Something breaks. Systems slow down. Alerts start firing. Messages pile up.
And suddenly, everyone is trying to fix the problem at the same time.
This is what most incidents look like today.
With the rise of cloud environments, AI workloads, and always-on infrastructure, outages and failures aren't rare anymore. But what turns a small issue into a major disruption isn't just the problem; it's the response.
When teams lack clarity, work gets duplicated, critical steps get missed, and communication breaks down.
That's why having a defined incident response team is no longer optional.
A strong incident response team brings structure to chaos. It ensures the right people handle the right tasks, at the right time, with clear ownership and coordination.
In this guide, we'll break down what an incident response team is, its key roles and responsibilities, and how to build one that actually works when it matters most.
What is an Incident Response Team?
An incident response team is a dedicated group of specialists responsible for managing and resolving incidents that disrupt operations, including cybersecurity breaches, physical security threats, and infrastructure failures.
Their role is simple in principle but critical in execution: detect issues early, contain them quickly, and restore normal operations with minimal impact.
In today's environments, incidents don't stay confined to one domain. A security breach could involve digital systems, physical access points, and operational workflows at the same time.
That's why a modern incident response team is not just made up of security analysts; it often includes IT engineers, operations teams, communication leads, and sometimes legal or compliance stakeholders.
Why Every Organisation Needs an Incident Response Team
Incidents are no longer rare or isolated. They cut across systems, teams, and even physical environments, and they escalate faster than most organizations expect. What makes the difference isn't prevention alone, but how effectively you respond. A well-structured incident response team brings that capability into focus.
Faster Response, Better Outcomes
When something goes wrong, time is everything. Without a defined incident response team, teams often react in parallel, duplicating efforts or missing critical actions. With clear ownership and coordination, response becomes immediate and focused, helping contain issues before they spread across systems or locations.
Reduced Financial and Operational Impact
Every minute of downtime has a cost: lost productivity, disrupted operations, and potential revenue impact. A strong incident response team minimizes this by acting early, reducing the scale of disruption, and accelerating recovery. The difference between a few minutes of response and a few hours can be significant.
Cross-Functional Coordination
Incidents rarely stay within one domain. A security issue may involve IT, operations, facilities, and leadership at the same time. An incident response team ensures all stakeholders are aligned, communication is clear, and decisions are made quickly without confusion or delays.
Stronger Compliance and Accountability
As regulatory expectations increase, organizations are required to respond to incidents in specific ways and within defined timelines. A structured team ensures proper documentation, timely reporting, and compliance with requirements, reducing legal and reputational risks.
Builds Trust and Business Confidence
Customers and partners don't expect incidents to never happen, but they do expect them to be handled responsibly. A coordinated and transparent response demonstrates control, reliability, and accountability, which helps maintain trust even during disruptions.
Continuous Learning and Improvement
Every incident provides insights. A mature incident response team doesn't just resolve issues; it reviews them, identifies gaps, and improves processes. Over time, this leads to faster detection, better coordination, and stronger overall resilience.
Preparedness for Modern Infrastructure Complexity
With cloud systems, distributed teams, and always-on operations, infrastructure today is more complex than ever. An incident response team ensures your organization is not just reacting to this complexity but is prepared to manage it effectively.
Core Roles and Responsibilities on an Incident Response Team
An effective incident response team doesn't just react when something breaks; it follows a structured lifecycle that ensures incidents are handled with clarity, speed, and consistency. These responsibilities are not isolated tasks but coordinated phases, where each role contributes to minimizing impact and restoring operations efficiently.
Preparation
Preparation is where a strong incident response team is truly built, long before any incident occurs. This phase goes beyond documentation. It involves:
- Creating a clear, actionable incident response plan with defined workflows
- Establishing incident response team roles and responsibilities so there's no confusion during high-pressure situations
- Identifying critical assets (systems, locations, data, people) and mapping potential risks
- Ensuring alignment with compliance, legal, and internal governance requirements
Mature teams also invest heavily in readiness. This includes running simulations, tabletop exercises, and real-world drills to test response scenarios, whether cyber incidents, physical breaches, system outages, or combined events.
