitoring is what separates administrative record-keeping from operational security
- Coram unifies visitor check-in, access control, video, and emergency management in one connected platform
What is Visitor Management?
Visitor management is the process of tracking, recording, and controlling who enters a facility — guests, vendors, contractors, and clients — to maintain security, safety, and compliance.
Three questions should have a clear answer at any point in the day:
- Who is on-site right now?
- Why are they here?
- Are they authorized to be where they are?
Modern visitor management replaces paper logs with digital systems that handle check-ins, identity verification, badge printing, host notifications, and emergency evacuation lists. It screens visitors against watchlists, captures signatures for NDAs or safety documents, and manages access to specific zones.
The result is accurate, searchable records that hold up during audits and incidents, not a clipboard that gets misplaced on a busy Monday morning.
Why is Visitor Management a Growing Security Priority?
Visitor-related security failures rarely look dramatic. They look like a contractor who stayed on-site two hours after their job ended. A vendor who was escorted to a meeting room and then wandered into a restricted area. A former employee who walked in behind a delivery driver without anyone noticing.
Three pressures are making these gaps harder to ignore.
Physical Security Risks Are Getting Harder to Dismiss
Tailgating is one of the most common physical security vulnerabilities and one of the hardest to catch without the right systems in place. When there's no log of who entered, when, and through which door, investigating an incident becomes guesswork.
Imagine a fire alarm triggers at 2 PM on a Tuesday. You have 14 visitors checked in across three floors. Can you account for all of them in under 60 seconds? Without real-time visitor data, the answer is almost always no.
Unauthorized access doesn't always mean theft. Sometimes it's a compliance violation, a safety incident, or a data exposure tied to someone who should never have passed the front desk.
Compliance Requires Records You Can Actually Produce
Auditors no longer accept incomplete paper logs. Regulated industries need time-stamped, searchable visitor records:
- Healthcare facilities must meet HIPAA physical safeguard requirements
- Schools have legal obligations around campus access and child safety
- Financial institutions and government contractors need documented logs for access reviews
Digital records with accurate timestamps and complete entries are now the baseline expectation, not a nice-to-have.
More Visitors, More Variables, More Risk
Hybrid work and outsourced services have changed who shows up at a facility on any given day. A job candidate needs to be escorted. A contractor needs recurring access for three weeks. A vendor needs the loading dock and nothing else.
One sign-in sheet handles none of these situations well. Each visitor type carries a different access requirement and a different level of risk. Managing them all the same way is where visibility breaks down.
Types of Visitors Organizations Need to Manage
Not every visitor carries the same risk or requires the same process. Managing a job candidate the same way you manage a contractor with recurring facility access is where visibility breaks down.
Contractors and Trade Workers
A contractor arrives for a week-long electrical job. Before they reach the front door, their identity should be verified, their approved work zones defined, and their access credentials ready. When the job ends, their access should expire automatically. Without a system tracking this, it's easy for access to outlast the job.
Vendors and Suppliers
Vendors often have established relationships with organizations, which creates a false sense of security. A vendor visiting for a quarterly review needs a meeting room, not a server room. Their check-in process should reflect that distinction.
Clients and Business Guests
A slow, paper-based check-in signals operational inefficiency before a meeting even starts. Digital pre-registration and a smooth kiosk check-in set the right tone while still maintaining a documented record of the visit.
Delivery Personnel
Delivery staff cycle in and out multiple times a day, often through service entrances. They're frequently the most under-tracked visitor type, leaving organizations with no reliable record of who entered, when, and through which access point.
Job Candidates
Candidates are typically escorted, but that doesn't mean they should go unlogged. A documented check-in ensures the right host is notified on arrival and maintains consistency across all visitor types.
Each visitor type carries a different access requirement, a different verification need, and a different level of risk. A single sign-in sheet treats all of them identically. That's not a process. That's a gap.
Core Visitor Management Strategies Used by Organizations
Most front-desk security gaps don't come from a lack of effort. They come from a lack of process. These five strategies give organizations a clear framework for managing visitors from arrival to departure.
