Every business has something worth protecting. People, property, data, reputation. Corporate security is the discipline that keeps all of it intact.
For most organizations, the question is not whether they need security. It is whether the security they have actually matches the threats they face. A propped door in a warehouse. Tailgating at an office lobby. A terminated employee whose badge still works. These are not edge cases. They are daily operational realities.
This guide covers corporate security from the ground up: what it means, why it matters, the core components, common threats, and how modern technology is changing how organizations protect themselves.
TL;DR
- Corporate security protects an organization's people, physical assets, information, and operations from internal and external threats
- The four pillars are physical security, cybersecurity, personnel security, and crisis management
- Common threats include unauthorized access, theft, workplace violence, cyber attacks, and insider threats
- Effective programs combine clear policies, trained personnel, and integrated technology
- AI-powered video surveillance and access control integration compress detection and response times significantly
What is Corporate Security?
Corporate security is the function responsible for protecting an organization's employees, physical assets, intellectual property, and business operations. It spans everything from the locks on the doors to the policies that govern who can access what, when, and under what conditions.
The term often gets confused with cybersecurity. They overlap, but they are not the same thing. Cybersecurity protects digital systems and data. Corporate security covers the full scope: physical spaces, people, information, and the operational continuity that ties them together.
A corporate security program typically includes:
- Physical security: Access control, surveillance, guards, and perimeter protection
- Information security: Data protection, intellectual property safeguards, and compliance
- Personnel security: Background checks, insider threat programs, and employee training
- Crisis management: Emergency response, business continuity, and disaster recovery
The goal is not zero risk. That does not exist. The goal is a security posture that matches your threat landscape and keeps your organization operational when something goes wrong.
Why Corporate Security Matters
Security incidents carry real costs. A single unauthorized access event can result in stolen equipment, compromised data, legal liability, or worse. Workplace violence incidents affect employee safety and organizational trust. Data breaches trigger regulatory penalties and reputational damage that can take years to recover from.
Consider the operational impact across different environments:
Corporate security is not a cost center that exists in isolation. It directly affects operational continuity, regulatory compliance, employee retention, and brand reputation.
Key Components of Corporate Security
A complete corporate security program covers four domains. Most organizations have some coverage in each area. The question is whether those pieces work together.
Physical Security
Physical security is the most visible layer. It includes everything that controls or monitors access to your physical spaces.
Access control systems determine who can enter which areas and when. Badge readers, biometric scanners, PIN pads, and mobile credentials all fall here. The access control system also generates the log data that tells you who was where at what time.
Video surveillance provides visual monitoring and a forensic record. Traditional systems record footage. Modern AI-powered platforms do more: they detect anomalies, flag suspicious behavior, and make footage searchable in seconds rather than hours.
Security personnel handle physical response, visitor management, and human judgment calls that technology cannot make. Guards, patrols, and reception staff all contribute.
Perimeter security includes fencing, lighting, barriers, and environmental design that makes unauthorized access harder before anyone reaches a door.
The shift in physical security over the past decade has been from passive recording to active detection. A camera that records footage is useful after an incident. A camera that alerts you to tailgating as it happens is useful during one.
Cybersecurity
Cybersecurity protects digital systems, networks, and data. In most organizations, it operates as a separate function, but the overlap with corporate security is significant.
Core elements include:
- Network security: Firewalls, intrusion detection, segmentation
- Endpoint protection: Antivirus, device management, patch management
- Identity and access management: User authentication, privilege controls, single sign-on
- Data protection: Encryption, backup, data loss prevention
- Security awareness training: Phishing simulations, policy education, incident reporting
The physical and digital domains increasingly intersect. An access control system is a network-connected device. A surveillance camera is an IP endpoint. A compromised credential can unlock a door as easily as a database.
Personnel Security
People are both an asset and a vulnerability. Personnel security manages that reality.
Background checks verify identity, criminal history, and employment claims before someone gains access to your organization. The depth of screening typically scales with the sensitivity of the role.
Insider threat programs monitor for behavioral indicators that suggest an employee may be a risk. This includes access pattern anomalies, policy violations, and warning signs that emerge over time.
Training and awareness ensure employees know what is expected of them and how to recognize threats. Phishing awareness, access policy training, and incident reporting procedures all fall here.
Visitor management controls who enters your facility, tracks where they go, and ensures they leave.
Crisis Management and Business Continuity
When something goes wrong, the question is whether your organization has a plan or whether it improvises.
Emergency response planning defines what happens during an active incident: who responds, in what order, through what channels. This includes evacuation procedures, lockdown protocols, and communication trees.
