Large enterprises, school districts, logistics networks, and retail chains are deploying cameras at a pace that would have been unthinkable a decade ago. A mid-sized retail chain might run 2,000 cameras across 80 stores.
A regional school district might manage 500 endpoints across 30 campuses. Warehousing and logistics operations are pushing those numbers higher still, with some facilities running hundreds of cameras inside a single building.
The infrastructure is scaling. The underlying architecture, in most cases, is not.
Most of these organizations built their surveillance stack on closed ecosystems: proprietary cameras that only talk to one VMS software that requires a specific vendor's hardware, cloud platforms that bundle everything together and call it simplicity. At one site, that bundling feels like a feature. Across dozens, it starts to feel like a trap.
The problem isn't that closed systems are poorly built. Many of them work exactly as designed. The problem is what they were designed for and what happens when your operational reality outgrows that design.
This article breaks down the five specific points where closed surveillance ecosystems fracture under scale, what that costs organizations in real operational terms, and what a more durable infrastructure model actually looks like.
TL;DR
- Closed surveillance ecosystems are architecturally designed for simplicity at one site, with no resilience built in for distributed scale
- Hardware lock-in means every expansion is a purchasing decision made in advance by the vendor
- Storage, bandwidth, and egress costs compound unpredictably as camera counts and site counts grow
- Multi-site management becomes operationally unworkable when each location runs as its own disconnected instance
- AI capabilities, integrations, and upgrades are gated behind a single vendor's engineering priorities and release cycles
- Switching costs accumulate across every layer; the longer an organization stays, the more leverage shifts to the vendor
What Makes a Surveillance Ecosystem "Closed"
A closed surveillance ecosystem is one where a single vendor controls every layer: hardware, software, storage, and analytics. The architecture is designed to keep all components inside a walled garden, simple to deploy initially, increasingly rigid as operational demands grow.
The defining characteristics:
- Vertically integrated hardware and software: Cameras only function properly within the vendor's own VMS and cloud infrastructure. They communicate through proprietary protocols rather than open standards like ONVIF or RTSP, making third-party connections structurally impossible.
- No meaningful third-party support: Existing cameras from other manufacturers cannot be added to the ecosystem. Every new site or expansion requires purchasing from the same vendor.
- Restricted API access: Custom integrations with access control, HR systems, or incident management platforms require vendor involvement. Independent workflow development is either blocked or impractical.
- Subscription-dependent intelligence: AI features, search, analytics, and in some cases recording storage, are cloud-hosted and vendor-controlled. When a subscription lapses, those capabilities go with it.
- Proprietary protocols over open standards: Without ONVIF or RTSP support, the system cannot communicate with the broader infrastructure stack an organization already runs.
These properties create a coherent product experience at one site. Across many, they become the source of every scaling problem covered in the sections ahead.
The Five Ways Closed Ecosystems Break Down at Scale
Closed ecosystems don't fail dramatically. They degrade gradually, one constraint at a time, until the cost of staying becomes harder to justify than the cost of leaving.
Fracture Point 1: Hardware Lock-In Turns Every Expansion Into a Rip-and-Replace
Every new site is a purchasing decision made for you in advance.
Proprietary protocols mean adding a location requires buying the same vendor's hardware, regardless of what you already have on-site. Standards-compliant cameras from Axis, Hanwha, or Bosch get written off because the ecosystem won't recognize them. When a camera model is discontinued, every site tied to that hardware faces an unplanned upgrade cycle.
For 5 sites, manageable. For 50, every expansion budget conversation becomes a negotiation with a vendor who already has you locked in.
Fracture Point 2: Storage and Bandwidth Costs Compound Unpredictably
Cloud-first architecture prices storage per camera, per retention period, with no flexibility to route high-volume feeds to cheaper local storage. Continuous upstream transmission from dozens of sites strains network infrastructure. Retrieving footage for investigations adds egress fees on top.
At 30 sites running 4K feeds, you're no longer paying for security. You're subsidizing an infrastructure model built around the vendor's recurring revenue.
Fracture Point 3: Multi-Site Management Becomes a Patchwork of Disconnected
A security director managing 40 locations across three states shouldn't need to log into four platforms to understand what happened at one door. But that's the operational reality closed ecosystems produce.
Here's what that actually looks like day-to-day:
The root cause is architectural. Closed platforms provision each site as its own instance, with its own configuration and its own data silo. At 30 sites, security teams spend more time managing the system than using it.
Fracture Point 4: Innovation Stalls Because You're Locked to One Vendor's Roadmap
Every capability your security infrastructure will ever have is decided by a single vendor's engineering priorities.
When weapon detection, behavioral analytics, or license plate recognition become operationally relevant, adoption depends on whether your vendor has built them and whether they're included in your subscription tier.
The pace of video AI development has accelerated sharply; organizations on open infrastructure deploy best-in-class analytics independently. Organizations inside closed ecosystems wait.
Fracture Point 5: Switching Costs Become a Trap
By the time an organization realizes a closed ecosystem isn't working at scale, leaving is expensive enough to make staying feel rational.
