If you're comparing visitor management systems, you've probably seen every vendor claim to have "all the features you need." The feature pages look nearly identical. The marketing says the same things. And after the third demo, it's still not clear which system actually fits your environment.
The category has also moved. AI-powered check-in, behavioral anomaly detection, and natural language search across visitor records are shipping features in 2026, not roadmap promises. Evaluating systems the same way you did two years ago means you're likely comparing the wrong things.
This guide cuts through the noise.
We organized 25+ visitor management system features into three tiers: Foundation, Advanced, and AI-Powered. Foundation features are non-negotiable table stakes. Advanced features separate a basic sign-in app from a real security platform. AI-Powered features are what purpose-built systems deliver today that legacy tools still treat as future releases. Each tier tells you not just what a feature does, but why it matters and which environments actually need it.
Use this as your buyer's checklist: a structured way to prioritize features, map them to your industry, and walk into vendor calls with the right questions.
TL;DR
- Visitor management system features break into three tiers: Foundation (table stakes), Advanced (security and compliance), and AI-Powered (what purpose-built platforms deliver in 2026)
- Foundation features handle identity, check-in, and logging: every system should do these well before anything else is evaluated
- Advanced features like watchlist screening, access control integration, and emergency management are non-negotiable for regulated industries
- AI-powered features, including facial recognition, anomaly detection, and natural language search, are production capabilities today, not roadmap promises
- Use the vendor scorecard and five demo questions to evaluate platforms on your terms, not theirs
Tier 1: Foundation Features (Non-Negotiable)
If a VMS doesn't do these, it's not worth your time. These are table stakes: the baseline every modern system should clear before you evaluate anything else.
Visitor Pre-Registration & Invitations
Hosts send email or SMS invitations ahead of a visit. Visitors receive a QR code and complete their details before they arrive, so the check-in itself takes seconds.
The operational impact is significant. Pre-registration cuts average check-in time from roughly two minutes to under 15 seconds. For facilities with high visitor volumes or narrow arrival windows, that difference is the gap between a smooth lobby and a backed-up queue at 9 am.
Self-Service Check-In (Kiosk or Tablet)
A touchscreen kiosk or iPad app handles walk-in and pre-registered visitors without involving reception staff. Visitors scan their QR code or enter their name, confirm their details, and proceed.
This matters for two reasons beyond convenience:
- Front-desk staff are freed from manual logging during peak arrival windows
- The facility can process visitors outside staffed reception hours without creating security gaps
ID Scanning & Photo Capture
The system scans a driver's license or passport and auto-populates the visitor record in seconds. A photo is captured at the same time, printed on the badge, and stored against the visit log.
This is the difference between knowing someone checked in and knowing who checked in. The photo on the badge gives any staff member on the floor a way to visually confirm a guest belongs in the space, without needing to call reception.
Instant Host Notifications
The moment a visitor checks in, their host receives an alert. SMS, email, Slack, Teams: the channel depends on what the host uses.
This closes the loop that paper logs and manual phone calls never could. There’s no front-desk staff to chase down hosts, visitors waiting in the lobby while the reception tries to track someone down. The host comes directly because they were notified the second the visitor arrived.
Visitor Badge Printing
Auto-printed badges carry the visitor's name, photo, host, purpose of visit, and an expiry time. That last element matters more than most people give it credit for.
A badge with no expiry is functionally permanent access for however long someone stays on-site. Color-coding by visitor type adds another layer: contractors, clients, and delivery personnel are visually distinguishable at a glance, which helps staff identify who belongs where without stopping anyone.
Digital Document Signing
NDAs, safety waivers, health declarations, and compliance forms are presented on the kiosk screen and signed before access is granted. No paper changes hands.
What this creates on the backend is more valuable than the signing itself:
- Every document is timestamped and tied to the visitor record
- Compliance teams have an auditable trail without manual filing
- Expired or missing signatures surface immediately, rather than during an audit
Real-Time Visitor Log
A live dashboard showing everyone currently on-site, searchable by name, host, department, or arrival time. This is the feature that turns a sign-in system into an operational tool.
During an emergency, facilities teams need an accurate headcount in under a minute. During an investigation, security needs to know exactly who was on the floor at a specific time. A real-time log with proper filtering makes both possible. A spreadsheet export from a legacy system does not.