Business continuity planning addresses how operations resume after a disruption. Which systems are critical? What are the recovery priorities? How long can each function be offline?
Incident management covers the full lifecycle: detection, containment, communication, evidence preservation, recovery, and post-incident review.
Organizations that handle crises well are not lucky. They planned for them.
Common Corporate Security Threats
Your security program should be built around the threats most likely to affect your environment. These vary by industry, location, and operational model, but several categories appear consistently.
Unauthorized Access and Intrusion
This is the most common category across every environment. It includes tailgating through controlled doors, credential misuse, forced entry, and visitors moving beyond permitted areas.
In many cases, unauthorized access is not malicious. An employee holds a door for a stranger out of politeness. A visitor wanders off the planned route. A badge that should have been deactivated still works.
The challenge is that unauthorized access often looks normal until it does not. Detection depends on access logs, video analytics, and the situational awareness of your staff.
Theft and Vandalism
Equipment theft, inventory shrinkage, and property damage affect organizations across every sector. Internal theft is often harder to detect than external intrusion because the person responsible already has legitimate access.
After-hours intrusions, loading dock vulnerabilities, and unsecured storage areas are common weak points. Detection often depends on video surveillance, access logs, and inventory controls working together.
Workplace Violence
Workplace violence ranges from verbal threats to physical altercations to active shooter situations. These incidents demand the fastest response and carry the highest stakes.
Prevention involves multiple layers: threat assessment, behavioral monitoring, employee training, and physical controls that limit access to sensitive areas. Response involves clear protocols, immediate communication, and coordination with law enforcement.
Cyber Attacks
Ransomware, phishing, credential theft, and network intrusion affect organizations of every size. The attack surface has expanded as more devices connect to corporate networks and more employees work remotely.
The intersection with physical security is increasingly relevant. A phishing attack that compromises access control credentials creates a physical security problem. A camera system with default passwords is a network entry point.
Insider Threats
Insider threats involve employees, contractors, or partners who misuse their legitimate access. Motivations vary: financial gain, personal grievance, external coercion, or simple carelessness.
Detection depends on behavioral monitoring, access pattern analysis, and the ability to correlate activity across systems. A single unusual event may mean nothing. A pattern of unusual events often means something.
Environmental and Safety Incidents
Fire, flooding, power failure, and severe weather all require a coordinated response. These are not security threats in the traditional sense, but they affect the same systems: access control, surveillance, communication, and emergency response.
Natural disasters and infrastructure failures also create opportunities for opportunistic crime. Security coverage should account for these scenarios.
Corporate Security Roles and Responsibilities
A corporate security program needs clear ownership. Roles vary by organization size, but the structure typically includes:
Chief Security Officer (CSO) or Director of Security: Owns the overall security program, sets strategy, manages budget, and reports to executive leadership.
Security Managers: Handle day-to-day operations, supervise personnel, coordinate with facilities and IT, and manage vendor relationships.
Security Officers and Guards: Provide physical presence, handle access control, respond to incidents, and manage visitor flow.
Security Analysts: Monitor systems, investigate incidents, analyze access data, and identify vulnerabilities.
IT Security Team: Manages cybersecurity controls, network security, and the technology infrastructure that physical security systems depend on.
Effective security requires cross-functional collaboration. HR handles background checks and terminations. Legal advises on compliance and liability. Facilities manages building access and physical infrastructure. No single team owns every piece.
Building a Corporate Security Program
A corporate security program is not a product you buy. It is a capability you build. The process follows a consistent pattern regardless of organization size.
Step 1: Conduct a Risk Assessment
Start by documenting your assets, threats, and current controls. The questions that drive this step:
- Which areas, if compromised, would directly affect safety or operations?
- Which entry points are unmonitored or unlogged?
- What incidents have occurred at your location or in your industry?
- Where do your current controls fall short?
The output is a prioritized list of risks ranked by likelihood and impact. This becomes the foundation your program builds from.
Step 2: Develop Security Policies
Policies define expectations and accountability. Core policies typically include:
- Access control policies: Who can access which areas, under what conditions
- Visitor management: Check-in procedures, escort requirements, badge tracking
- Incident response: Reporting channels, escalation paths, evidence preservation
- Acceptable use: Rules for credentials, devices, and sensitive areas
Policies are only useful if people know them and follow them. Training and enforcement are part of the program, not afterthoughts.
Step 3: Implement Security Measures
With risks identified and policies defined, implementation covers the technology, personnel, and processes that execute the program.