Proprietary hardware has no resale value outside the ecosystem. Footage isn't portable. Configurations, access rules, and audit logs don't export cleanly. Renewal conversations happen in the shadow of migration cost, not platform merit.
Organizations that recognize this early share one move: they shift toward open, standards-based infrastructure before the switching costs become the deciding factor.
What Organizations Give Up Inside a Closed Ecosystem?
The losses aren't uniform. They hit different roles at different points in the scaling journey.
The Security Director Loses cross-site visibility first. Incidents that span multiple locations require manual correlation across disconnected dashboards.
Investigation time stretches from minutes to hours. When a new AI capability becomes operationally relevant, such as weapon detection or behavioral analytics, adoption depends on the vendor's timeline, instead of the threat landscape.
The CIO / IT Infrastructure Leader Inherits a network architecture built around the vendor's cloud requirements, not the organization's bandwidth constraints. Storage costs scale with camera count and retention policy, with no flexibility to route feeds to cheaper local or hybrid storage.
Every integration with identity management, HR, or incident response platforms requires vendor involvement, slowing down IT roadmaps that have nothing to do with surveillance.
The Multi-Site Operator Faces the most compounding friction. Expansion means hardware decisions made in advance by the vendor ecosystem. Legacy cameras at older sites can't be brought into the platform.
Each new location adds another configuration layer, another provisioning cycle, another set of permissions to manage in isolation. The operational overhead grows faster than the site count.
Across all three, the common thread is the same: the organization absorbs the cost of an architecture it didn't fully understand at procurement, and pays that cost repeatedly as the environment scales.
What the Alternative Looks Like?
The shift happening across enterprise security infrastructure right now isn't a product upgrade. It's an architectural one.
Organizations moving away from closed ecosystems aren't simply switching vendors. They're adopting a fundamentally different design philosophy: one where hardware, software, storage, and AI are decoupled layers that can be evaluated, replaced, or upgraded independently.
The characteristics of that architecture are specific:
- Camera-agnostic platforms that support ONVIF and RTSP, allowing organizations to connect existing hardware from any standards-compliant manufacturer without a rip-and-replace cycle
- Edge and hybrid storage that routes footage intelligently, keeping high-volume feeds local and pushing only relevant clips to the cloud, reducing bandwidth and storage costs at scale
- Open APIs that connect surveillance data to access control, identity management, HR, and incident response platforms without vendor gatekeeping
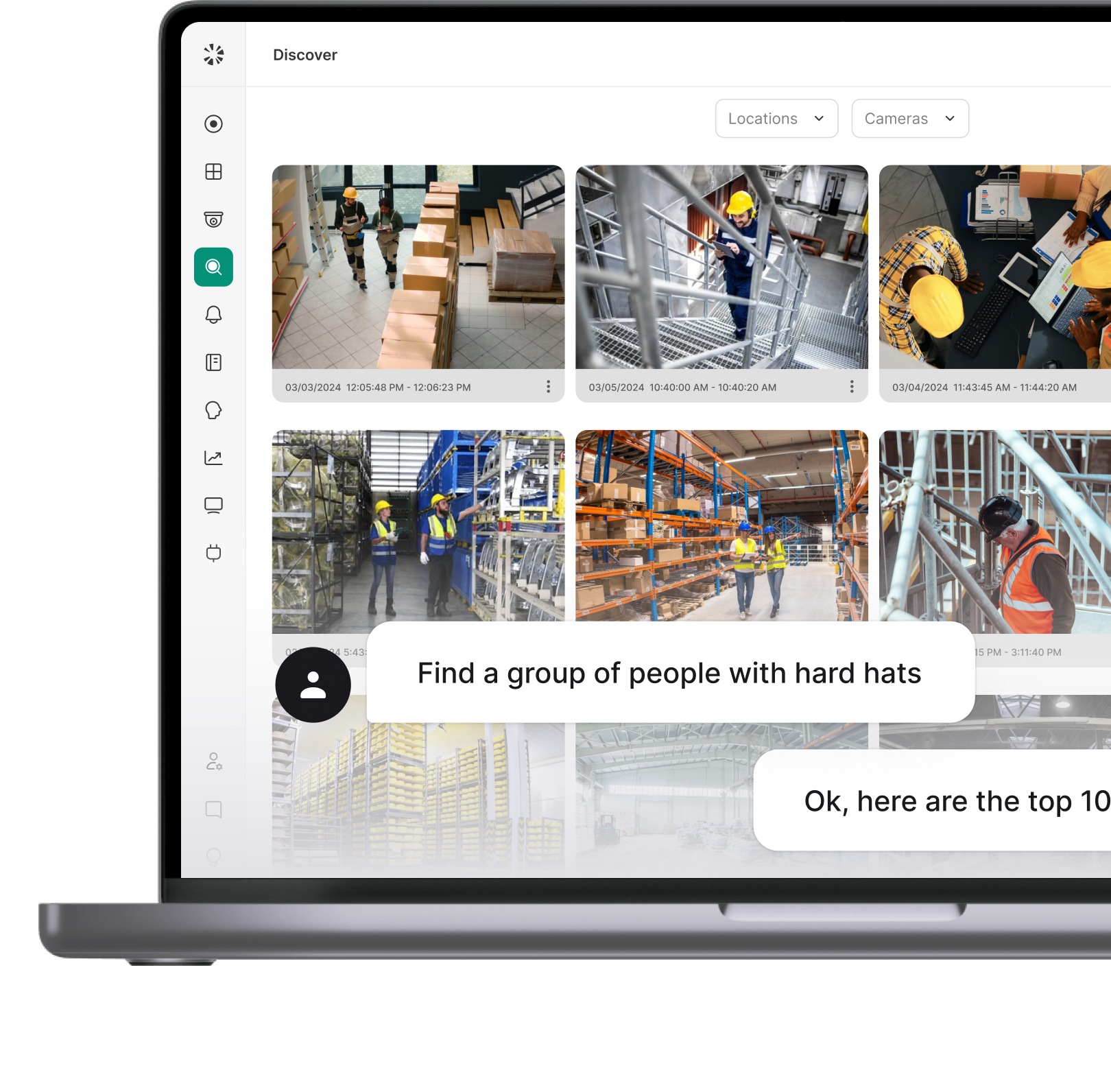
- AI that runs across hardware, delivering object detection, search, and behavioral analytics regardless of which manufacturer's camera captured the footage
- Unified multi-site management that centralizes access policies, alert configurations, and footage search across every location in a single dashboard
Coram was built around this architecture. It connects to third-party cameras from Axis, Hanwha, Bosch, and others through ONVIF and RTSP. AI analytics, including weapon detection, license plate recognition, and natural language video search, run across any connected hardware stream. Access control, video, and emergency management sit inside one platform rather than three separate vendor relationships.
The local system continues functioning independently of cloud connectivity. When a subscription lapses, hardware access and basic operations remain intact, removing the leverage that closed ecosystems use to enforce renewal.
For organizations managing distributed infrastructure at scale, that's not a feature list. It's the foundation that makes everything else manageable.