Preparation also means setting up the right tools for monitoring, alerting, and communication. Without this foundation, even the best teams struggle to act effectively.
When done right, preparation ensures that when an incident happens, the response is structured, predictable, and fast, rather than reactive or improvised.
Detection and Triage
This is where speed meets intelligence. The incident response team continuously monitors systems, both digital and physical, for anomalies. These could include unusual login attempts, unexpected system behavior, unauthorized access, or suspicious activity captured through surveillance systems. Once something is flagged, the team moves into triage:
- Is this a real incident or a false alarm?
- What is the severity and potential impact?
- Which systems, locations, or assets are affected?
This phase often relies on a mix of automated tools, threat intelligence, and human judgment. The goal is not just detection but prioritization, ensuring that critical threats are addressed first.
Containment and Mitigation
Once an incident is confirmed, the immediate focus is on control: stopping the situation from getting worse. Containment strategies depend on the nature of the incident, but may include:
- Isolating affected systems or networks
- Disabling compromised accounts or credentials
- Restricting access to specific locations or systems
- Blocking malicious traffic or suspicious activity
The challenge here is balance. The incident response team must contain the threat without disrupting business operations unnecessarily.
Mitigation follows containment and focuses on stabilizing the environment. This could involve:
- Applying temporary fixes or patches
- Redirecting workflows to backup systems
- Increasing monitoring around affected areas
This phase requires strong coordination across IT, operations, and security teams. Quick, informed decisions are critical to reduce impact while maintaining continuity.
Eradication and Recovery
After the situation is under control, the focus shifts to removal and restoration. Eradication involves identifying and eliminating the root cause:
- Removing malware or unauthorized access
- Fixing vulnerabilities or misconfigurations
- Addressing process gaps that led to the incident
This step is critical; if the root cause isn't fully resolved, the incident can recur. Recovery then focuses on bringing systems and operations back to normal:
- Restoring data from backups
- Re-enabling systems and services
- Verifying system integrity and security before full rollout
A strong incident response team ensures recovery is methodical, not rushed. Systems are tested, monitored, and validated before returning to full operation.
Communication is equally important here; stakeholders need clear updates on progress, risks, and timelines.
Post-Incident Review
This is where long-term resilience is built. After resolution, the incident response team conducts a detailed "lessons learned" analysis to evaluate the entire response:
- What triggered the incident?
- How quickly was it detected and contained?
- Where were the delays, gaps, or miscommunications?
- Which actions worked well and which didn't?
This review is documented in a comprehensive report that includes timelines, decisions made, outcomes, and recommendations. This becomes a critical resource for future training and planning.
Beyond documentation, the team takes action:
- Update the incident response plan and playbooks
- Patch vulnerabilities and strengthen controls
- Refine alerting, monitoring, and escalation processes
- Improve communication workflows across teams
Many organizations also conduct cross-functional debrief sessions to ensure learnings are shared, not siloed.
Over time, this process transforms the incident response team from reactive to proactive. Each incident strengthens the organization's ability to respond faster, coordinate better, and reduce future risk.
How an Incident Response Team Works
An incident response team operates through a structured incident response plan that defines how incidents are identified, assessed, and resolved. When an incident is detected, the team is activated immediately, with each member stepping into a clearly defined role to ensure fast, coordinated action.
At its core, how an incident response team works comes down to structure and clarity. Instead of multiple people reacting independently, responsibilities are distributed so that every critical task is handled without overlap or delay.
How the Process Typically Unfolds
Activation and Role Alignment: As soon as an incident is detected, the team is activated. The Incident Commander takes charge, assigns priorities, and ensures everyone is aligned.
Assessment and Triage: Security Analysts and Technical Leads investigate the issue, determine severity, and identify affected systems, locations, or assets.
Coordinated Response: The team works in sync:
- Technical teams handle containment and recovery
- Forensics analyzes the root cause and evidence
- Legal ensures compliance and risk management
- Communications manages internal and external updates
Real-Time Collaboration: Continuous communication ensures that all stakeholders stay informed, that decisions are aligned, and that actions are adjusted as the situation evolves.