Physical controls: Access control systems, surveillance cameras, locks, barriers, lighting
Personnel: Security officers, reception staff, monitoring personnel
Technology: Video management systems, access control platforms, alert systems, integration layers
The goal is layered defense. No single control stops every threat. Multiple controls working together create a security posture that is harder to defeat.
Step 4: Train Employees
Security is not just a security team responsibility. Every employee is part of the program.
Training should cover:
- Access policies and credential handling
- Visitor procedures
- Incident reporting
- Emergency response and evacuation
- Social engineering awareness
Regular refreshers and tabletop exercises turn written procedures into practiced behavior.
Step 5: Monitor, Audit, and Improve
A security program is never finished. Continuous monitoring identifies incidents as they occur. Regular audits verify that controls are working as intended. Post-incident reviews capture lessons learned.
Review your risk assessment annually, or whenever your facility, staffing, or operations change significantly.
The Role of Technology in Modern Corporate Security
Technology does not replace security fundamentals. It accelerates them. The difference between a response that contains an incident and one that misses it often comes down to what your systems detected, how fast that information reached the right person, and how much context was available when decisions had to be made.
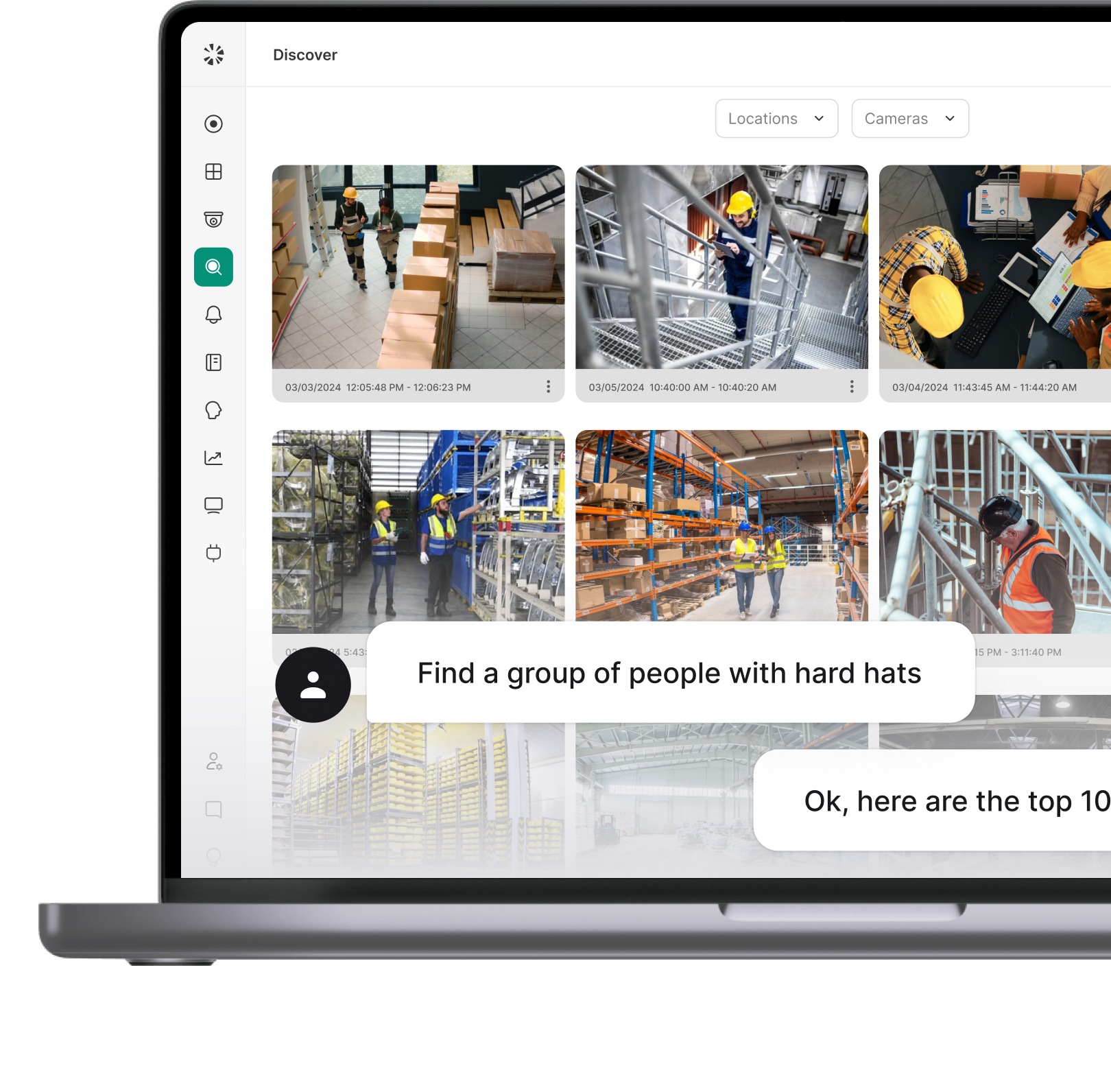
AI-Powered Video Security
Traditional camera systems record footage. AI-powered video security actively monitors it. That distinction matters because detection becomes automatic rather than dependent on someone watching a screen at the right moment.