Pre-Registration and Visitor Pre-Approval
The check-in process should start before a visitor reaches the front door.
Pre-registration allows hosts to submit visitor details in advance: name, company, purpose of visit, and expected arrival time. The front desk already knows who to expect, what access they need, and how long they're staying. When the visitor arrives, check-in takes seconds instead of minutes.
Think of a vendor arriving for a scheduled equipment installation. With pre-registration, their badge is ready, their approved zones are configured, and the host is automatically notified the moment they check in. Without it, that same arrival creates a bottleneck at the front desk and a gap in the access record.
Pre-approval also adds a layer of accountability. If a visitor wasn't pre-registered, that's a signal worth acting on, not something to wave through because the lobby is busy.
Identity Verification at Check-In
Knowing someone's name is not the same as knowing who they are.
Identity verification at check-in can include:
- Government-issued ID scanning
- Photo capture for visual confirmation
- Cross-checking against watchlists or previously flagged visitors
- Host confirmation before access is granted
The right level of verification depends on the facility. A corporate office may only need ID scanning. A school or healthcare facility may require all of the above. The point is to have a consistent, documented process rather than relying on front desk staff to make judgment calls under pressure.
Digital Visitor Badging
A printed badge does more than identify a visitor. It signals to everyone in the building that this person has been verified, where they're allowed to go, and when their visit expires.
Effective digital badging systems:
- Generate badges automatically after check-in
- Display the visitor's name, photo, host, and access zone
- Include a time or date expiration to prevent reuse
- Make it visually obvious when a badge is no longer valid
Without badges, staff have no reliable way to identify who belongs in a space and who doesn't.
Access Control Integration
A visitor check-in that isn't connected to your access control system creates an immediate gap. Someone can sign in at the front desk and still reach areas they were never approved for.
Integrating visitor management with access control means:
- Temporary credentials are issued automatically based on the visitor's approved zones
- Access is time-limited and expires when the visit ends
- Doors to restricted areas stay closed to visitors without explicit authorization
This removes the dependency on staff escorts and manual door monitoring, both of which break down quickly in busy facilities.
Real-Time Visitor Monitoring
Knowing who checked in is only half the picture. Knowing where they are right now is what makes visitor management operational rather than just administrative.
Real-time monitoring gives security and front desk teams a live view of who is on-site, which areas they've accessed, and how long they've been in the building. During an emergency, this becomes critical.
During a fire drill, can you account for every visitor on-site in under 60 seconds? With real-time monitoring, yes. Without it, you're working from a paper log that may already be an hour out of date.
Real-time visibility also flags unusual behavior: a visitor in a zone they weren't approved for, a badge used after expiration, or a check-in that never resulted in a check-out.
Why Paper Logs and Standalone Systems Fall Short
Paper logs and disconnected visitor systems can't meet modern operational, compliance, or safety standards. The gaps they create fall into five clear categories.
1. Human Error Is Built Into the Process
Handwritten entries are frequently incomplete, inaccurate, or illegible. There's no validation, no alert when a field is skipped, and no way to prevent intentional manipulation. A busy Monday morning is all it takes for the log to become unreliable.
2. No Real-Time Visibility
Information on a paper log is confined to a single clipboard. No one else can access it, no one is monitoring it, and by the time a security issue surfaces, the data is hours old and missing context.
3. Operational Costs That Add Up Quietly
Staff spend time writing, collecting, and correcting manual entries. Retrieving historical records means physically searching through archives. Updating a paper form across multiple locations is a project in itself.
4. Compliance Becomes a Liability
Paper-based systems frequently fail audits because records are missing, inconsistent, or improperly stored. Without automatically time-stamped entries, proving compliance with regulations like HIPAA is difficult to defend.
5. Standalone Apps Only Go So Far
A visitor management app that doesn't connect to access control or video surveillance still operates in a silo. It records who checked in. It has no visibility into where that visitor went, what doors they accessed, or whether they ever left.
The check-in log shows a clean entry. The security reality can tell a completely different story.