How to Tell If Your Current System Will Break at Scale?
Most organizations don't discover their surveillance architecture has a scaling problem during a procurement review. They discover it during a budget conversation, an incident investigation, or an expansion project that suddenly costs twice what it should.
These are the signals worth paying attention to before that moment arrives.
If three or more of these are recognizable, the architecture is already constraining operations. The question at that point isn't whether the system will break at scale; it's how much scale is left before it does.
The Architecture Decision That Can't Wait
Closed surveillance ecosystems don't announce their limits. They reveal them through budget overruns, investigation delays, expansion friction, and renewal conversations that feel more like hostage negotiations than vendor partnerships.
The organizations feeling that friction aren't running bad security programs. They're running good programs on infrastructure that was never designed for the scale they've reached.
The shift toward open, AI-native surveillance architecture is happening now, across enterprise, education, logistics, and multi-site retail, driven by security leaders who recognized that the architecture underneath their system matters as much as the features on top of it.
The decision point is whether to modernize before the switching costs make the choice for you.
Coram brings video security, access control, and AI intelligence into a single open platform, built to connect with existing hardware, scale across every location, and keep control with your team.
FAQ
A closed surveillance platform bundles hardware, software, storage, and analytics under a single vendor's control. Components only function within that vendor's ecosystem, and integration with third-party systems is restricted or impractical.
An open platform separates these layers, supporting industry standards like ONVIF and RTSP, allowing organizations to connect hardware from multiple manufacturers, integrate with external systems through open APIs, and operate independently of any single vendor's roadmap.
Vendor lock-in occurs when the architecture of a system makes switching providers prohibitively expensive. In physical security, this means proprietary cameras with no resale value outside the ecosystem, footage stored in formats that don't transfer to other platforms, configurations that can't be exported, and integrations that require rebuilding from scratch. The longer an organization stays inside a closed ecosystem, the higher the accumulated switching cost becomes.
Several operational signals indicate a closed ecosystem: adding new sites requires purchasing the same vendor's hardware, existing cameras from other manufacturers cannot connect to the platform, AI features stop functioning when a subscription lapses, API integrations require vendor professional services, and investigation workflows span multiple disconnected dashboards.
If three or more of these are familiar, the architecture is already constraining operations.
An open platform in video surveillance supports industry-standard protocols like ONVIF and RTSP, allowing cameras from any compliant manufacturer to connect. It provides documented API access for custom integrations, supports edge and hybrid storage alongside cloud, and runs AI analytics across third-party hardware streams.
Critically, core system functionality remains intact independent of cloud connectivity or subscription status.
Proprietary hardware uses vendor-specific communication protocols, firmware, and encoding formats that only function within that vendor's ecosystem. Standards-based hardware uses open protocols like ONVIF and RTSP, allowing it to connect to any compatible VMS or platform.
The practical difference at scale is significant: standards-based hardware preserves existing infrastructure investments, supports multi-vendor environments, and gives organizations flexibility to change software platforms without replacing physical devices.




.webp)