Use of Technology and Visibility: Monitoring tools, analytics, and alerts support faster detection and decision-making, especially critical in both cyber and physical security incident response scenarios.
Extended Team Support: Depending on the scale, roles like IT operations, PR, and risk management step in to support recovery and business continuity.
Best Practices for Building an Effective Incident Response Team
Building an effective incident response team isn't just about assembling skilled individuals; it's about creating a system that performs reliably under pressure. When incidents happen, there's no time to figure things out. The strength of your response depends on how well your team is structured, trained, and aligned in advance.
Start With Your Risk Reality, Not Assumptions
Every incident response team should be built around the risks it's meant to handle. Begin by identifying:
- Your most critical assets (data, infrastructure, physical locations, operations)
- The types of incidents most likely to occur (cyber threats, outages, physical breaches)
- The potential business impact of each scenario
This clarity helps define the size, structure, and focus of your incident response plan. A team designed for real risks will always perform better than one built on generic assumptions.
Secure Leadership Buy-In and Clear Authority
An incident response team cannot operate effectively without leadership support. During incidents, decisions need to be made quickly, sometimes with business-wide impact. Without executive backing:
- Response actions may get delayed
- Teams may hesitate to act decisively
- Budgets for tools and training may fall short
Leadership alignment ensures the team has both the authority and resources to respond confidently and without friction.
Design a Cross-Functional Team Structure
Incidents don't stay within one function, and neither should your team. A strong incident response team includes:
- Security analysts and technical responders
- IT or infrastructure engineers
- Operations or facility managers
- Communication leads
- Legal and compliance stakeholders
Depending on your scale, you may adopt internal teams for deep system familiarity, external experts for specialized incident handling, or hybrid models that combine both.
Clear incident response team roles and responsibilities ensure that each function contributes effectively without overlap or confusion.
Build a Strong Skills Foundation
Technical expertise is essential, but it's only part of the equation. An effective incident response team also needs:
- Analytical skills to interpret signals and detect real threats
- Problem-solving ability to act under uncertainty
- Communication skills to keep stakeholders aligned
- Composure under pressure when the stakes are high
In real-world incidents, decision-making speed and clarity often matter more than technical depth alone.
Invest in Tools That Provide Real Visibility
Your team's effectiveness is directly tied to what they can see. An incident response team needs:
- Real-time monitoring and alerting systems
- Tools to analyze logs, events, and anomalies
- Systems for tracking incidents and response progress
But the key is integration and visibility. In modern environments, especially those involving physical security incident response, teams need a unified view across systems, locations, and events. Without that, valuable time is lost switching between tools and piecing together context.
Establish Reliable Communication Channels
During incidents, communication often breaks before systems do. That's why every incident response team should have:
- Clearly defined escalation paths
- Pre-established communication protocols
- Backup (out-of-band) communication channels
If primary systems fail, the team should still be able to coordinate seamlessly. Everyone should know who to contact, how to share updates, and when to escalate decisions.
Make Training Continuous and Realistic
An incident response team is only as good as its last practice. Training should go beyond theory and include:
- Tabletop exercises simulating real incidents
- Live drills to test coordination and response time
- Cross-functional scenarios involving multiple teams
These exercises help uncover gaps in your incident response plan, improve team coordination, and build confidence in high-pressure situations.
Document Processes for Real-World Use
Documentation should not just exist; it should be usable under pressure. Your incident response team needs:
- Clear, step-by-step playbooks for common incident scenarios
- Defined escalation paths and decision trees
- Easy access to documentation during live incidents
The key is simplicity and accessibility. Overly complex documents often go unused when time is limited. Good documentation acts as a guide, reducing confusion and ensuring consistency, even when team members are under stress or incidents occur outside regular hours.
It also supports onboarding, helping new members quickly understand workflows and responsibilities without slowing down the team.
Design for Scalability and Changing Environments
Your infrastructure today will not look the same a year from now. An effective incident response team must be built to scale:
- As you add more systems, locations, or users
- As you adopt cloud, AI, and distributed technologies
- As threats become more sophisticated
This means regularly revisiting your incident response plan, updating tools, and expanding capabilities. What works for a single site may not work across multiple locations or global operations.