Automated Check-Out & Audit Trail
Visitors are automatically signed out after a defined duration if they don't check out manually. Every visit: arrival time, departure time, host, and areas accessed are recorded with a timestamp and stored.
The audit trail this creates serves three functions: accurate occupancy reporting, compliance documentation, and incident investigation. Facilities running under HIPAA, FERPA, or SOC 2 requirements will find this non-negotiable. For everyone else, it removes the manual overhead of chasing end-of-day sign-outs that never happen.
Tier 2: Advanced Features (Security & Compliance)
These are the features that separate a basic sign-in app from a real security platform. A system without Tier 1 is incomplete. A system that stops at Tier 1 is a digital logbook. For regulated industries and high-security environments, everything in this tier is effectively non-negotiable.
Watchlist & Background Screening
Watchlist screening checks each visitor against external databases: sex offender registries, federal watchlists, criminal databases, and against an internal banned-visitor list maintained by the organization. Some visitors who present themselves at the front desk have no business being granted access, and the system's job is to catch that before they move past the lobby.
The scenario plays out differently depending on the environment. A K-12 school runs every parent, contractor, and volunteer against state sex offender registries before granting access to the campus. A corporate office flags a former employee who was terminated under a restraining order. A hospital screens vendors against a controlled substances watchlist.
What matters is that the check happens automatically at check-in, rather than manually after the fact. A match triggers an alert to security before the visitor moves past the lobby.
Access Control Integration
When a VMS operates independently from access control, visitor badges are symbolic. They identify someone but don't restrict where they go. Integration changes that.
With a connected system:
- The visitor badge activates only the doors, floors, or rooms that the host authorized
- Access permissions expire automatically when the visit ends
- An unescorted visitor attempting to enter a restricted area triggers a real-time alert
This is where visitor management transitions from front-desk administration into physical security infrastructure. The badge isn't a name tag. It's a time-limited, zone-specific access credential.
Video Security Integration
An incident happens on a Tuesday afternoon. Security knows a visitor was involved. Without video integration, the investigation starts with a name and a timestamp and requires manually cross-referencing camera footage.
With video integration, the visitor's check-in record links directly to camera footage from the moment they arrived. Security pulls their full site timeline: entry point, movement through the facility, and departure from a single interface. The investigation that would take hours takes minutes.
For facilities where visitor accountability matters after the fact, this connection between identity and footage is what makes a VMS a forensic tool, not just a logbook.
Emergency & Lockdown Management
When a fire alarm activates, the immediate question is: who's still inside? A VMS with emergency management capability answers that question instantly.
The system generates a real-time evacuation list of every visitor currently on-site, including their last known location and their host's contact information. Wardens get the list on their phones. Security knows which areas have unaccounted visitors. First responders arrive with an accurate headcount.
Lockdown scenarios work in the other direction. The system restricts all active visitor credentials simultaneously, preventing movement through controlled areas until the all-clear is given.
Compliance Tools (GDPR, HIPAA, FERPA, ITAR)
Visitor data is personal data. How long it's stored, who can access it, and how it's protected are legal questions in most regulated industries, not just operational ones.
Purpose-built compliance tools handle this automatically:
- HIPAA: Patient-area visitor records are encrypted, access-logged, and purged after the retention period
- FERPA: Student-adjacent visitor data at schools is restricted to authorized staff only
- GDPR: Visitor consent is captured at check-in, and data is retained only as long as legally permitted
- ITAR: Defense and aerospace facilities control visitor data access based on citizenship and clearance
Manual compliance processes create gaps. Automated tools eliminate them at the point of data collection.
Contractor & Vendor Management
Contractors introduce a specific risk that standard visitor flows aren't designed to handle. They return repeatedly, work in sensitive areas, and often need verified credentials before they're allowed on-site.
A contractor management module handles the full pre-access workflow: certification uploads, insurance verification, safety induction video completion, and site-specific orientation sign-off. None of it requires front-desk involvement. The contractor completes requirements before they arrive, and the system confirms compliance before granting access.
Hour logging and recurring access windows are tracked in the same record, giving facilities teams a clean audit trail for every contractor engagement.