Modern platforms handle detection across the scenarios your security program is built around:
- Unauthorized access attempts and tailgating at controlled entry points
- Weapon detection with real-time alerts before a situation escalates
- After-hours motion in restricted areas triggering immediate notification
- AI-powered search that pulls relevant footage in seconds during an active response
For incident response, this means faster detection, faster containment decisions, and a cleaner evidence trail.
Integrated Access Control
Access control systems generate a precise record of every entry and exit event across your facility. During an incident, that data answers the questions your team needs answered immediately:
When access control integrates with video security, every door event connects directly to the corresponding footage. During an active incident, your team sees the access event, the credential that triggered it, and the camera feed from that exact entry point, all without switching systems.
Real-Time Alerts and Automated Notifications
Your response procedures are only as fast as your alerting infrastructure. Define the triggers, and the system handles the escalation:
- A door held open beyond a set threshold alerts the response lead
- A camera detecting motion in a restricted area after hours notifies security immediately
- An access attempt using a revoked credential flags automatically before anyone reaches a screen
For facilities managing multiple locations, automated alerts are what make consistent response times achievable across every site without adding headcount.
Centralized Incident Logging
Every action taken during a response needs to be logged, timestamped, and retrievable from one place. A centralized platform captures:
- Access events and credential activity for the incident window
- Camera footage linked to specific door and alert events
- Alert history showing what triggered, when, and who was notified
- Response actions documented in sequence for post-incident review
This record supports compliance audits, insurance documentation, legal proceedings, and the lessons-learned review your team conducts after every incident closes.
Corporate Security Best Practices
Organizations that maintain effective security programs share common practices:
Adopt a layered approach. No single control stops every threat. Combine physical barriers, access controls, surveillance, personnel, and policies so that defeating one layer does not defeat the entire program.
Integrate physical and cyber security. The teams may be separate, but the threats overlap. Access control systems, cameras, and building management systems are all network-connected devices that require both physical and cyber protection.
Prioritize employee training. Technology and policies are only effective if people follow them. Regular training, clear communication, and visible enforcement build the security culture that underpins everything else.
Leverage AI for proactive detection. Waiting for someone to review footage after an incident is reactive. AI-powered analytics detect anomalies as they happen and compress the gap between detection and response.
Test and update incident response plans. A plan that has never been tested is a plan that will fail under pressure. Tabletop exercises, drills, and post-incident reviews turn written procedures into operational capability.
Review and adapt regularly. Threats evolve. Your facility changes. Your workforce changes. The security program needs to change with them.
When Your Security Program Is the Difference
A corporate security program gives your organization the one thing that matters most when something goes wrong: a response already planned.
The organizations that handle incidents well did not figure it out during the incident. They built the structure before it happened, tested it, and backed it with technology that made detection and response faster at every step.
Coram is built for exactly that environment. From AI-powered threat detection and real-time alerts to unified access control and incident logging, the platform gives security teams the visibility and speed that their security program depends on.
If you are ready to see how it works across your doors, cameras, and locations, book a demo today.
FAQ
Corporate security protects an organization's people, physical assets, information, and operations from threats. This includes managing access control, video surveillance, security personnel, incident response, and coordination with law enforcement when necessary.
Cybersecurity focuses specifically on protecting digital systems, networks, and data. Corporate security covers the full scope: physical security, personnel security, information security, and crisis management. In practice, the two functions overlap significantly and often work together.
A corporate security officer is a member of the security team responsible for on-the-ground security operations. Duties typically include access control, surveillance monitoring, visitor management, incident response, and patrolling facilities. Senior roles may include threat assessment, program management, and executive protection.
Technology accelerates detection and response. AI-powered video analytics flag anomalies in real time rather than requiring manual review. Integrated access control links door events to camera footage. Automated alerts ensure the right people are notified immediately. Centralized logging supports incident investigation and compliance.