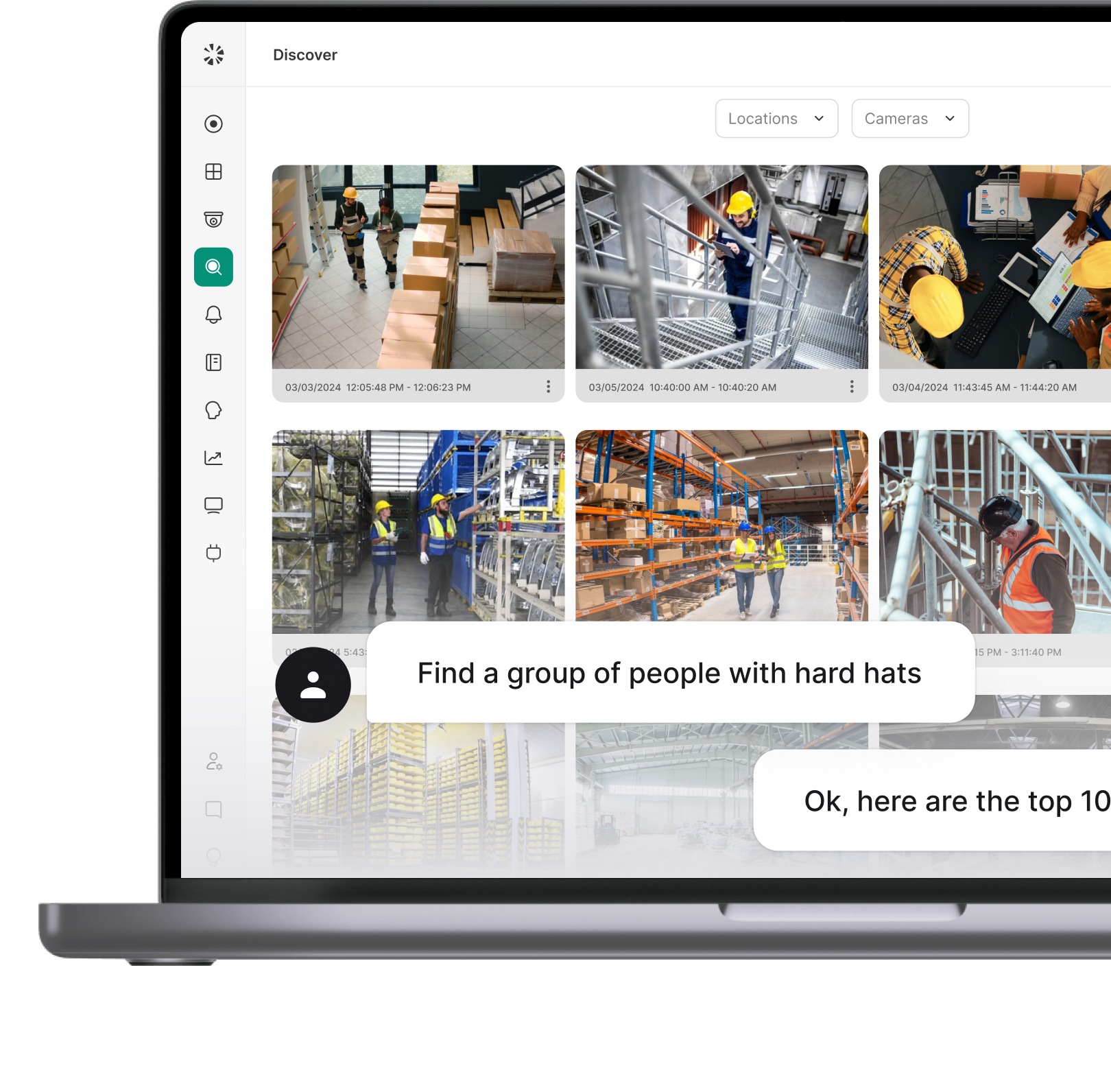
How Coram Brings Visitor Management Into a Unified Security Platform
Most organizations manage visitor security across multiple disconnected tools: a visitor app here, an access control system there, cameras on a separate platform. Each system works in isolation. None of them talk to each other.