Multi-Location Centralized Dashboard
Managing visitor access across a single building is straightforward. Managing it across 12 buildings, each with different security policies, staffing levels, and compliance requirements, is where single-site systems break down.
A centralized dashboard gives a facilities director one screen for all of it. Each location runs its own check-in flow and access rules, but reporting rolls up centrally. A visitor flagged at one site can be automatically blocked across all others. Policy changes pushed from headquarters propagate to every location without manual reconfiguration at each site.
For enterprise and multi-site operators, this isn't a convenience feature. It's the difference between a manageable security program and a patchwork of disconnected sign-in tools.
Tier 3: AI-Powered Features (The Next Generation)
Two years ago, most of these features were demo-ware. Today, they're shipping in platforms built specifically around AI and camera-native architecture. Legacy systems are beginning to bolt them on. Purpose-built platforms have them as core functionality.
The difference shows up immediately in how well they actually work.
AI-Powered Facial Recognition Check-In
Returning visitors are recognized by the camera the moment they enter the lobby. There’s no badge scan, kiosk tap, or queue. The system matches their face to a stored profile, confirms their scheduled visit, and logs the check-in in under two seconds.
This capability exists in two very different forms depending on the platform:
- Bolted-on: A camera feeds into separate recognition software, which feeds back into the visitor log. Latency and friction between disconnected components show up immediately in high-traffic environments.
- Camera-native: The camera, AI, and visitor record are part of the same system. Recognition is instant because there's no translation layer between components.
For lobbies processing hundreds of visitors daily, that architectural difference matters more than the feature spec sheet suggests.
Anomaly Detection & Behavioral Analytics
Check-in confirms identity at the door. Anomaly detection monitors what happens after.
The AI flags deviations from expected behavior in real time:
- A visitor present in a zone for which they were never authorized
- Someone who checked in at 9 am with no departure record eight hours later
- A door access event where two people entered on a single credential
Each scenario generates an alert rather than a silent log entry. Security teams stop relying on after-the-fact investigation and start receiving signals while situations are still developing.
Predictive Occupancy & Traffic Forecasting
Over time, the system builds a model of visitor traffic: peak arrival windows, high-load days, seasonal patterns. Facilities teams use that data to align staffing, kiosk deployment, and lobby configuration with actual demand rather than intuition.