Scalability also includes the ability to bring in external experts when needed, without disrupting internal coordination.
Turn Every Incident Into Improvement
The most effective incident response teams treat incidents as learning opportunities. After every incident:
- Conduct detailed post-incident reviews
- Analyze timelines, decisions, and outcomes
- Identify gaps in detection, communication, or execution
But most importantly, act on those insights.
Update playbooks, improve workflows, refine alerting systems, and adjust team responsibilities where needed. Share learnings across teams so improvements are not isolated.
Over time, this creates a feedback loop where each incident strengthens your response capability, making the team faster, more coordinated, and more resilient.
How Technology Empowers Incident Response Teams
In most organizations, the challenge is not capability but a lack of clarity in the moment.
Something goes wrong. Alerts start coming in. People jump into action. But without the right visibility, teams spend valuable time figuring out what actually happened instead of responding to it.
This is where modern technology changes how an incident response team operates.
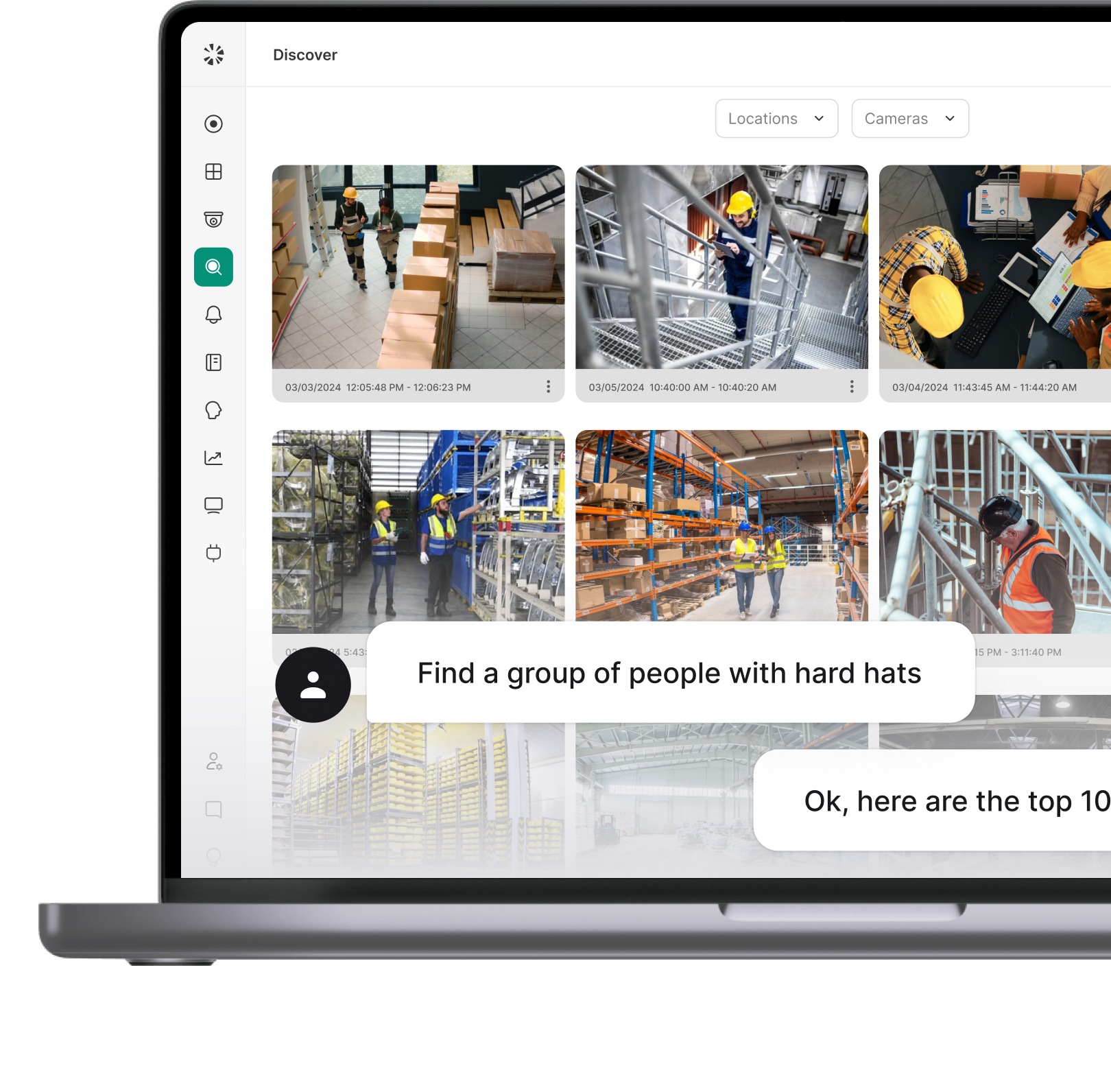
Instead of reacting with limited information, teams can now see events as they unfold. For example, with AI-driven video and system intelligence, like what Coram enables, teams can instantly search footage, identify specific events, and track movement across cameras without manually reviewing hours of data.