Coram takes a different approach. Visitor Management is built directly into the Coram platform, alongside video surveillance, access control, and emergency management. There's no integration to configure, no separate vendor to manage, and no data sitting in a silo.
Coram Visitor Management also works as a standalone product for organizations that need immediate visibility into who is on-site, without committing to a full platform switch. For teams already using Coram for video and access control, it connects directly into existing security workflows, making every tool in the suite more effective.
One Platform, One View
When a visitor checks in through the iPad kiosk, their entry appears instantly in the Visitor Log inside the Coram web app. The same dashboard where your team monitors camera feeds, door access events, and security alerts now shows exactly who is on-site and when they arrived.
Security teams don't need to switch between systems to connect the dots.
How Check-In Actually Works
Coram's visitor check-in runs on an iPad using the Coram Visitor app. Setup is straightforward:
- Open the Visitor app and register the device using a one-time code
- Assign the device to a specific location in the Coram web app
- The iPad functions as a secure check-in kiosk from that point forward
Optional photo capture and driver's license scanning add identity verification at the point of entry. If the iPad temporarily loses internet connectivity, check-ins continue offline and sync automatically to the cloud once the connection is restored, preserving original timestamps.
Built for Real Operational Environments
Coram Visitor Management is designed for facilities where visitor volume, complexity, and security requirements are high:
- K-12 schools and districts
- Healthcare facilities
- Corporate offices
- Manufacturing and warehouse sites
- Multi-location enterprises
Role-based permissions mean admins and guard-level users see what's relevant to their function, without overcomplicating the interface for front desk staff.
What's Already Connected
Because Visitor Management lives inside the same platform as Coram's other security tools, visitor activity is automatically visible alongside live and recorded video footage, door-level access control events, person detection and Journey Path tracking, and emergency management and reunification workflows.
During an emergency, this matters significantly. Instead of pulling visitor records from one system and cross-referencing camera footage from another, everything is in one place. Accounting for every visitor on-site becomes a task that takes seconds, not minutes.
What's Coming Next
Coram continues to expand Visitor Management capabilities. Planned additions include visitor blacklists, badge printing, expanded license verification workflows, and deeper access control integration, giving organizations more control over who enters and what happens when they do.
Start Knowing Who's in Your Building
Visitor management is only as strong as the systems behind it. Pre-registration, identity verification, digital badging, access control integration, and real-time monitoring all matter. But they only deliver full security value when they operate as a connected system.
Here's what that looks like in practice:
- Every visitor is pre-registered before they arrive
- Identity is verified at check-in, not assumed
- Badges communicate access zones and expiration visually
- Access control enforces zone restrictions automatically
- Real-time monitoring accounts for every visitor during an emergency
Coram makes that possible by bringing visitor check-in, access control, video surveillance, and emergency management into one platform. There's no need to switch between systems. That means no gaps in visibility and no guesswork during an incident.
FAQ
A visitor management strategy is the set of processes an organization uses to control, track, and document who enters its facilities. It covers everything from pre-registration and identity verification at check-in to zone-based access, real-time monitoring, and emergency accountability. A strong strategy ensures every visitor is known, authorized, and accounted for from arrival to departure.
Visitor management directly affects physical security, compliance, and operational efficiency. Without a structured process, organizations face risks like unauthorized access to restricted areas, tailgating, incomplete audit trails, and no reliable way to account for everyone on-site during an emergency. For regulated industries like healthcare, education, and finance, the compliance stakes are even higher.
When visitor management connects to access control, temporary credentials are issued automatically based on the visitor's approved zones. Access is time-limited and expires when the visit ends.
Restricted doors stay closed to visitors without explicit authorization. This removes the dependency on staff escorts and manual door monitoring and creates a complete record of where every visitor went inside the facility.
Paper sign-in sheets only capture a moment at the front desk. They don't verify identity, control access, or track where a visitor goes after check-in.
Entries are frequently incomplete, illegible, or missing entirely during busy periods. They fail compliance audits because records lack timestamps and searchability. And during an emergency, there's no reliable way to know who is still on-site based on a paper log alone.