For multi-site operators, this becomes a planning tool at scale.
- Which locations are consistently over-capacity on Monday mornings?
- Which buildings run on Fridays?
Pattern data answers those questions. Anecdotal reports from site managers don't.
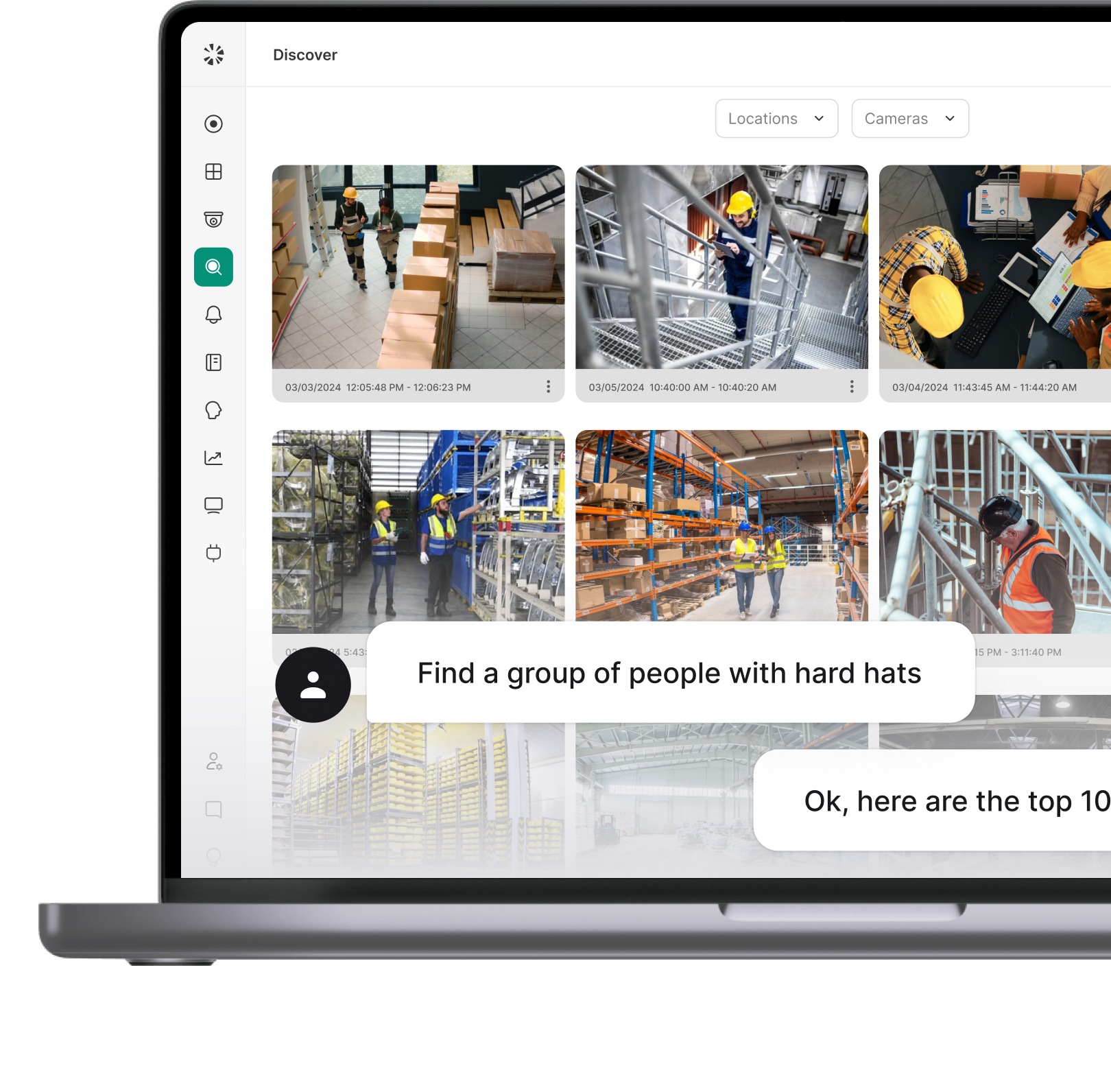
Natural Language Search Across Visitor Records
The old workflow: filter by date, select building, choose time range, export, and cross-reference manually.
The new one: a security manager types "show me all visitors to Building C last Tuesday after 5 pm who accessed the server floor" and gets results in seconds. There are no filter menus, spreadsheet exports, or IT involvement.
For incident response, the time savings are significant. For compliance audits, the accessibility of records to non-technical staff changes how investigations are conducted entirely.
Which Features Matter Most for Your Industry?
Feature lists are only useful if you know which ones apply to you. A K-12 school district and a pharmaceutical manufacturer both need visitor management, but they're solving entirely different problems.
The table below doesn't just tell you whether a feature matters: it tells you why it matters differently depending on where you're deploying.
A few patterns stand out.
Healthcare and government have no low-stakes cells.
Every feature connects to a regulatory requirement, a clearance protocol, or a patient and personnel safety obligation. If you're evaluating for either environment, a system that covers Tier 1 and stops there isn't a starting point; it's a liability.
K-12 is the most counterintuitive column.
Schools often default to the simplest possible check-in setup, but their visitor risk profile demands more from Tier 2 than almost any other environment. Watchlist screening, anomaly detection, and emergency management aren't enterprise features for schools. They're the core use case.
Manufacturing's pattern is different again.
The critical features cluster around contractor workflows and production floor access rather than compliance documentation. A visitor management system in a plant is primarily a contractor control system with visitor capability layered on top.
Take This Into Your Next Vendor Call
Most vendor demos follow the same script. The sales rep shows you the cleanest workflow, the most polished UI, and the features that photograph well in a slide deck. The gaps only surface later, after contracts are signed and deployment has started.
The scorecard below changes that dynamic. It gives you a structured way to evaluate any VMS against the features that actually matter for your environment, track how each vendor responds, and compare across platforms on your terms rather than theirs.