Think about a real scenario:
An unauthorized individual enters a restricted area. Traditionally, someone would review footage after the fact, piece together timelines, and then act. With the right technology, the incident response team can:
- Get alerted in real time
- Identify the person or event instantly
- Track their movement across locations
- Take action while the situation is still active
That shift from delayed reaction to real-time awareness is what makes the biggest difference.
Technology also reduces the dependency on manual processes. Instead of teams constantly monitoring screens or digging through logs, intelligent systems surface what matters. Alerts become more meaningful, investigations become faster, and decisions become more confident.
Another important aspect is centralization. When incidents involve multiple locations or systems, having everything in one place (alerts, footage, and system activity) helps teams stay aligned. The incident response team doesn't waste time switching between tools or coordinating across fragmented systems.
There's also a growing overlap between security and operations. Tools like Coram don't just detect threats; they help identify inefficiencies, unusual patterns, or operational risks. This means teams can act before issues escalate, not just after.
And importantly, this technology is designed to work with existing infrastructure. It doesn't require starting from scratch. Teams can layer intelligence on top of what they already have, making adoption faster and less disruptive.
At its core, technology doesn't replace an incident response team. It supports it. It gives teams:
- Faster awareness
- Better context
- Less manual effort
- More confidence in decisions
During an incident, the biggest advantage isn't just having a team; it's giving that team the ability to see clearly and act immediately.
Conclusion
An incident response team is essential for any organization operating in today's complex, always-on environment. It provides speed, structure, and coordination during incidents, reducing impact, costs, and confusion.
At its core, an incident response team works through:
- Preparation: building plans, roles, and readiness
- Detection and Triage: identifying and prioritizing incidents quickly
- Containment and Mitigation: limiting damage and stabilizing systems
- Recovery: restoring operations safely and efficiently
- Post-Incident Review: learning and improving continuously
How an incident response team works comes down to clear roles, real-time coordination, and fast decision-making under pressure.
Technology further strengthens this capability. Platforms like Coram enable real-time visibility, faster detection, and smarter responses, helping teams act with clarity rather than guesswork.
In the end, it's not about avoiding incidents; it's about being ready when they happen.
FAQ
An incident response team handles security, system, and operational incidents with structured coordination. An emergency response team focuses on immediate physical emergencies like fire, medical issues, or evacuation.
Incident response is about handling the event itself: detecting, containing, and recovering from it. Crisis management is broader and focuses on business impact, including communication with stakeholders, reputation management, and long-term decision-making. In simple terms, incident response fixes the problem; crisis management handles the fallout.
Yes, regardless of size. As systems become more connected, even small disruptions can have significant impact. A formal incident response team ensures there's structure, accountability, and faster response when incidents occur, rather than relying on ad-hoc efforts that can lead to delays and confusion.
A physical security incident response team typically handles:
- Unauthorized access or trespassing
- Theft, vandalism, or property damage
- Suspicious behavior or unidentified individuals
- Workplace safety violations or compliance risks
- Crowd management and overcrowding situations
- Vehicle-related incidents (unauthorized entry, tracking)
- Real-time alerts from surveillance and access systems