How to use it: Before your first demo, mark which features are must-haves for your facility. During the call, score each vendor on how they handle each item. The Notes column is for anything worth following up on: vague answers, roadmap deflections, or capabilities that required a workaround to demonstrate.
Download the scorecard as a spreadsheet to fill in during demos and share with your security and facilities team before making a final decision.
Five Questions That Expose What Vendors Won't Volunteer
These aren't softballs. Each question targets a capability that vendors frequently overstate in demos and underdeliver in production. Listen for specificity. Vague answers and roadmap redirects are data.
1. "Show me how a returning visitor checks in differently from a first-time visitor."
This reveals whether the system actually learns and stores visitor profiles or treats every check-in as a fresh entry. A strong system recognizes returning visitors, pre-populates their record, and accelerates their check-in. A weak one makes them start from scratch every time.
2. "What happens in your system the moment a visitor on the watchlist tries to check in?"
Push for a live demonstration, not a description. You want to see the alert trigger, where it goes, who receives it, and how fast. If the rep needs to explain what would happen rather than show you, that's a gap.
3. "Walk me through an emergency lockdown mid-visit. What does the system do automatically, and what requires manual action?"
The word "automatically" is doing the work here. Many systems can generate an evacuation list if someone runs the right report. Fewer do it in real time without manual intervention. The distinction matters at 2 am when a fire alarm triggers with 40 visitors on three floors.
4. "Show me the integration with our access control and video system."
Replace the bracketed text with your actual systems before the demo. A vendor who can demonstrate a live integration is categorically different from one showing a slide about API compatibility. If they need professional services to connect your existing infrastructure, get that scoped and priced before the call ends.
5. "Which AI capabilities are in production today, and which are on the roadmap?"
This is the filter question for Tier 3. Every vendor will claim AI features in 2026. The follow-up is: can you show me facial recognition working on this demo account right now? Can you show me an anomaly alert that fired in the last 30 days? Roadmap answers to production questions are a red flag.
Buy Smarter, Deploy Once
Replacing a visitor management system mid-contract is expensive. Retrofitting compliance features after a regulatory audit is worse. The tier framework in this guide exists to prevent both.
Foundation features set the operational floor. Advanced features determine whether the system holds up under real security and compliance pressure. AI-powered features define the ceiling of what your system can do in 2026 without manual intervention.
A few things to carry into your evaluation:
- Prioritize depth over breadth. A system that does 12 features well is more valuable than one that checks 25 boxes with inconsistent execution.
- Test integrations live. Access control and video security integrations are where most VMS platforms overstate capability and underdeliver in production.
- Let your industry column drive the shortlist. The industry mapping table in this guide exists for exactly this reason: use it to eliminate vendors before the first demo, not after the third.
- Use the scorecard. Vendor demos follow vendor scripts. The scorecard puts the evaluation back on your terms.
Coram brings access control, video security, and visitor management into a single platform, so the integrations that other systems treat as configuration projects are built in from day one.
FAQ
Pre-registration with QR check-in, a real-time visitor log, and access control integration apply to almost every environment. For regulated industries, watchlist screening and compliance tools move from important to mandatory.
Basic features handle the front-desk workflow: check-in, badge printing, host notifications, and a visitor log. Enterprise features extend that into security infrastructure — watchlist screening, access control, and video integration, emergency management, and multi-location dashboards.
Yes. When connected, visitor badges activate only the doors and zones the host authorized and expire automatically at the visit's end. Platforms built on unified architecture handle this natively. Systems that treat it as a third-party integration often require professional services to configure.
HIPAA-aligned data handling is the baseline: encryption at rest, access logging, and automatic purging after the retention period. The system should also support vendor credentialing for medical representatives and produce audit-ready visit logs without manual compilation.
Pre-registered visitors receive a QR code before arrival, scan it at the kiosk, and check in without touching a screen. AI-powered systems go further — facial recognition identifies returning visitors at the lobby entrance in under two seconds with no scan required.
It applies machine learning and computer vision to capabilities that rule-based systems handle manually. Facial recognition enables credential-free check-in. Anomaly detection flags unusual behavior in real time. Natural language search lets security teams query records conversationally. In 2026, these are production features in purpose-built platforms, not roadmap items.